我國加快發展先進作戰能力的當代要求
現代英語:
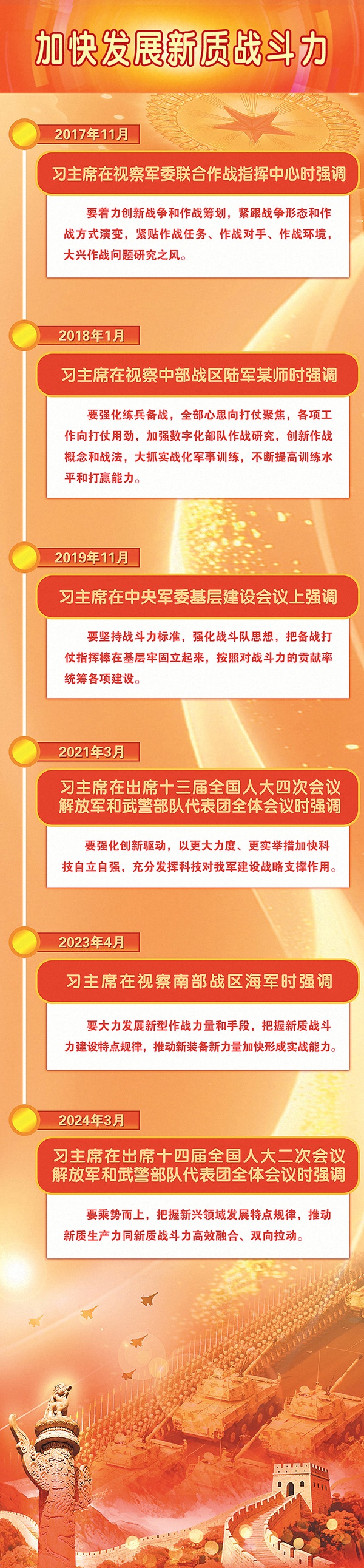
Combat effectiveness is the ultimate determining factor in the rise and fall of an army. It not only affects the operational methods and actual effectiveness of armed forces, but also safeguards the survival, security, and long-term stability of a nation and its people. Advanced combat effectiveness is the latest viewpoint on combat effectiveness development put forward by our Party after President Xi Jinping’s profound exposition of the original and iconic concept of “new-type combat effectiveness.” In January 2019, President Xi Jinping pointed out at the Central Military Commission’s military work conference: “We must strengthen the construction of new types of combat forces and increase the proportion of new-type combat effectiveness.” Since then, President Xi has repeatedly discussed this important issue, emphasizing “building a powerful strategic deterrent force system and increasing the proportion of new-type combat forces in new domains” and “promoting the accelerated improvement of new-type combat effectiveness.” It is precisely on the basis of the practical experience of the formation and development of new-type combat effectiveness in our army in the new era that the new idea and new conclusion of “advanced combat effectiveness” has emerged. Advanced combat capability is a higher form of combat capability, led and supported by new-type combat capability. It emphasizes the large-scale, practical, and systematic application of new-type combat capability, focuses on theoretical innovation, intelligent enhancement, system upgrade, intelligence enhancement, and weapon and equipment upgrade. It also includes the upgrading and creative application of traditional combat capability. It is the evolution of the form, capacity expansion, and quality upgrade of new-type combat capability.
Advanced combat capabilities represent the development trend of military transformation, military intelligence, and military combat methods. They are a new growth point for combat power and a commanding height on the future battlefield. The “Suggestions of the CPC Central Committee on Formulating the 15th Five-Year Plan for National Economic and Social Development” (hereinafter referred to as the “Suggestions”), adopted at the Fourth Plenary Session of the 20th CPC Central Committee, is based on the overall strategic situation of China’s modernization. It makes arrangements for achieving the centenary goal of the People’s Liberation Army on schedule and promoting the modernization of national defense and the armed forces with high quality. It proposes “accelerating the construction of advanced combat capabilities,” pointing out the direction and providing a benchmark for achieving the centenary goal of the People’s Liberation Army on schedule and further improving the quality and efficiency of national defense and military modernization from a new starting point. We must thoroughly study and understand the spirit of the Fourth Plenary Session of the 20th CPC Central Committee, deeply comprehend the firm will and far-sighted planning of the CPC Central Committee with Comrade Xi Jinping at its core in building a consolidated national defense and a powerful army, and continuously creating a new situation in the cause of building a strong military in the new era. We must profoundly grasp the requirements of the times for accelerating the construction of advanced combat capabilities, actively seize the commanding heights of military struggle, seek new advantages in military competition, focus on advanced combat capabilities to think about reforms, grasp construction, and make preparations, promote the work of preparing for war in the new era to go deeper and more practical, and continuously improve the strategic capability to safeguard national sovereignty, security, and development interests.
Advanced combat capabilities are proposed based on a profound understanding of global military development trends, the leapfrog development of new-type productive forces, and the laws governing the modernization of the armed forces.
President Xi Jinping pointed out: “For a country and a nation to revitalize, it must advance in the logic of historical progress and develop in the trend of the times.” Advanced combat capability is an original and iconic concept of Xi Jinping’s thought on strengthening the military. It is a scientific deployment made by the CPC Central Committee with Comrade Xi Jinping at its core, which has keenly grasped the trends of world military development and the laws governing the evolution of warfare, deeply understood the new situation of efficient integration and two-way driving between new-type productive forces and new-type combat capabilities, and scientifically grasped the achievements, historical position, and mission of national defense and military modernization in the new era.
The development of the new military revolution and the evolution of warfare are powerfully driving changes in combat capabilities. In today’s world, a new round of technological revolution and industrial transformation is accelerating, and the new military revolution is progressing rapidly. Strategic high-tech fields such as artificial intelligence, network information, big data, blockchain, quantum technology, biotechnology, and nanomaterials are emerging in rapid succession. The widespread application of science and technology in the military field has profoundly changed the nature of warfare and combat methods, increasingly becoming a crucial factor in determining victory or defeat. The evolution of warfare is showing many new trends, with increasingly prominent intelligent characteristics. Some new technologies and equipment are creating a disruptive advantage over traditional equipment. New types of combat forces, represented by strategic early warning, information control, algorithmic attack and defense, and unmanned intelligence, are increasingly becoming important forces shaping the modern battlefield. Thanks to the rapid advancements in technologies such as artificial intelligence and military robots, the “autonomous capabilities” of weapons and equipment—including autonomous battlefield perception, autonomous combat decision-making, autonomous planning, and autonomous action—are becoming increasingly stronger, elevating them from “execution tools” to “intelligent nodes.” The deep integration of drones and artificial intelligence recognition technology has resulted in a “long-range pursuit” deterrent effect. The coordinated use of firepower strikes and cyberattacks is creating an integrated hardware and software offensive system with full-domain coverage. Driven by military intelligence, new types of combat capabilities are constantly emerging, with higher efficiency and superior quality. Advanced combat capabilities are increasingly becoming a powerful force driving the new military revolution in the world.
The vigorous development of new-type productive forces is driving the upgrading and improvement of combat capabilities. The generation and upgrading of any combat capability is the application and extension of productive forces in the military field under a certain social structure. New-type productive forces are advanced productive forces characterized by high technology, high efficiency, and high quality, with innovation playing a leading role. They represent the most active, technologically advanced, promising, and influential productive force in contemporary society. The rapid development of new-type productive forces provides advanced science and technology and a solid material foundation for the generation of new-type combat capabilities, while also providing the driving force and support for their upgrading and transformation, becoming a key variable in reshaping the form of warfare, reconstructing combat systems, and reorganizing command elements. New-type combat capabilities originate from breakthroughs in key common technologies, cutting-edge leading technologies, and disruptive technologies. They rely on emerging technological means and advanced combat concepts, fully embedding information technology genes and integrating into networked systems. Utilizing new technologies, new equipment, and new tactics, they enable military systems to exhibit new advantages such as strategic guidance, information empowerment, network aggregation, technological strength, and systemic energy release. With the rapid development and widespread application of new-type combat capabilities, the advanced combat capability form they dominate will inevitably emerge, becoming a powerful engine for promoting the transformation and development of modern military systems.
The significant achievements in national defense and military modernization in the new era have laid a solid foundation for advanced combat capabilities. Since the beginning of the new era, President Xi Jinping, based on the overall strategic situation of the great rejuvenation of the Chinese nation and the unprecedented changes in the world, has used the goal of building a strong military to examine and guide the construction of combat capabilities, promoting the vigorous development of all elements of combat capabilities. The reform of national defense and the military has been deepened, forming a new pattern of overall command by the Central Military Commission, combat command by the theater commands, and development by the services. New combat force systems, such as the military aerospace force, cyberspace force, and information support force, have been established and adjusted, achieving a holistic and revolutionary reshaping of the organizational structure and force system. The development of strategic emerging industries and new combat forces has been promoted in a coordinated manner, yielding a series of significant results. The modernization of weaponry has been accelerated, with new fourth-generation equipment, represented by new tanks, carrier-based aircraft, and fighter jets, being deployed to the troops. Major national weapons, represented by the “Dongfeng-5C” liquid-fueled intercontinental strategic nuclear missile, have been showcased at military parades. The first electromagnetic catapult-equipped aircraft carrier, the Fujian, has officially entered service. The strategy of strengthening the military through talent has been implemented in depth, and high-quality, professional, and new-type military personnel are rapidly growing. These revolutionary advancements and historic achievements in the new era have enabled new combat capabilities to continuously accumulate momentum and be optimized and upgraded from concept to planning to practice, providing a solid fertile ground for the birth of advanced combat capabilities through military practice.
Advanced combat capabilities possess distinct characteristics of the times, innovation, and dialectical nature.
President Xi Jinping pointed out: “The military must be prepared to fight, and all work must adhere to the standard of combat effectiveness, focusing on the ability to fight and win wars.” Looking back on history, our military has grown from small to large, from weak to strong, and has continuously moved from victory to victory. A crucial lesson learned is the consistent emphasis on combat effectiveness development, the dynamic upgrading of combat capabilities, and the measurement of development effectiveness using actual combat standards. With technological progress and the development of the times, the form of warfare is rapidly evolving, and the connotation, elements, and characteristics of combat effectiveness are constantly undergoing new changes. Only by actively adapting to the development trend of the military revolution and keenly grasping the pulse of the times and the strong demands of combat effectiveness evolution can we clarify what kind of wars we will fight and how we will fight them, anchor the logical basis of war preparation, and accurately identify the direction of the military’s combat effectiveness development. Advanced combat effectiveness is an important concept proposed by President Xi Jinping in leading the modernization of national defense and the military, based on building a new type of military force system, accelerating the construction of new-quality combat effectiveness, improving the quality and efficiency of winning battles, and fulfilling missions and tasks to a high standard. It possesses distinct characteristics of timeliness, innovation, and dialectical thinking.
Advanced combat capabilities embody the development direction of military intelligence. Currently, adhering to the integrated development of mechanization, informatization, and intelligence, with mechanization as the foundation, informatization as the support, and intelligence as the guide, is an important path for our military to advance modernization. Traditional combat capabilities are based on mechanical and chemical energy, emphasizing the superposition of personnel, weapons, and forces, and focusing on the struggle for physical space such as land, sea, air, and space. New-type combat capabilities, based on traditional combat capabilities, rely more on new energy sources such as data, algorithms, and computing power, emphasizing the implantation of data elements, algorithmic elements, and cross-domain elements, and focusing on defeating the enemy in emerging fields such as the network domain, information domain, and cognitive domain. Advanced combat capabilities adapt to the new trend of future warfare leaping from “energy-dominated” to “information-dominated” and then to “intelligence-dominated.” They not only focus on the “new quality” composition of combat capabilities and emphasize the leading role of new-type combat capabilities, but also focus on the “superiority” of the application effectiveness of new-type combat capabilities, giving full play to their scale, combat realism, and systemic effects, and emphasizing the use of military intelligence to transform the combat capability generation structure and continuously improve the intelligence level of combat capabilities.
Advanced combat capability signifies a comprehensive iterative upgrade of all elements of combat capability. Essentially, advanced combat capability is high-quality combat capability, driven by innovation, empowered by technology, and enhanced by intelligence, exhibiting prominent characteristics such as high intelligence, high technology, high quality, and high integration. On the one hand, advanced combat capability requires a comprehensive iterative upgrade of all constituent elements of combat capability, ensuring that the soul of military theory, the structure of organizational form, the core of military personnel, and the support of weaponry fully implement the principles of quality first and efficiency priority, promoting quality transformation, efficiency transformation, and power transformation, and driving the widespread penetration and deep empowerment of intelligent technology into people, weapons, and their integration methods, thereby generating advanced combat capability through comprehensive element optimization. On the other hand, advanced combat capability relies more heavily on the integrated linkage of the entire military system, transforming the way combat capability is released from “points” to “areas,” the presentation of effectiveness from fragmented to aggregated, and the human-machine relationship from “master-slave cooperation” to “intelligent symbiosis,” optimizing the entire military system’s output and release efficiency of combat capability, and using the “superiority” of the system structure to generate “strength” in combat capability.
Advanced combat capabilities embody a materialist dialectical approach to military thinking. Advanced combat capabilities are not fixed, static, or passive. They are relative, representing a lead over stronger adversaries, possessing a clear advantage of being one step ahead, one point ahead, and one unit faster than the enemy. Advanced combat capabilities are dynamic; all “advanced” capabilities are evolving, a process of advanced technology leading tradition and new technologies transforming old ones. Today’s advancement does not guarantee tomorrow’s, and temporary advancement does not guarantee permanent advancement. From the perspective of ultimate operational effectiveness, “advanced” capabilities necessarily mean high efficiency defeating low efficiency, high quality crushing low quality, and strong military intelligence surpassing weak military intelligence. Advanced combat capabilities possess agency, exhibiting initiative that is not subject to external control, the ability to leverage strengths and avoid weaknesses, and the flexibility, resilience, and dynamism to adapt to the latest military developments and changes in the war environment. The original and iconic concept of advanced combat capability creatively reveals the dialectical unity of advanced and backward, quality and scale, and initiative and passivity in the generation of military capabilities. It profoundly reveals the general laws of combat capability generation, development and leap, expands the new vision of military theory, deepens the new understanding of military theory, realizes the innovative transformation and systematic reform of the constituent elements of combat capability, and opens up a new path for liberating and developing combat capability.
The concept of advanced combat capability represents a breakthrough in multiple aspects of the history of military theory development.
Standing at the forefront of the times, President Xi has profoundly grasped the laws governing the military transformation and the evolution of modern warfare in the new era. He has made theoretical innovations in combat capability building, enriched and developed the Marxist theoretical system on combat capability building, promoted the theoretical innovation and transformation of the Party’s combat capability form, transcended the logical limitations of Western theories on combat capability generation, and achieved multiple strategic value breakthroughs in the history of military thought and the history of military theory development.
This has enriched and developed the Marxist theoretical system on combat capability building. Marx and Engels profoundly understood the intrinsic connection between military and political, economic, and other social factors, scientifically grasped the essence and laws of military activities, and emphasized that “the nature and type of armed forces, as well as their characteristics, equipment, and tactics, and the organization and training methods of the troops, depend on the level of development of productive forces, on the social system, and on the class structure of society.” They formed a theoretical understanding of the constituent elements of military combat capability and the laws governing their generation and development, providing scientific guidance for the proletarian party to build its own armed forces and improve its combat capability. President Xi Jinping adheres to the Marxist military view and methodology, based on the new characteristics of the times and the new realities of the PLA’s development, and has put forward a series of concepts and propositions such as “science and technology are the core combat capability of modern warfare,” “scientific military theory is combat capability,” and “new-quality combat capability.” He scientifically revealed the generation mode and evolution law of combat capability under the conditions of the information and intelligent era, leading the PLA’s combat capability to achieve a new leap forward and enriching and developing the Marxist military theoretical conceptual system.
This has driven the innovation and transformation of the Party’s theory on combat effectiveness. Throughout the history of building and strengthening the People’s Liberation Army, our Party has always attached great importance to improving the army’s combat effectiveness. During the period of the New Democratic Revolution, our Party raised the issue of “improving the combat effectiveness of the main force,” and in practice, maintained strong combat effectiveness through extremely insightful strategic guidance, flexible strategies and tactics, rigorous training, and courageous spirit. On the eve of the founding of the People’s Republic of China, Comrade Mao Zedong clearly pointed out: “The People’s Liberation Army will always be a fighting force.” In the new era of reform and opening up and socialist modernization, Comrade Deng Xiaoping pointed out that “the army must improve its combat effectiveness,” leading our army to continuously develop its combat effectiveness through streamlining, reorganization, reform, and strengthened training. With the continuous liberation and development of productive forces, our Party emphasized “using science and technology to promote training” and “using science and technology to train troops,” promoting new improvements in combat effectiveness. Entering the new era, President Xi Jinping scientifically grasped the trend of implementing the new development philosophy and developing new-quality productive forces, focusing on achieving the Party’s goal of building a strong military in the new era. Based on emphasizing firmly establishing combat effectiveness as the sole fundamental standard, he put forward scientific conclusions such as “strengthening the construction of new types of combat forces” and “fully liberating and developing new-quality combat effectiveness,” providing important guidance for the iterative upgrading of our army’s combat effectiveness. “Advanced combat capability” is a condensation, sublimation, and innovative development of the Party’s historical experience in building combat capability. It enriches the scientific theory of the Party’s military combat capability in the new era and has become a new concept and category with great guiding significance and ideological power in Xi Jinping’s thought on strengthening the military. It lays a solid foundation for the systematization, physics, and chemistry of the Party’s military theory in the new era.
This transcends the logical limitations of Western theories of combat power generation. Engels profoundly pointed out that “the entire organization and mode of warfare of an army, and the outcome of battles related to it, depend on material, i.e., economic conditions,” which laid the historical materialist methodological foundation for combat power research. However, for a long time, technology worship and the “weaponry determinism” were prevalent in the issue of combat power construction, leading to the misconception that combat power was only about “things” and not “people.” For example, the US military once used technological superiority to completely defeat many weaker adversaries, but its “military transformation” frequently fell into the logic of “replacing combat platforms” with old weapons. The concept of advanced combat capability, starting from the foundation of new-type combat capability, uses “new” to identify technological breakthroughs, “quality” to characterize qualitative changes in combat capability structure, and “combat effectiveness” to measure the effectiveness of combat capability construction and application. It strengthens the ecosystem of combat capability generation, integrates theory, data, algorithms, talent, and organization into the productivity and combat capability fusion system, shifts the focus of combat capability from weapons competition to system confrontation, reshapes the underlying logic of combat capability generation, and forms a combat capability generation theory with Chinese characteristics. It effectively gets rid of the misconceptions of combat capability generation such as over-reliance on technology and materials, and the separation of political goals from military means, and lays a solid foundation for building China’s independent military knowledge system.
Scientifically construct an advanced combat capability generation, development, and maintenance system
President Xi Jinping emphasized: “Improving the operational efficiency of the military system and promoting the high-quality development of our armed forces.” The theme of my country’s economic and social development during the 15th Five-Year Plan period is promoting high-quality development. This is not only an inevitable choice for developing new productive forces on the new journey, but also an inevitable principle for strengthening advanced combat capabilities. We must thoroughly implement Xi Jinping’s thought on strengthening the military, deeply understand the deployment requirements of the “Suggestions,” accurately grasp the phased characteristics of the next five years and even longer, highlight the theme of promoting high-quality development, consistently uphold and strengthen the Party’s absolute leadership over the military, advance political building of the military, reform and strengthening of the military, technological strengthening of the military, talent strengthening of the military, and rule of law in the military, uphold principles and innovate in the overall planning of advanced combat capability building, construct a modern military force system with Chinese characteristics, continuously improve combat capabilities, and enhance the strategic capability to safeguard national sovereignty, security, and development interests.
We must persist in promoting the high-quality development of all elements of combat capability. In future warfare, with the continuous strengthening of new domain and new quality forces and the rapid development of technologies such as unmanned and intelligent systems, combat capability generation will exhibit a trend of comprehensive upgrading, presenting new characteristics such as three-dimensional, mobile, and efficiency-oriented optimization. We must focus on the new trends in the development of warfare, accelerate the modernization of military theory, earnestly implement President Xi Jinping’s important expositions on combat capability building, analyze the winning mechanisms of informationized and intelligent warfare, and promote the flourishing development of core combat capability theories such as military strategy, operational thinking, and military modernization. Adapting to the significantly enhanced overall, coordinated, and complex nature of military system operations, we must ensure the implementation of reform tasks, continuously optimize the military force system, and do a good job in modernizing military governance to improve the efficiency of combat capability extraction and aggregation. We must combine investment in materials with investment in people, adhere to the principle of cultivating, evaluating, and utilizing talent from a political perspective, build a military talent pool adapted to the requirements of intelligent warfare, further accelerate the development of advanced weaponry and equipment, improve the intelligence level of weaponry and equipment, implement major national defense development projects, expedite national defense science and technology innovation and the transformation of advanced technologies, and develop and build more “killer” weapons and equipment capable of defeating the enemy.
Make good use of military intelligence as a powerful engine for upgrading combat capabilities. With breakthroughs in artificial intelligence, the trend of human society moving from informatization to intelligence is also reflected in the military field. The “mast” of military intelligence has appeared on the “sea level” of the evolution of warfare, and information warfare with intelligent characteristics is beginning to take shape. It is imperative to accelerate the coordinated construction and application of network information systems. Networks are the carriers and channels of information and intelligence; under modern warfare conditions, network information systems have become a core support. We must coordinate the construction and application of network information systems, strengthen the development and utilization of data resources, achieve interconnection and interoperability between combat units and various weapon systems, build a distributed, reconfigurable, and resilient combat network, and accelerate the improvement of network information system construction and service support capabilities for combat readiness. It is also imperative to build an intelligent military system, accelerate the transformation and application of cutting-edge technologies in the field of artificial intelligence to the military, accelerate the construction of unmanned intelligent combat forces and countermeasure capabilities, and enable military intelligence to better and faster integrate into, drive, and empower the system.
Cultivating the integrated development of new-type productive forces is the lifeblood of combat capability building. In today’s world, the technological revolution, industrial transformation, and military revolution are accelerating, and national strategic competitiveness, social productivity, and military combat capability are becoming increasingly interconnected, mutually influential, and mutually supportive. Promoting the efficient integration and two-way synergy between new-type productive forces and new-type combat capabilities is a fundamental requirement for achieving the unity of a prosperous nation and a strong military, and it is the lifeblood of accelerating the development of advanced combat capabilities. We must innovate the models of combat capability building and application, actively guide the direction of new-type productive forces and new-type combat capabilities according to the needs of military struggle, improve and perfect institutional mechanisms for demand alignment, planning coordination, and resource sharing, highlight the top priority of promoting strategic capabilities in emerging fields, vigorously promote the development and integrated application of new types of military talent, new types of combat equipment, new organizational forms, and new tactics, continuously consolidate the material foundation for social production to serve future warfare, accelerate the supply of new-type combat capabilities, and ensure that wartime military combat capabilities and social productivity are effectively focused and precisely released on the battlefield, so as to win future wars with a strong and sustainable overall national strength.
Emphasizing realistic combat training as a crucial lever for catalyzing combat effectiveness is essential. Realistic combat training serves as a bridge and means to achieve efficient integration of personnel, weaponry, and organizational systems. It possesses a strong capacity for integrating and transforming various resources and elements involved in combat capability generation, and is a vital pathway for generating, developing, and strengthening advanced combat capabilities. President Xi Jinping, with profound insight into the key to developing advanced combat capabilities, has called for “strengthening the consistency between combat and training, adhering to the principle of training guided by combat and promoting combat through training, ensuring training according to actual combat requirements, and achieving the integration of operations and training,” and “improving the level of full-cycle, refined training management,” thus pointing out the “realistic” path for generating advanced combat capabilities. It is necessary to deepen strategic and operational planning, solidly advance realistic combat military training, strengthen the integration of combat capability systems, innovate combat capability construction and application models, vigorously carry out modern training in conjunction with combat readiness building, joint exercises and training, and the application of diversified military forces, strengthen targeted and confrontational training, and continuously improve the combat capabilities of the troops.
(The author is a researcher at the Xi Jinping Thought on Socialism with Chinese Characteristics for a New Era Research Center of the National Defense University.)
People’s Daily (November 17, 2025, Page 9)
現代國語:
戰鬥力是一支軍隊興衰成敗的最終決定力量,不僅影響武裝力量的作戰方式和實際效能,更維繫著一個國家和一個民族的生存安全和長治久安。先進戰鬥力,是習主席深刻論述「新質戰鬥力」這個原創性概念標識性概念之後,我們黨提出的關於戰鬥力建設的最新觀點。 2019年1月,習主席在中央軍委會軍事工作會議中指出:「要加強新型作戰力量建設,增加新質戰鬥力比重。」此後,習主席多次論述這一重要問題,強調「打造強大戰略威懾力量體系,增加新域新質作戰力量比重」「推動新質戰鬥力加速提升」等。正是在新時代我軍新質戰鬥力形成發展的實踐基礎上,「先進戰鬥力」這個新思想新論斷應運而生。先進戰鬥力是更高級形態的戰鬥力,以新質戰鬥力為引領和支撐,強調新質戰鬥力的規模化、實戰化、體系化運用,注重理論創新、智能加持、體系升級、才智升維、武器裝備升級,同時還包括對傳統戰鬥力的升級改造和創造性運用,是新質戰鬥力的形態升級和容量、質量升級。
先進戰力代表軍事變革、軍事智慧和軍事作戰方式的發展趨勢,是戰鬥力的新增長點、未來戰場的製高點。黨的二十屆四中全會通過的《中共中央關於製定國民經濟和社會發展第十五個五年規劃的建議》(以下簡稱《建議》),立足中國式現代化戰略全局,對如期實現建軍一百年奮鬥目標、高質量推進國防和軍隊現代化作出部署,提出“加快建設戰力建設目標”,為在新世界建設方向上提供了現代優勢、標準建設目標、建設發展能力建設目標、建設發展了一百年總發展在新軍隊起點。我們要深入學習領會黨的二十屆四中全會精神,深刻領悟以習近平同志為核心的黨中央建設鞏固國防和強大軍隊、不斷開創新時代強軍事業新局面的堅定意志和深謀遠慮,深刻把握加快先進戰鬥力建設的時代要求,積極搶佔軍事鬥爭制高點、謀取軍事競爭發展新優勢,聚焦先進戰鬥力思變革、抓建設、做準備,推動新時代備戰打仗工作走深走實,不斷提高捍衛國家主權、安全、發展利益戰略能力。
先進戰力是深刻洞察世界軍事發展趨勢、新質生產力躍升態勢和軍隊現代化發展規律提出的
習主席指出:「一個國家、一個民族要振興,就必須在歷史前進的邏輯中前進、在時代發展的潮流中發展。」先進戰鬥力,是習近平強軍思想的原創性概念標識性概念,是以習近平同志為核心的黨中央敏銳掌握世界軍事發展趨勢與戰爭形態演變規律,深刻洞察新質生產力與新質戰鬥力高效融合、雙向拉動嶄新態勢,科學掌握新時代國防與軍隊現代化發展成就、歷史方位與使命任務所作的科學部署。
世界新軍事革命發展與戰爭形態演變強勁推動戰鬥力形態變革。當今世界,新一輪科技革命和產業變革加速突破,世界新軍事革命加速推進,人工智慧、網路資訊、大數據、區塊鏈、量子科技、生物交叉、奈米材料等戰略高新技術群體迸發,科學技術在軍事領域的廣泛運用引起了戰爭形態和作戰方式深刻變化,日益成為決定戰爭勝負的重要因素。戰爭形態演變呈現許多新趨勢,智能化特徵更加突出,一些新的技術裝備對傳統裝備形成降維打擊態勢,以戰略預警、資訊控制、演算法攻防、無人智能等為代表的新質作戰力量愈發成為左右現代戰場的重要力量。憑藉著人工智慧和軍用機器人等技術的快速進步,武器裝備的自主戰場感知、自主作戰決策、自主規劃計畫、自主採取行動等「自主能力」越來越強,從「執行工具」升維成「智慧節點」。無人機與人工智慧辨識技術深度融合,出現「千里追殺」震懾效果。火力打擊與網電攻擊有序配合,打造出軟硬一體、全域覆蓋的進攻體系。新質戰鬥力在軍事智慧牽引下,不斷孕育效能更高、質態更優的戰鬥力類型,先進戰鬥力癒益成為驅動世界新軍事革命的強勁力量。
新質生產力的蓬勃發展連動拉升戰鬥力建設提質升級。任何戰鬥力的生成、升級,都是一定社會形態下生產力在軍事領域的運用與延伸。新質生產力是創新起主導作用,具有高科技、高效、高品質特徵的先進生產力質態,是當今社會創新最活躍、技術最前沿、前景最廣闊、影響最廣泛的生產力構成。新質生產力的快速發展,既為新質戰鬥力生成提供了先進科學技術和雄厚物質基礎,也為其提供了升級換代的牽引力、支撐力,成為重塑戰爭形態、重建作戰體系、重組指揮要素的關鍵變數。新質戰鬥力源自關鍵共通技術、前沿引領技術與顛覆性技術創新突破,依托新興科技手段與先進作戰理念,全要素植入資訊化基因、融進網路化體系,運用新科技、新裝備、新戰法,使軍事體系呈現出謀略導能、資訊賦能、網路聚能、科技強能、體系釋能等新優勢。隨著新質戰鬥力的快速發展和廣泛運用,由其主導的先進戰鬥力形態必然顯現出來,成為推動現代軍事體系變革發展的有力引擎。
新時代國防與軍隊現代化重大成就奠定先進戰鬥力厚實基礎。新時代以來,習主席立足中華民族偉大復興戰略全局和世界百年未有之大變局,用強軍目標審視和牽引戰鬥力建設,推動戰力各要素的活力競相迸發。深化國防與軍事改革,形成軍委管總、戰區主戰、軍種主建新格局,先後組成調整軍事太空部隊、網路太空部隊、資訊支援部隊等新型作戰力量體系,實現了組織架構和力量體系整體性、革命性重塑。統籌推動戰略性新興產業和新型作戰力量發展,取得一系列重大成果。加速武器裝備更新換代,以新型戰車、艦載機、殲擊機等為代表的新型四代裝備列裝部隊,以「東風—5C」液體洲際戰略核子飛彈等為代表的大國重器亮相閱兵場,首艘電磁彈射型航母福建艦正式入列。人才強軍戰略深入實施,高素質專業化新型軍事人才加速成長。新時代這些革命性進展和歷史性成就,使新質戰鬥力由概念到規劃、到實踐,不斷累積成勢、優化升級,為先進戰鬥力誕生提供了堅實的軍事實踐沃土。
先進戰鬥力具有鮮明的時代性、創新性、辯證性
習主席指出:「軍隊是要準備打仗的,一切工作都必須堅持戰鬥力標準,向能打仗、打勝仗聚焦。」回顧歷史,我軍從小到大、由弱到強,不斷從勝利走向勝利,一條重要經驗,就是始終注重戰鬥力建設,推進作戰能力動態衡量,用實戰標準建設成效。隨著科技進步和時代發展,戰爭形態加速演變,戰鬥力內涵、要素和特徵不斷發生新的變化。只有積極適應軍事革命發展趨勢,敏銳掌握戰鬥力演變的時代脈動和強勁需求,才能明晰未來打什麼仗、怎麼打仗,錨定戰爭準備的邏輯基點,找準軍隊戰鬥力發展方向。先進戰鬥力,就是習主席在領導國防和軍隊現代化的時代征程中,基於打造新型軍事力量體系、加速新質戰鬥力建設、提高勝戰能力質效、高標準履行使命任務提出的重要概念,具有鮮明的時代性、創新性、辯證性等特徵。
先進戰力體現軍事智慧化的發展方向。目前,堅持機械化資訊化智能化融合發展,以機械化為基礎,以資訊化為支撐,以智能化為引領,是我軍推進現代化的重要路徑。傳統戰鬥力以機械能、化學能為基底,注重人員、武器、力量疊加,聚焦陸海空天等實體空間爭奪。新質戰鬥力在傳統戰力基礎上,更依托數據、演算法、算力等新型能量,注重資料要素、演算法要素、跨域要素植入,聚焦網路域、資訊域、認知域等新興領域制敵謀勝。先進戰鬥力順應未來戰爭將從「能量主導」向「資訊主導」再向「智慧主導」躍遷的新趨勢,不僅關注戰鬥力的「新質」構成,強調新質戰鬥力發揮主導地位,更關注新質戰鬥力的應用效能之“優”,發揮其規模化、實戰化、體系化戰力提升
先進戰鬥力意味著戰鬥力全要素迭代升級。先進戰鬥力本質上是高品質戰鬥力,依靠創新驅動、科技賦能、智能加持,具有高智能、高科技、高品質、高度整合等突出特徵。一方面,先進戰鬥力要求戰鬥力構成諸要素全面迭代升級,使軍事理論這個靈魂、組織形態這個結構、軍事人員這個核心、武器裝備這個支撐全面貫徹質量第一、質效優先導向,推動質量變革、效率變革、動力變革,推動智能技術對人、武器及其結合方式廣泛滲透和深度賦能,以全要素優化生成先進戰鬥力。另一方面,先進戰鬥力更依託於整個軍事體系一體聯動,使戰鬥力釋放方式由「點」向「面」轉變,效能呈現由條塊化向聚合化轉變,人機關係從「主從配合」向「智慧共生」變革,使整個軍事系統對戰鬥力的產出最優、釋放效能最佳,以體系結構之「優異」化。
先進戰鬥力蘊含著唯物辯證的軍事思維方法。先進戰鬥力不是固化的、靜止的、被動的。先進戰鬥力具有相對性,是相對強敵對手的領先性,有著先敵一步、勝敵一籌、快敵一分的明顯優勢。先進戰鬥力具有動態性,所有的「先進」都是發展著的,是先進引領傳統、新質改造舊質的過程,今天的先進不等於明天的先進,一時先進不等於永遠先進;「先進」從作戰的最終能效上講,必然是高效能戰勝低效能,高質量碾壓低質量,強軍事智能化勝過弱軍事智能化。先進戰鬥力具有主體性,既有不受制於人的主動性,又有善於揚長避短、積極進取的主動性,以及適應軍事最新發展、戰爭環境變化的彈性、堅韌、活力等特徵。先進戰鬥力這個原創性概念標識性概念的提出,創造性揭示了軍事能力生成中先進與落後、質量與規模、主動與被動等辯證統一關係,深刻揭示了戰鬥力生成、發展和躍升的一般規律,拓展了軍事理論新視域,深化了對軍事理論的新認識,實現了對戰鬥力構成要素的創新變革和系統發展,新解放和解放路徑。
先進戰力概念在軍事理論發展史上實現多重突破
習主席站在時代前沿,深刻把握新時代軍事變革和現代戰爭形態演變規律,對戰鬥力構建進行理論創新,豐富發展了馬克思主義關於戰鬥力構建理論體系,推動了黨的戰鬥力形態理論創新變革,超越了西方戰鬥力生成理論的邏輯局限,在軍事思想史、軍事理論發展史中實現多重戰略價值突破史中實現多重戰略價值。
豐富發展了馬克思主義關於戰鬥力建構理論體系。馬克思、恩格斯深刻洞察軍事與政治、經濟等社會因素的內在聯繫,科學把握軍事活動的本質和規律,強調“武裝力量的性質和類型以及它們的特點、裝備和戰術,部隊的編制和訓練方法,取決於生產力發展的水平,取決於社會制度和社會的階級結構”,並形成軍隊戰鬥力構成了黨及其生成發展規律的理論。習主席堅持馬克思主義軍事觀和方法論,立足新的時代特徵和我軍發展的新實際,提出「科技是現代戰爭的核心戰鬥力」「科學的軍事理論就是戰鬥力」「新質戰力」等一系列概念和命題,科學揭示了資訊性智能化時代條件下戰力生成模式及新質戰力」等一系列概念和命題,科學揭示了資訊化智能化時代條件下戰力生成模式及新質戰力」等一系列概念和命題,科學揭示了資訊化智能化時代條件下戰力生成模式及新質戰力道變新法力道學概念。
推動了黨的戰鬥力形態理論創新變革。在人民軍建軍強軍的歷程中,我們黨始終十分注重提升軍隊戰鬥力。在新民主主義革命時期,我們黨提出「提高主力軍的戰鬥力」問題,並在實踐中以極為高明的戰略指導、機動靈活的戰略戰術、刻苦訓練和勇敢精神,保持了強大戰鬥力。毛澤東同志在新中國成立前夕明確指出:“人民解放軍永遠是一個戰鬥隊。”在改革開放和社會主義現代化建設新時期,鄧小平同志指出“軍隊要提高戰鬥力”,領導我軍通過精簡、整頓、改革和強化訓練等不斷發展戰鬥力。隨著不斷解放和發展生產力,我們黨強調“科技興訓”“科技練兵”,推動戰鬥力建設有了新的提高。進入新時代,習主席科學把握貫徹新發展理念、發展新質生產力的時代大勢,著眼實現黨在新時代的強軍目標,在強調牢固樹立戰鬥力這個唯一的根本的標準基礎上,提出“加強新型作戰力量建設”“充分解放和發展新質戰鬥力”等科學論斷,為我軍戰鬥力迭代升級提供重要引領。 「先進戰鬥力」是對黨的戰鬥力建設歷史經驗的凝練昇華和創新發展,豐富了新時代黨的軍事戰鬥力形態科學理論,成為習近平強軍思想中極具引領性和思想力的新概念新範疇,為新時代黨的軍事理論的體系化學理化奠定堅實基礎。
超越了西方戰鬥力生成理論的邏輯限制。恩格斯深刻指出“軍隊的全部組織和作戰方式以及與之有關的勝負,取決於物質的即經濟的條件”,這為戰鬥力研究奠定了歷史唯物主義方法論基礎。但在戰鬥力建構問題上,很長一段時間,技術崇拜、「武器裝備決定論」等很有市場,出現了論戰鬥力只見「物」不見「人」的誤解。例如,美軍曾以技術代差,完敗很多弱小對手,其「軍事轉型」卻頻繁陷入從舊武器到新武器的「作戰平台替換」邏輯。先進戰鬥力概念,堅持從新質戰鬥力的基點出發,以「新」標識技術突變,以「質」表徵戰鬥力結構質變,以「作戰質效」衡量戰鬥力建設運用效果,強化戰鬥力生成的生態體系,將理論、數據、演算法、人才、組織納入生產力、戰鬥力融合拉動體系,把戰鬥力重心從武器比拼轉向體系對抗,重塑了戰鬥力生成底層邏輯,形成了具有中國特色的戰鬥力生成理論,有效擺脫那些過度依賴技術與物質、政治目標與軍事手段相脫離等戰鬥力生成的誤區,為構建中國自主的軍事知識體系打下堅實的軍事知識體系。
科學建構先進戰鬥力生成、建構與維護體系
習主席強調:「提升軍事系統運作效能,推動我軍高品質發展。」「十五五」時期我國經濟社會發展的主題是推動高品質發展,這不僅是新旅程發展新質生產力的必然選擇,也是加強先進戰鬥力建設的必然遵循。我們要深入貫徹習近平強軍思想,深刻領會《建議》部署要求,把準未來五年乃至更長時間階段性特徵,突出推動高品質發展這個主題,一以貫之堅持並加強黨對軍隊的絕對領導,推進政治建軍、改革強軍、科技強軍、人才強軍、依法治作戰,守正創新籌資先進戰力強化為強國作戰能力、建構安全性強軍;
堅持推進戰鬥力構成的全要素高品質發展。未來作戰,隨著新域新質力量不斷加強和無人智能等技術快速發展,戰鬥力生成將出現全要素升級的態勢,呈現立體聚優、動中聚優、效能聚優等新特徵。要著眼戰爭形態發展新趨勢,加速軍事理論現代化步伐,認真貫徹實習主席關於戰鬥力建設重要論述,研析資訊化智能化戰爭制勝機理,推動軍事戰略、作戰思想、軍隊現代化建設等戰力主幹理論繁榮發展。適應軍事系統運作整體性、協同性、複雜性顯著提升的實際,抓好改革任務落地,持續優化軍事力量體系,做好軍事治理現代化這篇大文章,提升戰鬥力萃取和聚合效能。把投資於物與投資於人結合起來,堅持從政治上培養、考察、使用人才,打造適應智能化戰爭要求的軍事人才方陣,進一步加快先進武器裝備發展,提升武器裝備智能化程度,實施國防發展重大工程,加緊國防科技創新和先進技術轉化,研發建造更多製強勝強的「殺手鐧」武器裝備。
用好軍事智慧化這個戰鬥力質態升級的強勁引擎。隨著人工智慧領域技術的突破,人類社會由資訊化向智慧化的發展趨勢也反映在軍事領域,軍事智慧化的「桅杆」已經出現在戰爭形態發展演進的「海平面」上,具有智慧化特徵的資訊化戰爭顯露雛形。必須加快統籌網路資訊體系建置運用。網路是資訊和智慧的載體和通道,在現代戰爭條件下,網路資訊體系成為核心支撐。要統籌網路資訊體系建置運用,加強資料資源開發利用,實現作戰單元、各類武器系統之間的互聯互通,建構分散式、可重構、強韌性的作戰網絡,加快把網路資訊體系建構和服務支撐備戰打仗能力搞上去。必須建構智慧化軍事體系,加速人工智慧領域前沿技術成果向軍事領域的轉換應用,加速無人智慧作戰力量及反制能力建設,使軍事智慧更好更快融入體系、驅動體系、賦能體系。
涵養一體融合這個戰鬥力建設的源頭活水。當今世界,科技革命、產業變革、軍事革命加速發展,國家戰略競爭力、社會生產力、軍隊戰鬥力三者相互關聯、相互影響、相互支撐越來越緊密。推動新質生產力同新質戰鬥力高效融合、雙向拉動,是實現富國與強軍相統一的根本要求,是加速先進戰鬥力建設的源頭活水。要創新戰鬥力建設與運用模式,根據軍事鬥爭需要積極牽引新質生產力、新質戰鬥力前進方向,健全完善需求對接、規劃銜接、資源共享等製度機制,突顯推進新興領域戰略能力建設這個重中之重,大力推動新型軍事人才、新型作戰裝備、新型組織形態、新型戰法建設發展和融合運用,持續打牢社會生產服務未來戰爭的物質基礎,加速新質戰鬥力供給,確保戰時軍隊戰鬥力和社會生產力在戰場上有效聚焦、精準釋能,以強大持續的國家整體力量打贏未來戰爭。
突顯實戰化訓練這個戰鬥力催化的重要抓手。實戰化訓練,是實現人與武器裝備、組織體系高效融合的橋樑和手段,對戰鬥力生成的各種資源和要素具有很強的整合轉化功能,是生成、發展和強化先進戰鬥力的重要途徑。習主席深刻洞察發展先進戰鬥力的要害所在,要求“強化戰訓一致,堅持以戰領訓、以訓促戰,做到按實戰要求訓練,實現作戰和訓練一體化”“提高全週期、精細化訓練管理水平”,為先進戰鬥力指明了“實戰化”生成路徑。要深化戰略和作戰籌劃,紮實推進實戰化軍事訓練,加強作戰能力體系集成,創新戰鬥力建設和運用模式,結合鬥爭塑勢、聯演聯訓和多樣化軍事力量運用大力開展現代化練兵,加強針對性對抗性訓練,推動部隊實戰能力不斷提升。
(作者為國防大學習近平新時代中國特色社會主義思想研究中心研究員)
《 人民日報 》( 2025年11月17日 09 版)
汤俊峰
2025年11月17日08:37 来源:人民网-人民日报
中國原創軍事資源:https://theory.people.com.cn/n1/2025/