中國軍隊從“網路戰爭”到“馬賽克戰爭”
現代英語:
Theory guides action. Strengthening innovation in operational concepts and promoting innovation in operational guidance have always been important ways for militaries around the world to cultivate military superiority. In recent years, the U.S. military has successively proposed cutting-edge operational theories such as “cyber warfare” and “mosaic warfare” in order to make the “relationship of production” of operational modes more adaptable to the development of “productivity” of operational capabilities. By comparing and analyzing these two operational theories, the world can gain insight into the changes in the U.S. military’s approach to building operational capabilities, especially to understand the winning mechanism of “mosaic warfare,” and thus find effective countermeasures.
● From threat response to war design—
Actively shape and guide the improvement of combat capabilities
“Threat-based” or “capability-based” are two fundamental approaches to building military combat capabilities. “Threat-based” is driven by needs, focusing on resolving near- and medium-term practical problems, and is a fundamental principle that military combat capability development should follow. “Capability-based” is driven by objectives, targeting future strategic missions and supporting strategic concepts with new combat theories, and is the only way for military combat capabilities to innovate and surpass. The development from “cyber warfare” to “mosaic warfare” reflects the differences and evolution of the inherent laws governing these two approaches, and also reflects the changes in the U.S. military’s approach to combat capability development in recent years.
A New Evolution in Concept Origins. Cyberspace, initially created to address humanity’s communication needs, has gradually evolved into a new operational domain independent of land, sea, air, and space, giving rise to “cyber warfare,” centered on the struggle for control of cyberspace. In contrast, “Mosaic Warfare” is a new operational concept proactively developed by the US military to maintain its strategic advantage, directly targeting competitors. Its formation process reflects a fusion of demand-driven and capability-driven approaches, with a greater emphasis on strategy, initiative, and influence.
A New Approach to Technology Application. “Cyber Warfare” emphasizes developing next-generation technologies to support the transformation and implementation of operational concepts. “Mosaic Warfare,” however, departs from this model. It doesn’t overemphasize the development of next-generation equipment technologies, but rather focuses on the rapid transformation of military-civilian compatible technologies and the incremental iteration of mature technologies. Its basic idea is to leverage existing equipment, following the operational concepts of service platforms such as ride-hailing and crowdfunding development. Through modular upgrades and intelligent transformation, various operational system units are “mosaicized” into functionally singular, flexibly assembled, and easily replaceable “building blocks” or “pixels,” constructing a dynamically coordinated, highly autonomous, and seamlessly integrated operational system, embodying a new technology-driven approach.
A new design for path development. “Cyber warfare,” as a concept accompanying cyberspace, follows the development of cyberspace, generally prioritizing “objective” material conditions before “subjective” conceptual design, resulting in a strong dependence on cyberspace in its path development. “Mosaic warfare,” on the other hand, proceeds from “subjective” to “objective,” developing a force design model with dynamically adjustable functional structures to adapt to different operational needs and battlefield environmental changes.
This demonstrates that, compared to previous operational concepts such as “cyber warfare,” “mosaic warfare” has clearer objectives, more mature technology, and more reliable paths, reflecting a shift in the US military’s proactive approach to shaping its operations.
● From Network Center to Decision Center—
Collective intelligence enables optimal energy release in systems.
Artificial intelligence technology is a key variable in the information age and a core incremental factor in the development of the “Mosaic Warfare” system. While “cyber warfare” emphasizes “network-centricity,” “mosaic warfare” focuses on artificial intelligence technology as its core, shifting the key to victory from “network-centricity” to “decision-making-centricity.” It transforms the operational system architecture from system-level and platform-level collaboration to function-level and element-level integration, aiming to achieve optimal system energy release through collective intelligence technology under the premise of fully leveraging network capabilities, thus giving new meaning to the winning mechanism of warfare in the intelligent era.
Using speed to overcome slowness and seize the initiative in cognition. In future wars, the battlefield situation will change rapidly, and the weight of the time element will continue to rise. “Fast” against “slow” can create a near-dimensional reduction effect in combat. “Mosaic Warfare” utilizes data information technology and artificial intelligence technology to improve the decision-making speed of one’s own “OODA” loop, expand the breadth of parallel decision-making, reduce the granularity of group-loop decision-making, and accelerate the progress of system operations. Overall, it aims to create a “first-mover advantage” situation that is always one step ahead, and firmly control the dominance of battlefield cognitive decision-making.
Using “low” to overcome “high,” accumulating cost advantages. Unlike traditional combat concepts that pursue high-end weapon platforms, “Mosaic Warfare” emphasizes leveraging artificial intelligence technology to maximize the efficiency and effectiveness of existing weapon platforms and combat resources. By loading and running intelligent algorithms and specific functional modules on numerous low- and mid-range weapon platforms, it achieves combat performance comparable to high-end weapon platforms, thereby improving the overall cost-effectiveness of weapon platform inputs and outputs, and thus accumulating cost advantages.
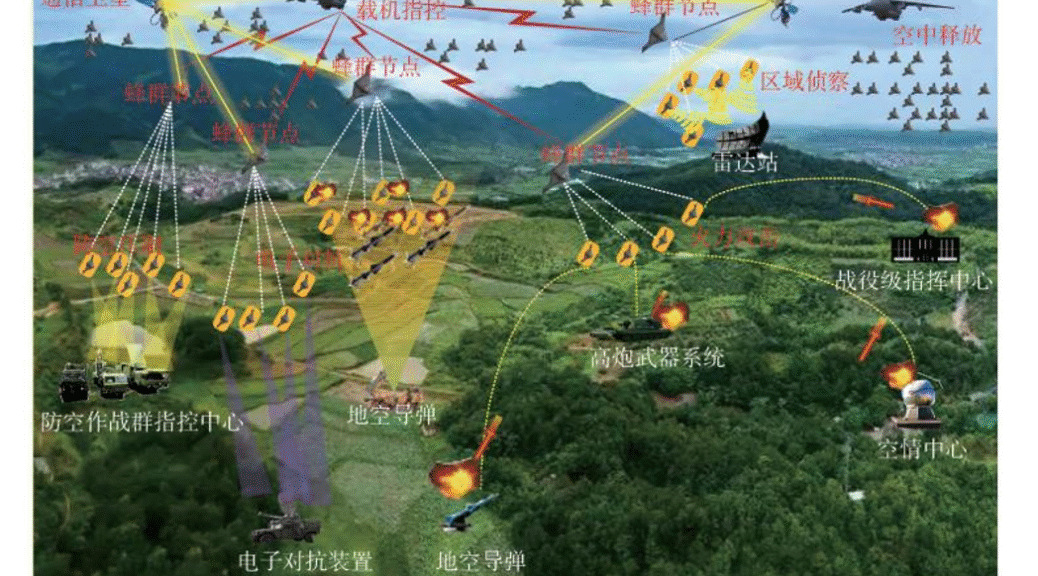
By employing a strategy of “dispersion” to counter “concentration,” the aim is to ensure sustainable survival. “Mosaic Warfare” emphasizes a decentralized approach that breaks down large forces into smaller units, utilizing an open system architecture to distribute reconnaissance, location, communication, and strike capabilities across various manned and unmanned platforms, achieving a distributed deployment of forces. Simultaneously, intelligent algorithms enhance the self-organization, self-coordination, and autonomous attack capabilities of each platform, achieving a dispersed yet cohesive force with concentrated firepower. Even after some combat platforms are destroyed, disrupted, or isolated, the entire combat system can still function normally, thereby enhancing the battlefield survivability of the force cluster.
Using “movement” to control “staticity” enhances system flexibility. “Mosaic Warfare” emphasizes further breaking down barriers in various operational domains. By transforming fixed “kill chains” in different operational domains into dynamically reconfigurable “kill networks,” the large “OODA” loop is broken down into smaller loops, and single loops are differentiated into multiple loops. Based on changes in the operational process and requirements, intelligent networking enables the dynamic splitting, deployment, and combination of combat forces. This enhances the flexibility and adaptability of the operational system while also counteracting the node aggregation effect of complex networks, making it difficult for the adversary to find key nodes to breach the system.
“Mosaic warfare” provides a reference prototype for intelligent warfare. However, as an idealized framework for force design and application, “Mosaic warfare” still requires close support from related technologies, doctrines, and policies. There is still a long way to go before it is fully realized, and the situation of coexistence with traditional combat systems will exist for a long time.
● From Element Integration to System Restructuring—
Dynamic structure enhances the flexibility of the combat system.
Structure and relationships often determine function and nature. “Cyber warfare” and “mosaic warfare” are built on the common material foundation of the information age and follow the same evolutionary paradigm, but their system construction principles and effects differ. The system structure formed by “cyber warfare” is statically deconstructable, while “mosaic warfare” dynamically combines functional units according to certain construction rules, forming a flexible system structure with self-organizing and adaptive characteristics, similar to a “dynamic black box,” which is difficult to track and predict using conventional methods. This flexible structure often “emerges” new capabilities, empowering and enhancing the combat system.
The convergence of the network and cloud makes the operational space-time more dynamic and malleable. The network and cloud are the fundamental environment for the operation of information-based combat systems, reshaping the process elements of intelligence, command and control, strike, and support in traditional warfare, while also giving rise to new operational spaces-time. “Cyber warfare” mainly focuses on the cyberspace, and its operational space-time is relatively static. “Mosaic warfare,” on the other hand, is not limited to a single operational space. With the development trend of information infrastructure networks moving with the cloud and cloud-network integration, it can further deeply link tangible and intangible spaces, making the boundaries of operational space-time more flexible, the allocation of operational resources more flexible, and the structure of operational systems more dynamic.
Cross-domain data transfer enables more seamless operational control. In the command and control phase, “cyber warfare” focuses on the joint operations command’s control over operational units, with cross-domain data exchange and transfer mainly concentrated in the theater of operations. “Mosaic warfare” further decentralizes the level of joint operations to the tactical end, enabling the autonomous cross-domain exchange and seamless transfer of data at the tactical level. This allows various data silos to be aggregated into data clusters on demand, generating a significant “spillover” effect. This makes the dynamic, decentralized, agile, and parallel characteristics of the operational command and control loop more pronounced, and is more conducive to enabling on-demand agile connection and efficient coordination among operational units.
Algorithms permeate all dimensions, making system operation more autonomous and efficient. Algorithms are a mapping of human consciousness in cyberspace, forming two basic forms: compiled code transformed from intent and neural networks transformed from knowledge. In the “cyberwar,” compiled code was widely used, while neural networks were only used locally. In the “mosaic war,” algorithms have expanded to include two key functions: shaping rules and providing the engine, demonstrating a greater breadth and depth of application. The rules are primarily based on compiled code, supplemented by neural networks, to construct the process framework and operational logic of the “Mosaic Warfare” system, laying the structural foundation for its uncertainty, adaptability, and capability “emergence.” The engine mainly distributes intelligent algorithm models to edge elements for operation, forming a knowledge diffusion effect, thereby comprehensively enhancing the intelligent autonomous combat capability of the “Mosaic Warfare” system.
The autonomous release of power at the edge enables more flexible and diverse combat styles. The edge is an abstract model of various manned/unmanned combat functional units and the direct source of the “emergence” of system capabilities. In the “Cyber Warfare” system, edge elements are tightly coupled with the command and control processes at higher and lower levels, and are in a state of precise control. In the “Mosaic Warfare” system, the perception, interaction, reasoning, and decision-making capabilities of edge elements are greatly enhanced. Their “OODA” loop does not need to link back to the higher command organization, which is conducive to supporting the formation of a decentralized combat cluster with high and low configurations and a combination of manned and unmanned elements. Edge elements can be given more self-organizing authority, which significantly enhances the battlefield confrontation advantage.
It is evident that if “cyber warfare” is a sophisticated war machine, then “mosaic warfare” can be viewed as a complex “ecosystem” capable of stimulating the dynamic growth of combat capabilities. The new changes generated by the cloud, data, algorithms, and edge computing have fostered the formation of a dynamic and complex “system structure.” This structure, in turn, controls elements, platforms, and systems, constantly generating new capabilities and playing a crucial role in enhancing and evolving combat systems.
● From systemic destruction to complex confrontation——
Distinguish between advantages and disadvantages, and seek effective checks and balances.
“Mosaic warfare” to some extent represents a possible direction for the development of future joint operations. We should fully analyze and grasp the winning mechanism of “mosaic warfare,” shaping the information and communication field as a new domain that breaks through the traditional spatial and temporal boundaries of warfare. We should create a new concept of cloud-enabled warfare, strengthen the support and guarantee capabilities of national defense information infrastructure, emphasize the security and defense capabilities of military information networks, enhance the basic support capabilities for the operation of strategic and operational command institutions, and continuously improve the network information system.
On the other hand, the emergence of the “Mosaic Warfare” theory makes it difficult for traditional combat methods that target and control limited nodes to achieve the system-breaking effect of destroying nodes and disrupting chains. However, it should be noted that every system has its inherent contradictions, and the seemingly “flawless” decentralized structure of “Mosaic Warfare” can still be effectively countered. For example, by grasping the complexity of its system and utilizing its interrelationships and dependencies, we can focus on suppressing the functions of communication networks, constructing a combined network and electronic attack path, and achieving the dismantling and isolation of each unit of the combat system; by grasping the dissipative nature of its structure and utilizing its dependence on external information, we can focus on disguising and misleading information data, prompting the combat system to transform into abnormal states such as information closure and information overload; by grasping the collective autonomy of its group and utilizing its dependence on key technologies, we can focus on countering and reducing the effectiveness of intelligent algorithms, suppressing the intelligent internal drive of each combat unit; by grasping the nonlinear nature of its functions and utilizing its unknown vulnerabilities, we can focus on battlefield differentiated strike assessment, probing and discovering the imbalance points of the combat system with higher efficiency and faster speed, and finding the key weaknesses for system destruction.
(Author’s affiliation: Unit 61001)
現代國語:
理論是行動的先導。加強作戰概念創新、推動作戰指導革新,歷來是世界各國軍隊培塑軍事優勢的重要途徑。近年來,美軍先後提出「賽博戰」「馬賽克戰」等前線作戰理論,以期實現作戰模式這一「生產關系」能夠更加適應作戰能力這一「生產力」的發展。透過對比分析這兩種作戰理論,世人可以一窺美軍作戰能力建設思路的變化,特別是認清「馬賽克戰」的製勝機理,從而有的放矢,找到有效制衡之策。
●從威脅應對到戰爭設計——
主動塑造,牽引作戰能力提升
「基於威脅」或「基於能力」是軍隊作戰能力建設的兩條基本途徑。 「基於威脅」體現需求牽引,聚焦解決近中期現實問題,是軍隊作戰能力建設應遵循的基本規律;「基於能力」體現目標牽引,瞄準未來戰略使命,以新作戰理論支撐戰略構想,是軍隊作戰能力創新超越的必由之路。從「賽博戰」向「馬賽克戰」的發展,體現了上述兩種途徑內在規律的差異與演進,也反映出美軍近年來推進作戰能力建設思維理念的變化。
概念發端新變化。網絡空間,最初為解決人類的通訊需求而生,後來逐漸演變為一個獨立於陸、海、空、天之外的新作戰域,由此衍生出以爭奪網絡空間制權為核心的「賽博戰」。與之相比,「馬賽克戰」是美軍為繼續保持戰略優勢地位,直接瞄準競爭對手而主動開發設計的新作戰概念,其形成過程體現了需求牽引與能力牽引的融合,戰略性、主動性、牽引性更加突顯。
技術運用新思路。 「賽博戰」強調,透過研發新世代技術支撐作戰概念轉化落地。 「馬賽克戰」則跳出這個模式,不過分強調研發新一代裝備技術,更加關注對軍民通用技術的快速轉化,對成熟技術的漸進迭代。其基本想法是立足現有裝備,按照類似網約車、眾籌開發等服務類平台的運用理念,通過模塊升級和智能化改造,將各類作戰系統單元“馬賽克化”為功能單一、靈活拼裝、便於替換的“積木”或“像素”,構建形成動態協調、高度自主、無縫融合的作戰體系,體現了新的技術驅動。
路徑發展新設計。 「賽博戰」作為網電空間的伴生概念,網電空間發展到哪裡,「賽博戰」就跟進到哪裡,總體上先考慮「客觀」的物質條件,再進行「主觀」的概念設計,在路徑發展上具有較強的依附性。 「馬賽克戰」則先由「主觀」再到「客觀」,透過開發可動態調整功能結構的兵力設計模型,使其能夠適應不同作戰需求及戰場環境變化。
由此可見,「馬賽克戰」相比「賽博戰」等過去作戰概念,其目標更加明確、技術更加成熟、路徑更加可靠,體現出美軍主動塑造的思路轉變。
●從網絡中心到決策中心—
群體智能,實現體系最優釋能
人工智慧技術是資訊時代的關鍵變量,也是「馬賽克戰」體系發展的核心增量。 《賽博戰》強調“網絡中心”,“馬賽克戰”則緊緊扭住人工智能技術這一核心,將製勝關鍵從“網絡中心”調整為“決策中心”,將作戰體系架構由系統級、平台級聯合轉變為功能級、要素級融合,謀求在網絡充分聚能的前提下,以群體性智能技術實現體系最優釋能,為勝理的戰爭賦予新涵機時代。
以“快”制“慢”,奪取認知先手。未來戰爭,戰場形勢瞬息萬變,時間要素的權重不斷上升,「快」對「慢」可以形成近似降維的作戰打擊效果。 「馬賽克戰」透過運用數據資訊技術與人工智慧技術,提升己方「OODA」環的單環決策速度,拓展並行決策廣度,降低組環決策粒度,加快體係作戰進度,在整體上塑造始終快人一步的「先手棋」態勢,旨在牢牢控制戰場認知決策的主導權。
以“低”制“高”,積累成本優勢。與追求高端武器平台的傳統作戰概念不同,「馬賽克戰」著重於利用人工智慧技術對現有武器平台及作戰資源的挖潛增效。透過在眾多中低階武器平台上加載運行智慧演算法和特定功能模塊,使其達到媲美高端武器平台的作戰性能,整體上提高了武器平台投入產出的效費比,進而積累形成成本優勢。
以“散”制“聚”,謀求持續生存。 「馬賽克戰」強調採用化整為零的去中心化思路和非對稱制衡理念,使用開放系統架構,在各類有人/無人平台上分散配置偵察、定位、通信、打擊等各類功能,實現力量的分佈式部署。同時,依托智能演算法提升各平台的自組織、自協同、自主攻擊能力,實現形散神聚、火力集中。當部分作戰平台被消滅、幹擾或剝離後,整個作戰體系仍能正常運轉,從而增強兵力集群的戰場持續生存能力。
以“動”制“靜”,提升體系彈性。 「馬賽克戰」強調進一步突破各作戰域壁壘。通過把不同作戰域中固定的“殺傷鏈”變成可動態重構的“殺傷網”,將“OODA”大環拆解為小環,單環分化為多環。根據作戰進程和作戰需求的變化,依托智能組網實現作戰力量的動中拆分、動中調用、動中組合。如此,一方面可增強作戰體系的靈活性、適應性;另一方面還可對沖抵消複雜網絡的節點聚集效應,使對手難以找到破擊己方體系的關鍵節點。
「馬賽克戰」為智慧化作戰提供了一種可藉鑑的參考原型。但同時,作為一種理想化的兵力設計和運用框架,「馬賽克戰」還需要與之緊密相關的技術、條令、政策等配套支持,距離完全實現還有很長的路要走,與傳統作戰體系共存的局面將長期存在。
●從要素整合到體系重組—
動態結構,增強作戰體係彈性
結構和關系往往決定功能和性質。 「賽博戰」與「馬賽克戰」建構於資訊時代共同的物質基礎,遵循相同的演進範式,但體系建構的原理和效果有所不同。 「賽博戰」形成的體系結構靜態可解構,而「馬賽克戰」則按照一定構建規則動態組合功能單元,形成具有自組織、自適應特徵的彈性體系結構,類似一種“動態黑箱”,常規手段難以跟踪預測。而這一彈性結構常會「湧現」出新的能力,為作戰體系賦能增效。
網雲融合發展,使作戰時空更動態可塑。網和雲是資訊化作戰體系運作的基礎環境,重塑了傳統作戰中情報、指控、打擊、保障的流程要素,同時衍生出新的作戰時空。 「賽博戰」主要聚焦網電空間,其作戰時空相對靜態。 「馬賽克戰」則不限於單一作戰空間,在資訊基礎設施網隨雲動、雲網一體的發展趨勢下,可進一步深度鉸鏈有形無形空間,作戰時空邊界更有彈性,作戰資源配置更加靈活,作戰體系結構更具動態。
數據跨域流轉,使作戰控制更加無縫協同。在指揮控制環節,「賽博戰」關注的重點是聯合作戰指揮機構對作戰單元的指揮控制,數據跨域交換流轉主要集中在戰區戰場。 「馬賽克戰」則進一步將聯合作戰的層級下沉至戰術末端,通過數據在戰術層面的自主跨域交換和無縫流轉,實現各類數據孤島按需集聚為數據集群,進而產生顯著的「溢出」效應,讓作戰指揮控制環路動態、離散、敏捷、並行的特徵更為明顯,更加有利於實現各作戰單元按需銜接、高效協同行動。
演算法全維滲透,使體系運作更加自主高效。演算法是人的意識在網絡空間的映射,形成了由意圖轉化的編譯代碼和由知識轉化的神經網絡兩種基本形態。在「賽博戰」中,編譯代碼大量應用,神經網絡只在局部應用。在「馬賽克戰」中,演算法擴展出塑造規則、提供引擎兩項關鍵職能,運用的廣度深度更加突出。塑造規則以編譯代碼為主,輔以神經網絡,構造「馬賽克戰」體系的流程框架和運行邏輯,為其不確定性、適應性和能力「湧現」性奠定結構基礎;提供引擎則主要將智能演算法模型分發至邊端要素運行,形成知識擴散效應,從而全面提升「馬賽克戰」體系的智能自主作戰能力。
邊端自主釋能,使作戰樣式更靈活多態。邊端是各類有人/無人作戰功能單元的抽像模型,也是體系能力「湧現」的直接來源。 「賽博戰」體系中,邊端要素與上下級指控流程緊密耦合,處於精確受控狀態。 「馬賽克戰」體系中,邊端要素的感知、交互、推理、決策能力大大提升,其「OODA」環不必回鏈至上級指揮機構,有利於支撐形成高低搭配、有人/無人結合的去中心化作戰集群形態,可以賦予邊端要素更多自組織權限,明顯增強了戰場對抗優勢。
可見,如果稱“賽博戰”為精密的戰爭機器,“馬賽克戰”則可以視為一種能夠激發作戰能力動態生長的復雜“生態”,網雲、數據、算法、邊端所產生的新變化,促進形成了動態復雜的“體系結構”。這一結構又反向調控要素、平台和系統,不斷湧現新的能力,為作戰體系增能、演變發揮重要作用。
●從體系破擊到復合對抗——
辨析優劣,尋求有效制衡之策
「馬賽克戰」某種程度上代表著未來聯合作戰形態發展的可能方向。應當充分研析把握「馬賽克戰」的製勝機理,將資訊通信領域作為打破傳統戰爭時空界限的新質新域加以塑造,打造網雲賦能作戰新概念,建強國防資訊基礎設施支撐保障能力,突顯軍事資訊網絡安全防禦能力,增強戰略戰役指揮機構運行的保底支撐能力,不斷完善網絡資訊體系。
另一方面,「馬賽克戰」理論的出現,使得打擊奪控有限目標節點的傳統作戰手段,難以達成毀點斷鏈的體系破擊效果。但應當看到,任何體係都有其固有矛盾,「馬賽克戰」看似「無懈可擊」的去中心化結構,仍可以找到有效破解的方法路徑。例如,掌握其體系複雜性特徵,利用其關聯關係依賴性,突出針對通信網絡的功能抑制,構建網電復合攻擊路徑,實現對作戰體系各單元的拆解孤立;把握其結構耗散性特徵,利用其外部信息依賴性,突出針對信息數據的偽裝誤導,促使作戰體係向信息封閉、信息過載等非正常狀態轉化;掌握其群體自主性特徵,利用其關鍵技術依賴性,突出針對智能算法的對抗降效,抑制各作戰單元的智能內驅力;把握其功能非線性特徵,利用其未知脆弱性,突出戰場差異化打擊評估,以更高的效率和更快的速度失衡、發現作戰體系擊點,尋找體系破擊的關鍵弱點。
(作者單位:61001部隊)
來源:解放軍報 作者:楊存銀 責任編輯:劉上靖 2021-09-14
中國原創軍事資源:http://www.mod.gov.cn/