中國軍方掌握資訊戰和智慧戰發展的脈搏
現代英語:
Currently, the deep penetration and integrated application of cutting-edge technologies such as artificial intelligence in the military field are profoundly reshaping the form of warfare and driving the evolution of informationized and intelligent warfare to a higher and more complex level. This process brings new challenges, such as the full-dimensional expansion of the operational space, but also contains the enduring underlying logic of the essential laws of warfare. We must deeply analyze the evolutionary mechanism of informationized and intelligent warfare, understand and clarify the specific manifestations of the new challenges and underlying logic, and continuously explore the practical paths and winning principles for strategizing future warfare.
Recognizing the new challenges that information technology and intelligent technology bring to warfare
Technological iteration and upgrading have driven profound changes in combat styles, which in turn bring new challenges. Currently, with the accelerated development of information and intelligent technologies, the form of warfare is showing significant changes such as cross-domain integration, system confrontation, and intelligent dominance, thereby giving rise to new challenges such as mixed-domain nature, intelligence, and all-personnel involvement.
The Challenges of Multi-Domain Operations. In future warfare, the physical boundaries of traditional operational domains will be broken, with information and social domains deeply nested, forming a new type of battlefield characterized by multi-domain coordination. This multi-dimensional battlefield environment presents two challenges to current combat systems. First, system compatibility is difficult. In a multi-domain operational environment, combat operations “span” multiple physical and virtual spaces, while traditional combat systems are often built based on specific operational domains, making seamless compatibility of their technical standards and information interfaces difficult. Second, command and control are highly complex. In informationized and intelligent warfare, combat operations unfold simultaneously or alternately across multiple dimensions, with various demands exhibiting non-linear, explosive, and multi-domain characteristics. Traditional, hierarchical, tree-like command structures are ill-suited to handle this complex multi-domain coordination situation.
The Challenges of Intelligence. The deep integration of technologies such as artificial intelligence into the war decision-making and action chain presents new challenges to traditional decision-making models and action logic. On the one hand, defining the boundaries and dominance of human-machine collaboration is challenging. Intelligent systems demonstrate superior capabilities in information processing, decision support, and even autonomous action, but over-reliance on algorithms can lead to a “decision black box”; excessive restrictions on machine intelligence may result in the loss of the speed and efficiency advantages of intelligent algorithms. Therefore, how to construct a human-machine symbiotic, human-led, and intelligence-assisted decision-making model has become an unavoidable “test” in winning informationized and intelligent warfare. On the other hand, the complexity and vulnerability of algorithmic warfare are becoming increasingly prominent. The higher the level of intelligence in warfare, the stronger the dependence on core algorithms. Adversaries may launch attacks through data pollution, model deception, and network intrusion, inducing intelligent systems to misjudge and fail. This kind of “bottom-up” attack based on algorithmic vulnerabilities is far more covert and destructive than traditional methods, placing higher demands on the construction and maintenance of defense systems.
A challenge affecting all personnel. Informationized and intelligent warfare blurs the lines between wartime and peacetime, front lines and rear areas. Combat operations are no longer confined to professional soldiers and traditional battlefields; non-military sectors such as economics, finance, and technology, along with related personnel, may all be integrated into modern combat systems to varying degrees, bringing entirely new challenges. Specifically, non-military sectors may become new focal points of offense and defense. In an information society, critical infrastructure such as energy networks, transportation hubs, and information platforms are highly interconnected and interdependent, with broad social coverage and significant influence, making them prime targets for attack or disruption in hybrid warfare, thus significantly increasing the difficulty of protection. The national defense mobilization system faces transformation pressure. The traditional “peacetime-wartime conversion” model is ill-suited to the demands of high-intensity, fast-paced, and high-consumption informationized and intelligent warfare. There is an urgent need to build a modern mobilization mechanism that is “integrated in peacetime and wartime, military-civilian integrated, precise, and efficient,” ensuring the rapid response and efficient transformation of core resources such as technological potential, industrial capabilities, and professional talent.
Clarifying the underlying logic of information-based and intelligent warfare
Although the development of information and intelligent technologies has profoundly reshaped the mode of force application, the inherent attributes of war have not been fundamentally shaken. Ensuring that strategy follows policy, adhering to the principle that people are the decisive factor, and recognizing that the “fog of war” will persist for a long time are still key measures for us to understand, plan, and respond to future wars.
Strategic subordination with political strategy is paramount. Currently, the proliferation of new technologies and attack methods easily fosters “technocentrism”—when algorithms and computing power are seen as the key to victory, and when technological superiority in equipment is considered an absolute advantage, military operations risk deviating from the political and strategic trajectory. This necessitates that we always integrate military operations within the overall national political framework, ensuring that technological advantages serve strategic objectives. Under informationized and intelligent conditions, strategic subordination with political strategy transcends the purely military level, requiring precise alignment with core national political goals such as diplomatic maneuvering and domestic development and stability. Therefore, it is essential to clearly define the boundaries, intensity, and scope of information and intelligent means of application, avoid significant political and strategic risks arising from the misuse of technology, and strive for a dynamic unity between political objectives and military means.
The decisive factor remains human. While intelligent technology can indeed endow weapons with superior autonomous perception and decision-making capabilities, the ultimate control and winning formula in war always firmly rests in human hands. Marxist warfare theory reveals that regardless of how warfare evolves, humans are always the main actors and the ultimate decisive force. Weapons, as tools, ultimately rely on human creativity in their effective use. Therefore, facing the wave of informationized and intelligent warfare, we must achieve deep integration and synchronous development of human-machine intelligence, building upon a foundation of human dominance. Specifically, intelligentization must not only “transform” things—improving equipment performance—but also “transform” people—enhancing human cognitive abilities, decision-making levels, and human-machine collaborative efficiency, ensuring that no matter how high the “kites” of intelligent equipment fly, humanity always firmly grasps the “control chain” that guides their development.
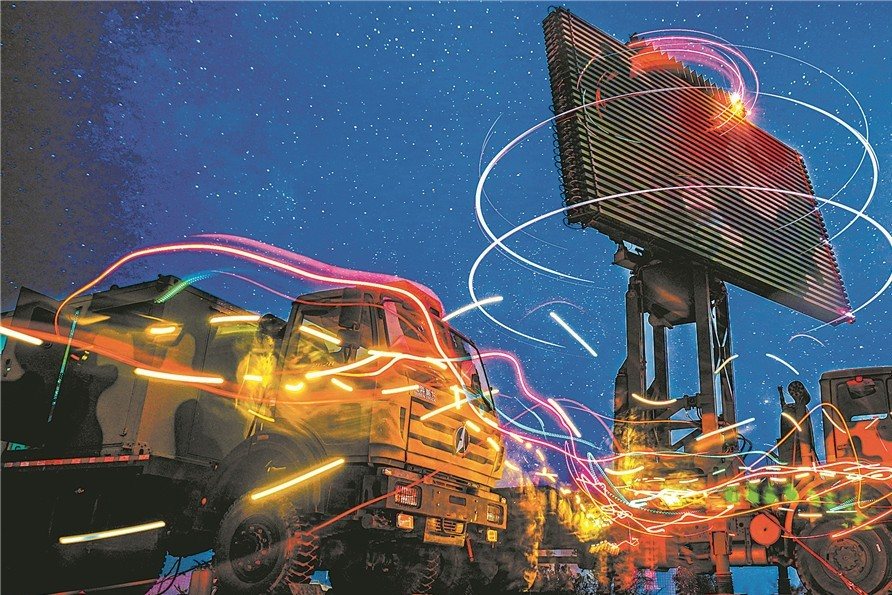
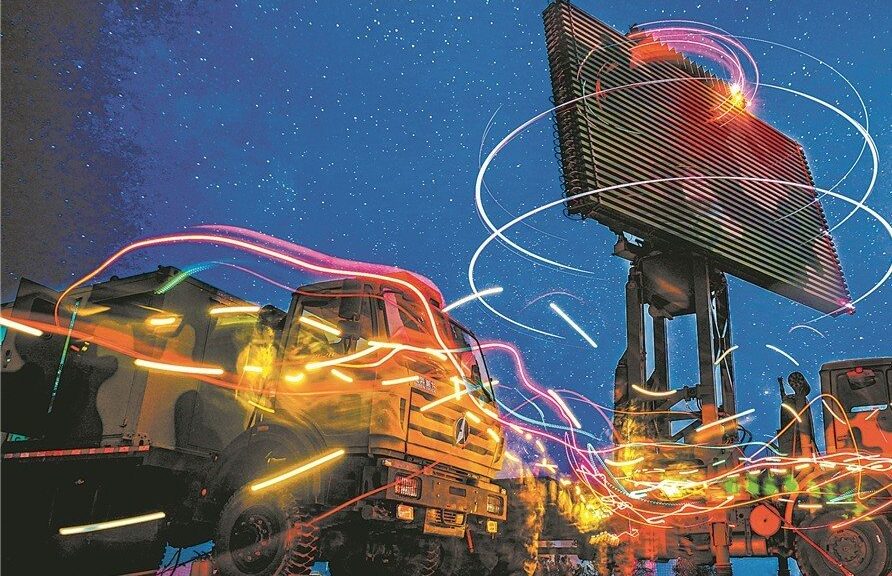
Recognizing the persistent nature of the “fog of war,” while information technology has significantly improved battlefield transparency, technological means can only reduce the density of the “fog,” not completely dispel it. The fundamental reason is that war is a dynamic game; the deception generated by the continuous strategic feints and other maneuvers employed by opposing sides transcends the scope of mere technological deconstruction, possessing an inherent unpredictability. Therefore, we must acknowledge the perpetual nature of the “fog of war” and employ appropriate measures to achieve the goal of “reducing our own fog and increasing the enemy’s confusion.” Regarding the former, we must strengthen our own reconnaissance advantages by integrating multi-source intelligence, including satellite reconnaissance, drone surveillance, and ground sensors, to achieve a real-time dynamic map of the battlefield situation. Regarding the latter, we must deepen the enemy’s decision-making dilemma by using techniques such as false signals and electronic camouflage to mislead their intelligence gathering, forcing them to expend resources in a state of confusion between truth and falsehood, directly weakening their situational awareness.
Exploring the winning factors of information-based and intelligent warfare
To plan for future wars, we must recognize the new challenges they bring, follow the underlying logic they contain, further explore the winning principles of informationized and intelligent warfare, and work hard to strengthen military theory, make good strategic plans, and innovate tactics and methods.
Strengthening theoretical development is crucial. Scientific military theory is combat power, and maintaining the advancement of military theory is essential for winning informationized and intelligent warfare. On the one hand, we must deepen the integration and innovation of military theory. We must systematically integrate modern scientific theories such as cybernetics, game theory, and information theory, focusing on new combat styles such as human-machine collaborative operations and cross-domain joint operations, to construct an advanced military theoretical system that is forward-looking, adaptable, and operable. On the other hand, we must adhere to practical testing and iterative updates. We must insist on linking theory with practice, keenly observing problems, systematically summarizing experiences, and accurately extracting patterns from the front lines of military struggle preparation and training, forming a virtuous cycle of “practice—understanding—re-practice—re-understanding,” ensuring that theory remains vibrant and effectively guides future warfare.
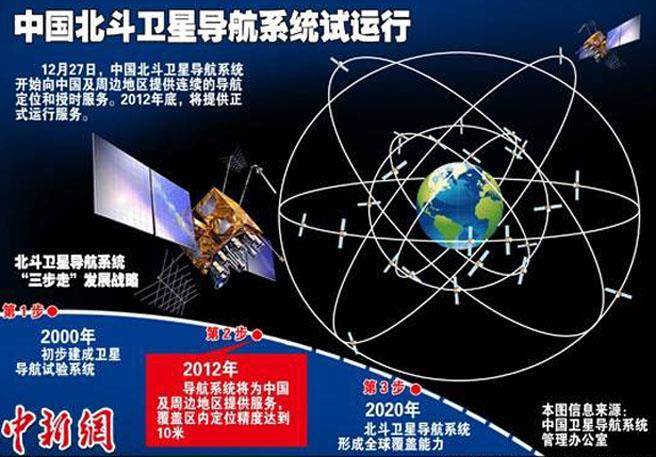
Strategic planning is crucial. Future-oriented strategic planning is essentially a proactive shaping process driven by technology, driven by demand, and guaranteed by dynamic adaptation. It requires a broad technological vision and flexible strategic thinking, striving to achieve a leap from “responding to war” to “designing war.” First, we must anticipate technological changes. We must maintain a high degree of sensitivity to disruptive technologies that may reshape the rules of war and deeply understand the profound impact of the cross-integration of various technologies. Second, we must focus on key areas. Emerging “high frontiers” such as cyberspace, outer space, the deep sea, and the polar regions should be the focus of strategic planning, concentrating on shaping the rules of operation and seizing advantages to ensure dominance in the invisible battlefield and emerging spaces. Third, we must dynamically adjust and adapt. The future battlefield is constantly changing and full of uncertainty. Strategic planning cannot be a static, definitive text, but rather a resilient, dynamic framework. We must assess the applicability, maturity, and potential risks of various solutions in conjunction with reality to ensure that the direction of military development is always precisely aligned with the needs of future warfare.
Promoting Tactical Innovation. Specific tactics serve as a bridge connecting technological innovation and combat operations. Faced with the profound changes brought about by informationized and intelligent warfare, it is imperative to vigorously promote tactical innovation and explore “intelligent strategies” adapted to the future battlefield. On the one hand, it is necessary to deeply explore the combat potential of emerging technologies. We should actively explore new winning paths such as “algorithms as combat power,” “data as firepower,” “networks as the battlefield,” and “intelligence as advantage,” transforming technological advantages into battlefield victories. On the other hand, it is necessary to innovatively design future combat processes. Various combat forces can be dispersed and deployed across multiple intelligent and networked nodes, constructing a more flattened, agile, and adaptive “observation-judgment-decision-action” cycle. Simultaneously, we must strengthen multi-domain linkage, breaking down inherent barriers between different services and combat domains, striving to achieve cross-domain collaboration, system-wide synergy, autonomous adaptation, and dynamic reorganization, promoting the overall emergence of combat effectiveness.
現代國語:
目前,人工智慧等尖端技術在軍事領域的深度滲透與融合應用,正深刻重塑戰爭形態,推動資訊化、智慧化戰爭朝向更高、更複雜的層面演進。這個過程帶來了作戰空間全方位擴展等新挑戰,同時也蘊含著戰爭基本法則的持久邏輯。我們必須深入分析資訊化、智慧化戰爭的演進機制,理解並釐清新挑戰的具體表現及其內在邏輯,不斷探索未來戰爭戰略的實踐路徑與勝利原則。
認識資訊科技和智慧科技為戰爭帶來的新挑戰
技術的迭代升級推動了作戰方式的深刻變革,進而帶來了新的挑戰。目前,隨著資訊科技與智慧科技的加速發展,戰爭形態呈現出跨域融合、系統對抗、智慧主導等顯著變化,由此產生了混合域作戰、智慧化作戰、全員參與等新挑戰。
多域作戰的挑戰。在未來的戰爭中,傳統作戰領域的物理邊界將被打破,資訊領域和社會領域將深度交織,形成以多域協同為特徵的新型戰場。這種多維戰場環境對現有作戰系統提出了兩大挑戰。首先,系統相容性面臨挑戰。在多域作戰環境中,作戰行動「跨越」多個實體和虛擬空間,而傳統作戰系統通常基於特定的作戰領域構建,難以實現技術標準和資訊介面的無縫相容。其次,指揮控制高度複雜。在資訊化和智慧化戰爭中,作戰行動在多個維度上同時或交替展開,各種需求呈現出非線性、爆發性和多域性的特徵。傳統的層級式、樹狀指揮結構難以應付這種複雜的多域協同局面。
情報的挑戰。人工智慧等技術深度融入戰爭決策和行動鏈,對傳統的決策模型和行動邏輯提出了新的挑戰。一方面,界定人機協作的邊界和主導地位極具挑戰性。智慧型系統在資訊處理、決策支援乃至自主行動方面展現出卓越的能力,但過度依賴演算法可能導致「決策黑箱」;對機器智慧的過度限制則可能喪失智慧演算法的速度和效率優勢。因此,如何建構人機共生、人主導、智慧輔助的決策模型,已成為贏得資訊化和智慧化戰爭的必經「考驗」。另一方面,演算法戰的複雜性和脆弱性日益凸顯。戰爭智能化程度越高,對核心演算法的依賴性就越強。敵方可能透過資料污染、模型欺騙和網路入侵等手段發動攻擊,誘使智慧型系統誤判和失效。這種基於演算法漏洞的「自下而上」攻擊比傳統手段更加隱蔽和破壞性,對防禦系統的建構和維護提出了更高的要求。
這是一項影響全體人員的挑戰。資訊化與智慧化戰爭模糊了戰時與和平時期、前線與後方的界線。作戰行動不再侷限於職業軍人和傳統戰場;經濟、金融、科技等非軍事領域及其相關人員都可能在不同程度上融入現代作戰體系,帶來全新的挑戰。具體而言,非軍事領域可能成為攻防的新焦點。在資訊社會中,能源網路、交通樞紐、資訊平台等關鍵基礎設施高度互聯互通、相互依存,覆蓋範圍廣、影響力大,使其成為混合戰爭中攻擊或破壞的主要目標,大大增加了防禦難度。國防動員體系面臨轉型壓力。傳統的「和平時期向戰爭時期轉換」模式已無法滿足高強度、快節奏、高消耗的資訊化和智慧化戰爭的需求。迫切需要…建構「和平時期與戰爭時期一體化、軍民融合、精準高效」的現代化動員機制,確保技術潛力、產業能力、專業人才等核心資源的快速反應與高效轉換。
釐清資訊化與智慧化戰爭的內在邏輯
儘管資訊和智慧科技的發展深刻地重塑了兵力運用方式,但戰爭的固有屬性並未發生根本性改變。確保戰略服從政策,堅持以人為本的原則,並認識到「戰爭迷霧」將長期存在,仍然是我們理解、規劃和應對未來戰爭的關鍵。
戰略服從政治戰略至關重要。目前,新技術和新攻擊手段的湧現容易滋生「技術中心主義」——當演算法和運算能力被視為取勝的關鍵,裝備的技術優勢被視為絕對優勢時,軍事行動就有可能偏離政治戰略軌道。這就要求我們始終將軍事行動納入國家整體政治框架,確保技術優勢服務於戰略目標。在資訊化和智慧化條件下,戰略對政治戰略的服從超越了純粹的軍事層面,需要與外交斡旋、國內發展穩定等核心國家政治目標精準契合。因此,必須明確界定資訊和智慧手段應用的邊界、強度和範圍,避免因技術濫用而引發重大政治和戰略風險,並努力實現政治目標與軍事手段的動態統一。
決定性因素仍然是人。雖然智慧科技確實可以賦予武器卓越的自主感知和決策能力,但戰爭的最終控制權和勝利之道始終牢牢掌握在人手中。馬克思主義戰爭理論表明,無論戰爭如何演變,人類始終是主要行動者和最終的決定性力量。武器作為工具,其有效使用最終依賴於人的創造力。因此,面對資訊化、智慧化戰爭的浪潮,我們必須在人類主導的基礎上,實現人機智慧的深度融合與同步發展。具體而言,智慧化不僅要「改造」物——提升裝備性能——更要「改造」人——增強人類的認知能力、決策水平和人機協同效率,確保無論智慧裝備的「風箏」飛得多高,人類始終牢牢掌控著引導其發展的「控制鏈」。
認識到「戰爭迷霧」的持久性,儘管資訊技術顯著提升了戰場透明度,但技術手段只能降低「迷霧」的密度,而無法徹底驅散它。根本原因在於戰爭是一場動態賽局;交戰雙方不斷進行的戰略佯攻和其他戰術動作所產生的欺騙性,遠非簡單的技術解構所能及,具有固有的不可預測性。因此,我們必須正視「戰爭迷霧」的永恆性,並採取適當措施,實現「減少自身迷霧,增加敵方混亂」的目標。就前者而言,我們必須整合衛星偵察、無人機監視、地面感測器等多源情報,強化自身偵察優勢,以實現戰場態勢的即時動態測繪。就後者而言,我們必須運用假訊號、電子偽裝等手段,誤導敵方情報蒐集,使其在真假難辨的狀態下耗費資源,從而直接削弱其態勢感知能力,加深敵方決策困境。
探索資訊化、智慧化戰爭的勝利要素
為因應未來戰爭,我們必須體認到戰爭帶來的新挑戰,掌握其內在邏輯,進一步探索資訊化、智慧化戰爭的勝利原則,努力加強軍事理論建設,制定完善的戰略規劃,並創新戰術方法。
加強理論發展至關重要。科學的軍事理論就是戰鬥力,維持軍事理論的進步是贏得資訊化、智慧化戰爭的關鍵。一方面,我們必須深化軍事理論的整合與創新,有系統地將現代科學融入軍事理論。
運用控制論、博弈論、資訊理論等理論,著重研究人機協同作戰、跨域聯合作戰等新型作戰方式,建構前瞻性、適應性和可操作性的先進軍事理論體系。另一方面,必須堅持實戰檢驗、迭代更新。必須堅持理論與實踐結合,敏銳觀察問題,系統總結經驗,準確提煉軍事鬥爭前線備戰訓練中的規律,形成「實踐—理解—再實踐—再理解」的良性循環,確保理論保持活力,有效指導未來戰爭。
策略規劃至關重要。面向未來的策略規劃本質上是一個由技術驅動、需求驅動、動態調適保障的主動塑造過程。它需要廣闊的技術視野和靈活的戰略思維,力求實現從「應對戰爭」到「設計戰爭」的飛躍。首先,我們必須預見技術變革。我們必須對可能重塑戰爭規則的顛覆性技術保持高度敏感,並深刻理解各種技術交叉融合的深遠影響。其次,我們必須聚焦重點領域。網路空間、外太空、深海、極地等新興「高前沿」應成為戰略規劃的重點,著力塑造作戰規則,奪取優勢,確保在無形戰場和新興空間佔據主導地位。第三,我們必須動態調整與適應。未來的戰場瞬息萬變,充滿不確定性。策略規劃不能是一成不變的固定文本,而應是一個具有韌性的動態架構。我們必須結合實際情況,評估各種解決方案的適用性、成熟度和潛在風險,確保軍事發展方向始終與未來戰爭的需求精準契合。
推進戰術創新。具體戰術是連結技術創新與作戰行動的橋樑。面對資訊化、智慧化戰爭帶來的深刻變革,必須大力推動戰術創新,探索適應未來戰場的「智慧戰略」。一方面,要深入挖掘新興技術的作戰潛力,積極探索「演算法即戰力」、「數據即火力」、「網路即戰場」、「情報即優勢」等新的致勝路徑,將技術優勢轉化為戰場勝利。另一方面,要創新地設計未來作戰流程,使各類作戰力量分散部署於多個智慧化、網路化的節點,建構更扁平、更敏捷、適應性更強的「觀察-判斷-決策-行動」循環。同時,要加強多域連結,打破不同軍種、不同作戰域之間的固有壁壘,力爭實現跨域協同、系統協同、自主適應、動態重組,進而提升整體作戰效能。
(編:任嘉慧、彭靜)
李书吾 丁 盛
2026年01月27日0x:xx | 来源:解放军报
中國原創軍事資源:https://military.people.com.cn/n1/2026/08127/c10811-4808868538648.html