Chinese Analysis of Cyber Space Deterrence – Important Strategic Points
淺析網絡空間威懾的特徵、類型和運用要點
Chinese People’s Liberation Army Academy of Military Sciences Yuan Yi
January 04, 2016
Editor’s note: When both opposing parties have the ability to ensure intrusion and damage to the other party’s network, they can bring about two-way network containment, making the two parties obliged to comply with the game rules that do not attack each other’s network under certain conditions, forming an invisible safety valve. Even international conventions or conventions that do not attack each other’s networks will be formed. The cyberspace has thus become a strategic area that can produce a huge deterrent effect. After the deterrence of cyberspace followed by nuclear deterrence, it began to enter the strategic vision of big country politicians and military strategists. Studying the characteristics, types, and points of use of cyberspace deterrence must be taken into consideration and necessary action by the Internet powers and the cyber force.
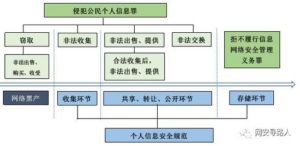
With the increasing dependence of human society on cyberspace, cyberspace has become the “second type of living space” for human production and life and the “fifth-dimensional combat space” for military confrontation. Countries around the world have fiercely competed for the dominant rights, control rights, and discourse power of cyberspace. The competition in the cyberspace has reached the level of human survival, national destiny, and success or failure of military struggles. Thinking about cyberspace deterrence capacity building has great practical and theoretical value.
First, analysis of the advantages and disadvantages of cyberspace deterrence
Cyberspace deterrence refers to the actions and actions taken in the cyberspace to demonstrate and control enemy cyberspace, and to control the enemy’s physical space through cross-domain cyberspace, so as to achieve the goal of destroying enemy forces, stopping the enemy, blocking the enemy, and preventing deterrence. A form of strategic deterrence for the enemy’s purpose. Compared with the physical space, the “virtual and real duality” of network space and the uniqueness of network warfare compared with traditional combat styles have determined that the advantages and disadvantages of cyberspace deterrence are very obvious.
(A) The advantages of cyberspace deterrence
The advantages of cyberspace deterrence are mainly reflected in the following: First, the deterrence approach has become more civilized and humane. Compared with nuclear, chemical, and chemical weapons based on physical, biological, and chemical killing mechanisms, the direct killing and destructive effects of cyber warfare weapons are much smaller than the former. Normally, they will not cause permanent damage and pollution to the natural environment, nor will they cause large numbers of people. Casualties and humanitarian disasters. Second, deterrence costs are inefficient. The network warfare weapons are dominated by viruses, Trojans and other software. The costs are relatively low, and the technical threshold is low. The destructive effects are rather alarming. The network defense points are multi-faceted, and they are hard to prevent. To increase the level of network security by one level, the input cost will increase exponentially. The contrast between the low cost of cyber offense and the high cost of cyber defense makes the offensive and defensive performance of the network a feature of “spirit shield”, and the cyber warfare weapon is thus called “the atomic bomb of the poor country”. The third is that deterrence methods are diverse and practical. The variety of cyber warfare weapons and the multiple goals of cyber attacks have determined that there are diversified cyberspace deterrent methods to choose from. The effects of cyberattacks are recoverable to a certain extent. As long as the application is properly implemented, the risk of causing war and escalating the war is relatively small. In a sense, the deterrence value of nuclear weapons is far greater than the value of actual combat, and cyber warfare weapons are both practical values and deterrence values. Fourth, the use of repeatability and deterrence is strong. Once the “nuclear threshold” crosses, a full-scale nuclear war will erupt, and the two sides at the nuclear balance will fall into a state of mutual destruction. The easy implementation of nuclear deterrence, especially nuclear deterrence against non-nuclear countries, will also be condemned by international public opinion. These factors are all The use of nuclear deterrence is greatly limited. The deterrence of software and hardware and the controllable characteristics of cyberspace deter- mine the flexibility and control of deterrence in light of the changes and needs of the military struggle. It can be used in advance, used throughout, and used repeatedly. It has strong flexibility.
(B) Defects in cyberspace deterrence
The deterrence of cyberspace is mainly reflected in: First, the credibility of the deterrence effect has not been fully verified. The credibility of nuclear deterrence has been verified in actual combat. However, as of now, the real network war has not really exploded. People’s astonishing destructive power over cyber warfare is more of a speculation and worry. The real power of cyber warfare can only be convincing after being tested by actual combat. Second, the reliability of deterrence measures is not very high. Network warfare is a dynamic process of continuous offensive and defensive interaction between the two sides of the enemy and me. The characteristics of network confrontation and technicality determine that the network warfare attack has greater uncertainty and may not achieve the desired operational objectives, which will greatly reduce the effectiveness of deterrence. . For example, when the enemy performs cyberspace deterrence, if the enemy takes various effective defense measures in a timely manner, it will increase the difficulty of its own cyber attack and reduce the damage, and even lead to the failure of the attack. Third, the controllability of deterrence scope needs further improvement. As one of the important weapons of cyber warfare, viral weapons have strong dissemination, poor controllability, and a wide range of influence. It is difficult to launch targeted and targeted attacks on enemy computers and networks. If it can’t control its effective scope, it will spread to third-party neutral countries and even make itself a victim. As a result, the use of virus weapons suffers from the use of “imposed rats.” The fourth is the selective limitation of deterrence objects. Nuclear deterrence is clear and effective for any country, and the effectiveness of cyberspace deterrence has a lot to do with the level of informatization of enemy countries. Cyberspace deterrence is extremely effective for countries with a high degree of informatization, and for those underdeveloped countries with weak information infrastructure and weak network dependence, it is difficult for them to exert results, or even completely ineffective. Fifth, the organization of deterrence is relatively complicated. All nuclear powers in the world implement centralized and unified management of strategic nuclear forces. Command and control powers are highly centralized. When organizations implement nuclear deterrence operations, they can accurately control each combat unit, and the organization is well-executed. The implementation of the deterrence of cyberspace involves many forces such as investigation, control, defense, and control. It has many personnel and large scales and is scattered among different departments and units in the military and the military. It is very complicated to organize and it is difficult to form a synergy.
Second, the main types of cyberspace deterrence
The cyberspace deterrence includes four types: cyberspace technology test deterrence, cyberspace equipment demonstration deterrence, cyberspace operational deterrence deterrence, and cyberspace operational deterrence. Among them, the first three are demonstrative deterrence, and the latter is actual deterrence.
(A) Cyberspace Technology Test Deterrence
The cyberspace technology test deterrence is a field in the field of cyber warfare. It constantly conducts preliminary exploratory experiments on new concepts of warfare, new experiments on the effectiveness of attack mechanisms and tactics, and practical experiments on the weaponization of new technologies. The outside world is disclosed to demonstrate its strong strength in the basic research of information technology and its enormous potential for transforming it into a cyber warfare capability to achieve deterrence. At present, network offensive and defensive technology is still developing rapidly. A breakthrough in a key technology will often have a significant impact on cyberspace security and operations, and even lead to revolutionary changes. Whoever preempts the strategic commanding heights of the network offensive and defensive technology, who will be able to achieve a clear advantage in the future of network warfare.
(B) Cyberspace Equipment Demonstration
The demonstration of cyberspace equipment deterrence is the development of network warfare equipment development planning, technology development, target testing, stereotyped production and other development stages. According to the needs of the appropriate disclosure of network warfare equipment models, performance, characteristics, parameters and development schedule, etc. Reach the purpose of deterring opponents. There are two main ways: one is through public disclosure in official media such as national defense white papers, diplomatic bulletins, and newspapers, periodicals, and large-scale websites; and the other is through online social media or other unofficial. The channel has deliberately leaked equipment-related information and implemented hidden deterrence. The cyber space equipment demonstrates deterrence. On the one hand, it can invent new cyber-warfare equipment with new mechanisms and new concepts and render its unique combat capabilities. On the other hand, it can deliberately exaggerate the operational effectiveness of existing cyber warfare equipment. There are facts in the virtual reality, there is something in the real, and the implementation of fuzzy policies, so that the other party can not understand their true situation and strength, resulting in fear and jealousy. For example, the U.S. military’s “Shuute” on-board network power system has been put into practical use several times and poses a serious threat to the air defense systems of its hostile countries. However, its basic principles, working mechanisms, and combat technical indicators have not been publicly disclosed. It has not been completely mastered by other countries and has remained in a state of secrecy. It is difficult to distinguish between reality and reality and has played a very good deterrent effect.
(3) Deterrence in cyberspace operations exercises
The deterrence of cyberspace operations exercises is to conduct drills in cyberspace through virtual or virtual methods, and use various media channels to show potential war opponents their own cyber warfighting capabilities, strengths and determinations in order to achieve deterrence. Cyberspace operations can be divided into two kinds: actual drills and virtual exercises. The former is usually carried out nationwide or in alliance with allies, and is generally based on the joint exercise of military space and space defense operations. In recent years, the United States and its allies have held “Network Storm” series of cyber warfare exercises and “Shriver” series of space-network space exercises, which have demonstrated the mobilization strength, overall defense level, and the implementation of cyber warfare. Determination. The latter is usually held at the national large-scale network integrated shooting range, and is generally based on the offensive actions of the military professional cyber warfare forces.
(D) Deterrence in cyberspace operations
The deterrence of cyberspace operations is the actual deterrence of attacking specific opponents by deterring opponents with certain attacks. There are two opportunities for its use: First, when one’s own side is aware that the enemy is about to wage a war on one’s own side, one’s own choice of the key cyber targets of the enemy’s key defenses will be targeted to combat them, and preventive and deterrent deterrence will be implemented; When the Party initiates a tentative cyber attack on its own side and implements cyberspace deterrence, it must immediately conduct effective retaliatory and disciplinary deterrence. There are many types of cyber warfare operations that have deterrent effects. For example, infiltrate the enemy’s telecommunications network, send a large number of anti-war messages to the enemy’s citizens, and attack the enemy’s power grid, resulting in a short-term blackout of major cities in the enemy’s power; attacking the enemy’s broadcast television networks and inserting their own broadcasts during prime time. Special video programs; etc.
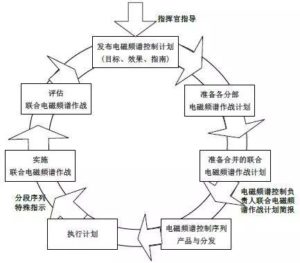
Third, the use of cyberspace deterrence points
The general requirements for the use of cyberspace deterrence are: combination of wartime and warfare, with strength, actual display capability, and determination, strive to demonstrate deterrence with small battles, ensure deterrence with strikes, and achieve deterrence with a small price. Specifically, the following points should be achieved.
(A) Combination of peacetime and long-term preparation
“Frozen feet, not a cold day.” Successful implementation of cyberspace deterrence requires a combination of peacetime and warfare, and we must fully and carefully prepare for peacetime. The first is to conduct comprehensive and thorough network reconnaissance. Requires the combination of spying, reconnaissance and technical reconnaissance, wireless reconnaissance, and cable reconnaissance. Conduct long-term and continuous network reconnaissance of enemy network targets, gradually understand the basic conditions of the enemy’s network, draw a picture of its network topology, and in particular analyze and find all kinds of soft enemies. Hardware system vulnerabilities. The second is to conduct a large number of effective strategic presets. Using hacking methods, secretive infiltrate all types of networks through the use of system vulnerabilities or password cracking, leaving the back door, setting up a springboard machine, and laying down logic bombs and Trojans to set a breakthrough for launching cyber attacks in the future. The third is to conduct pre-prepared cyber defenses. When deterring cyberspace deterrence against the enemy, one must adjust the deployment of network defenses in advance, make the enemy’s pre-designed attack path, anticipate the use of system loopholes, and plan to implement an attack plan that is difficult to implement, or the effect of implementation is greatly reduced to minimize the enemy’s Losses caused by cyber retaliation.
(B) careful decision-making, control strength
Sun Tzu said: “The Lord must not anger and raise a teacher. Cyberspace deterrence is a strategic game behavior between countries, especially with deterrence and sensitivity. It must be rational, beneficial, and tangible. It must not be abused because of the low threshold of deterrence. Otherwise, its effect may be counter-productive. . Cyberspace deterrence has a high requirement for combat intensity control. On the one hand, if the intensity is too small, the enemy’s government and people will not have fear and will not achieve the deterrent effect they deserve. The other party may also use the same methods to implement anti-deterrence, eventually leading to confrontational escalation and deterring one’s own deterrence. On the other hand, if it is too strong, it will cause huge economic losses and casualties to the enemy countries. This will cause the condemnation of the international community and the hatred of the enemy governments and people. It may trigger the enemy’s use of conventional forces to carry out large-scale revenge. Nuclear countries may even Nuclear power may be used. This will not only stop the war but will also play a role in warfare.
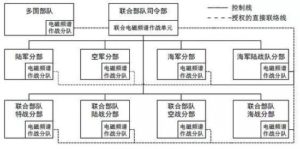
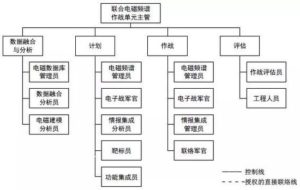
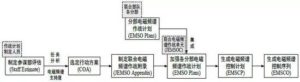
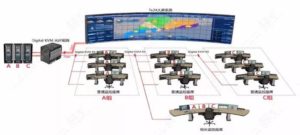
(III) Unified command and careful organization
The implementation of the deterrence of cyberspace requires centralized command, unified planning, and good coordination. The first is meticulous organization of strength. Uniformly organize the four forces of military investigation, attack, defense, and control, and actively coordinate the strength of the cyber warfare forces of all parties to form a joint force. In particular, it is necessary to organize and coordinate the strength of civil non-professional cyber warfare, especially patriotic hacking, so that there can be no phenomenon of “blindness” so as to avoid triggering friction, escalating fire, causing an escalation of cyber warfare, or prematurely exposing attack intentions and giving people a handle. , leading to uncontrollable situations or failure of operations. The second is to select the target. Should choose a wide range of influence, easy to produce a clear deterrent effect of the goal. For example, broadcast television channels with the highest ratings, portals with a large number of visitors, and wireless communication networks with numerous users. It is not possible to choose attacks that are irrelevant, insignificant, and indifferent to the target. They can easily be mistaken for cybersecurity incidents created by ordinary hackers and do not achieve the desired deterrent effect. In addition, we must also consider the constraints of international law and war laws. We must not choose targets that are easy to cause humanitarian disasters. We should try our best not to select the network goals of railways, aviation, finance, and medical departments so as not to arouse condemnation and resentment from the international community and the people of the other side. The third is the precise control of the process. Prior to the deterrent strikes in cyberspace, it is necessary to publicize the momentum through extensive public opinion, issue warnings to the enemy countries, and declare the justice of their actions to the world in order to gain the understanding and support of international public opinion. In order to highlight the deterrent effect, one can highly announce the target of the enemy’s network to be attacked, break through the enemy’s layered network defenses, and implement a resolute and effective cyber attack. If necessary, the network attack effect can be resumed regularly to show its superiority. The cyber attack technology and means make the enemy’s decision makers and the public have a sense of frustration that is hard to defend and difficult to parry, thus forming a strong shock effect.
(4) Combining actual situation with actual situation, focusing on strategy
The grandson said that “it is not possible to show and not to use it,” and it is used to deter online space. Its main points are summarized as “showing without propaganda, advocating without showing.” “Indicating nothing” means that it is difficult to track and locate using cyber attacks and conduct cyber attacks on specific targets. However, it is not done for others to announce that they are doing their own thing. It not only demonstrates their own capabilities, but also makes the enemy’s suspicion of doing their own thing. However, there is no evidence and it cannot be pursued. “Proclaiming but not showing” is the publicity or inadvertent disclosure of the type, performance, and characteristics of the advanced cyber warfare equipment developed or fabricated by the company, deliberately exaggerating its combat effectiveness, falsifying facts, and integrating facts and facts, so that the enemy can’t understand its true strength. , resulting in a deterrent effect. The cyber warfare operations have the characteristics of difficulty in tracking and traceability and complexity in forensics. The initiating party can either admit or deny it, or push the responsibility to civil hacker organizations. (Source: China Information Security).
Original Communist Mandarin Chinese:
編者按:當敵對雙方都具有確保侵入破壞對方網絡的能力時,就可以帶來雙向網絡遏制,使得雙方不得不在一定條件下,遵守互不攻擊對方網絡的遊戲規則,形成一個無形的安全閥,甚至國際上也會形成互不攻擊對方網絡的慣例協議或公約,網絡空間由此成為可以產生巨大威懾效應的戰略領域。網絡空間威懾繼核威懾之後,開始進入大國政治家和軍事家的戰略視野。研究網絡空間威懾的特徵、類型和運用要點,成為網絡強國、網絡強軍的必須考量和必要行動。
隨著人類社會對網絡空間依賴程度的不斷加深,網絡空間成為人類生產生活的“第二類生存空間”和軍事對抗的“第五維作戰空間”。世界各國圍繞網絡空間的主導權、控制權、話語權展開了激烈的爭奪,網絡空間的競爭已達到與人類生存、國家命運和軍事鬥爭成敗休戚相關的程度。思考網絡空間威懾能力建設,具有重大現實和理論價值。
一、網絡空間威懾的優劣分析
網絡空間威懾,是指在網絡空間採取各種行動,展示癱瘓控制敵方網絡空間,並通過網絡空間跨域控制敵方實體空間的決心和實力,從而達到懾敵、止敵、阻敵、遏敵目的的一種戰略威懾形式。網絡空間與實體空間相比所具有的“虛實二相性”,網絡戰與傳統作戰樣式相比所具有的獨特性,決定了網絡空間威懾的優缺點都非常明顯。
(一)網絡空間威懾的優點
網絡空間威懾的優點,主要體現在:一是威懾方式更趨文明和人道。與基於物理、生物、化學殺傷機理的核生化武器相比,網絡戰武器的直接殺傷和破壞效應要遠小於前者,通常不會對自然環境造成永久性破壞和污染,也不會造成大量的人員傷亡,並引發人道主義災難。二是威懾成本低效費比高。網絡戰武器以病毒、木馬等軟件為主,成本相對低廉,技術門檻較低,而造成的破壞效果卻相當驚人。網絡防禦點多面廣,防不勝防,要網絡安全程度每提高一個等級,投入成本會呈指數級增加。網絡進攻的低成本與網絡防禦的高成本對比鮮明,使得網絡攻防呈現“矛尖盾薄”的特點,網絡戰武器因而被稱為“窮國的原子彈”。三是威懾手段多樣實用性強。網絡戰武器多種多樣,網絡攻擊目標多元,決定了有多樣化的網絡空間威懾手段可供選擇。網絡攻擊效果在一定程度上是可恢復的,只要運用實施得當,引發戰爭和促使戰爭升級的風險相對較小。從某種意義上講,核武器的威懾價值遠大於實戰價值,而網絡戰武器則是實戰價值與威懾價值兼具。四是威懾運用可重複靈活性強。 “核門檻”一旦跨過就會爆發全面核戰爭,處於核均勢的雙方將陷入相互摧毀狀態,輕易實施核威懾特別是對無核國家進行核威懾,還會招致國際輿論的譴責,這些因素都極大地限制了核威懾手段的使用。而網絡空間威懾軟硬結合、威力可控的特點,決定了其可根據軍事鬥爭形勢的變化和需要,適時調控威懾強度,先期使用、全程使用、反複使用,具有很強的靈活性。
(二)網絡空間威懾的不足
網絡空間威懾的不足,主要體現在:一是威懾效果的可信性未得到充分驗證。核威懾的可信度已在實戰中得到了驗證。然而,截止目前,真正意義上的網絡大戰還沒有真正爆發過。人們對網絡戰驚人的破壞力,更多的只是一種猜測和擔憂,網絡戰的真實威力只有經過實戰檢驗後,才能真正令人信服。二是威懾手段的可靠性不太高。網絡戰是敵我雙方網絡攻防持續互動的動態過程,網絡對抗複雜、技術性強的特點,決定了網絡戰攻擊效果具有較大的不確定性,有可能達不到預期作戰目的,使威懾效果大打折扣。例如,對敵實施網絡空間實戰威懾時,敵方若及時採取各種有效防御手段,就會增加己方網絡攻擊的難度和降低破壞效果,甚至導致攻擊行動的失敗。三是威懾範圍的可控性需進一步改善。病毒武器作為網絡戰的重要武器之一,其傳播性強、可控性較差、影響範圍比較廣,很難針對敵國計算機和網絡發動專門性、針對性極強的攻擊。如果不能控制其有效作用範圍,就會波及第三方中立國家,甚至使自身也成為受害者,因而病毒武器的使用有“投鼠忌器”之患。四是威懾對象的可選擇性受限。核威懾對任何國家都是明確而有效的,而網絡空間威懾的效果與敵國的信息化程度有很大關係。網絡空間威懾對信息化程度高的國家極為有效,而對那些信息基礎設施薄弱,網絡依賴性不強的不發達國家,則很難發揮效果,甚至完全不起作用。五是威懾實施的組織相對複雜。世界各個核國家無不對戰略核力量實施集中統管,指揮控制權高度集中,組織實施核威懾行動時可以準確控製到每一個作戰單元,組織實施十分周密。而網絡空間威懾的組織實施,要涉及偵、控、防、控等多支力量,人員多、規模大,且分散在軍地不同部門和單位,組織起來非常複雜,形成合力不易。
二、網絡空間威懾的主要類型
網絡空間威懾主要有網絡空間技術試驗威懾、網絡空間裝備展示威懾、網絡空間作戰演習威懾和網絡空間作戰行動威懾四種類型。其中,前三種是示形威懾,後一種是實戰威懾。
(一)網絡空間技術試驗威懾
網絡空間技術試驗威懾,是在網絡戰領域,經常性地進行新作戰概念的先期探索性試驗、新攻擊機理和戰術的效果印證性試驗、新技術的實用化武器化試驗等,並通過媒體向外界披露,以展現本國雄厚的信息技術基礎研究實力,以及轉化為網絡戰能力的巨大潛力,以達到威懾對手的目的。當前,網絡攻防技術仍在快速發展,一項關鍵性技術的突破,往往會對網絡空間安全和作戰產生重大影響,甚至引發革命性變化。誰搶先佔領了網絡攻防技術的戰略制高點,誰就能在未來網絡戰中取得明顯優勢。
(二)網絡空間裝備展示威懾
網絡空間裝備展示威懾,是在網絡戰裝備發展規劃制定、技術開發、打靶試驗、定型生產等各個發展階段,根據需要適當披露網絡戰裝備的型號、性能、特點、參數以及研製進度等情況,以達到威懾對手的目的。其方式主要有兩種:一種是通過在國防白皮書、外交公報以及報紙、期刊、大型網站等權威媒體從官方渠道公開披露,實施顯性威懾;另一種是通過網絡社交媒體或其他非官方渠道,刻意洩露裝備相關情況,實施隱性威懾。網絡空間裝備展示威懾,一方面可以虛構新機理、新概念的新型網絡戰裝備,並渲染其獨特的作戰能力;另一方面可以刻意誇大已有網絡戰裝備的作戰效能。虛中有實、實中有虛,實施模糊政策,使對方摸不清己方真實情況和實力,產生恐懼和忌憚心理。例如,美軍的“舒特”機載網電一體攻擊系統已多次投入實戰使用,對其敵對國家的防空體系構成了嚴重威脅,但其基本原理、工作機制、戰技指標既沒有公開披露,也沒有被他國完全掌握破解,一直處於保密狀態,令人虛實難辨,起到了很好的威懾作用。
(三)網絡空間作戰演習威懾
網絡空間作戰演習威懾,是以實兵或虛擬的方式在網絡空間展開演習活動,並藉助各種媒體渠道,向潛在作戰對手展現本國網絡戰能力、實力與決心,以達到威懾對手的目的。網絡空間作戰演習可分為實兵演習和虛擬演習兩種。前者通常在全國范圍內或與盟國聯合進行,一般以演練軍地聯合網絡空間防禦行動為主。近幾年來,美國及盟國多次舉行“網絡風暴”系列網絡戰演習,以及“施里弗”系列太空-網絡空間演習,很好展現了網絡戰的動員實力、整體防禦水平,以及實施網絡戰的決心。後者通常在國家大型網絡綜合靶場舉行,一般以演練軍隊專業網絡戰力量的進攻行動為主。
(四)網絡空間作戰行動威懾
網絡空間作戰行動威懾,是指對特定的網絡目標實施攻擊,以確信的攻擊效果來威懾作戰對手的一種實戰性威懾。其運用的時機有兩個:一是當己方覺察敵方即將對己方發動戰爭時,己方選擇敵方重點防禦的關鍵性網絡目標進行針對性打擊,進行預防性、遏制性威懾;二是當敵方通過對己方發起試探性網絡攻擊,實施網絡空間威懾時,己方應立即進行有效的報復性、懲戒性威懾。具有威懾效果的網絡戰行動有多種。例如,對敵電信網滲透破壞,向敵國民眾手機大量發送宣傳反戰短信;對敵電力網進行攻擊,造成敵重要城市短時間的大面積停電;對敵廣播電視網進行攻擊,在黃金時段插播己方特製的視頻節目;等等。
三、網絡空間威懾的運用要點
網絡空間威懾總的運用要求是:懾戰結合,以實力、實戰展示能力和決心,力求以小戰體現威懾、以精打確保威懾,以較小的代價實現威懾目的。具體說來,應做到以下幾點。
(一)平戰結合,長期準備
“冰凍三尺,非一日之寒”。成功實施網絡空間威懾,需要平戰結合,在平時就要進行充分細緻的準備。一是要進行全面周密的網絡偵察。要求諜報偵察與技術偵察、無線偵察與有線偵察相結合,對敵網絡目標進行長期持續的網絡偵察,逐步摸清敵網絡基本情況,繪製其網絡拓撲結構圖,尤其是分析查找出敵各種軟硬件系統的漏洞。二是要進行大量有效的戰略預置。採用黑客手段,通過利用系統漏洞或口令破譯等辦法,秘密滲透進入敵各類網絡,留下後門,設置跳板機,埋設邏輯炸彈和木馬,為未來發動網絡攻擊預留突破口。三是進行預有準備的網絡防禦。在對敵實施網絡空間威懾時,己方應提前調整網絡防禦部署,使敵預先設計的攻擊路徑,預期利用的系統漏洞,預定執行的攻擊方案難以實施,或實施效果大打折扣,最大限度地降低敵網絡報復造成的損失。
(二)慎重決策,控制強度
孫子曰:“主不可以怒而興師,將不可以慍而致戰”。網絡空間威懾是國家之間的戰略博弈行為,尤其是實戰威懾,敏感性強,必須做到有理、有利、有節,決不能因為威懾“門檻”較低而濫用亂用,否則其效果可能會適得其反。網絡空間實戰威懾對作戰強度控制的要求很高。一方面,若強度太小,敵國政府和民眾不會產生畏懼心理,起不到應有的威懾效果,對方還可能採取同樣的手段實施反威懾,最終導致對抗升級,使己方威懾失效。另一方面,若強度過大,給敵國造成巨大的經濟損失和人員傷亡,引起國際社會的譴責和敵國政府、民眾的仇恨心理,就可能引發敵國運用常規力量進行大規模報復,有核國家甚至可能會動用核力量,這樣不但不能懾止戰爭,反而會起到戰爭導火索的作用。
(三)統一指揮,周密組織
網絡空間威懾的組織實施,要集中指揮,統一籌劃,搞好協同。一是精心組織力量。統一組織軍隊偵、攻、防、控四支力量,積極協調軍地各方網絡戰力量形成合力。尤其是要組織和協調好民間非專業網絡戰力量特別是愛國黑客,不能出現“盲動”現象,以免引發磨擦,擦槍走火,引起網絡戰的升級,或過早暴露攻擊意圖,授人以柄,導致局勢不可控或行動失敗。二是精當選擇目標。應選擇影響面廣,易產生明顯威懾效果的目標。例如,收視率排名靠前的廣播電視頻道、訪問量巨大的門戶網站、用戶眾多的無線通信網絡等。不能選擇無關痛癢、影響面小、民眾漠不關心的目標進行攻擊,易被誤認為是普通黑客製造的網絡安全事件,起不到應有的威懾效果。此外,還要考慮國際法和戰爭法約束,不能選擇易造成人道主義災難的目標,盡量不選取鐵路、航空、金融、醫療等部門的網絡目標,以免激起國際社會和對方民眾的譴責和反感。三是精確控制進程。實施網絡空間威懾性打擊之前,要通過廣泛的輿論宣傳造勢,向敵國發出打擊警告,並向全世界宣告己方行動的正義性,以爭取國際輿論的理解和支持。為突出威懾效果,己方可以高調宣布要攻擊的敵國網絡目標,再突破敵方層層網絡防禦,實施堅決有效的網絡攻擊,必要時最後還可對網絡攻擊效果進行定時恢復,以展現己方高超的網絡攻擊技術和手段,讓敵方決策者和民眾產生防不勝防、難以招架的心理挫折感,從而形成強烈的震懾效果。
(四)虛實結合,注重謀略
孫子所說的“能而示之不能,用而示之不用”,運用到網絡空間威懾,其要點概括起來就是“示而不宣、宣而不示”。 “示而不宣”,就是利用網絡攻擊難以追踪定位這一點,對特定目標實施網絡攻擊,但不對外宣布是己方所為,既展示了己方能力,又使得敵方雖然懷疑是己方所為,但沒有證據,無法追究。 “宣而不示”,就是公開宣傳或不經意透露己方研製或虛構的先進網絡戰裝備的型號、性能、特點,刻意誇大其作戰效能,虛虛實實,虛實結合,使敵摸不清己方真實實力,從而產生威懾效果。網絡戰行動具有追踪溯源困難、取證複雜的特點,發起方既可以承認,也可以矢口否認,或把責任推給民間黑客組織。 (來源:中國信息安全)
Original URL: