Chinese Internet Security Report 2017 (a) //
中華人民共和國2017年上半年互聯網安全報告
1 Internet security situation is grim, to develop network security is imperative
At the same time, the Internet security has become more and more important. In 2014, the central network security and information leading group was formally established, Xi Jinping personally as head of the country and the government’s attention to the degree of network security is evident. In the central network security and information leading group at the first meeting, Xi Jinping first proposed “network power” strategy, “no network security is no national security”, network security is a relationship between national security and sovereignty, social stability, national culture The important issue of inheritance and development. Its importance, with the pace of global information to accelerate and become more and more significant. “Home is the door”, security issues without delay.
In China, the network has entered the tens of thousands of households, the number of Internet users in the world, China has become a network power. The Internet has been deeply involved in all aspects of people’s lives. According to a survey on the information of the public, students and white-collar groups of Internet usage has been close to 100%, more than Jiucheng college students and white-collar groups the most important information access channel for the Internet. Internet users on the Internet to conduct the main news, learning, real-time communication, social networking and all kinds of leisure and entertainment. In the era of universal networking, Internet users how to ensure network security? How does an enterprise network effectively defend against cyber attacks? These have become important issues that countries, governments and the security industry are facing and need to address as soon as possible.
From the domestic “dark cloud Ⅲ” virus, to sweeping the global “WannaCry” extortion virus, and then to “Petya” malignant devastating virus, all that the current network security situation is grim, corporate security vulnerable, vigorously develop the network Security is imperative.
2 to strengthen the network security construction, lack of talent need to improve the current situation
Although China has become a big country network, but there is distance from the network power. Trojans and botnets, mobile Internet malicious programs, denial of service attacks, security vulnerabilities, phishing, web tampering and other network security incidents have occurred, the basic network equipment, domain name systems, industrial Internet and other basic infrastructure and critical infrastructure is still facing Greater security risks, strengthen the network security construction is imminent.
At the same time, the shortage of network security personnel in China is in urgent need of improvement. As a network power, China in addition to research and development of computer equipment to enhance the speed of network transmission, but also should step up the cultivation of computer information security personnel, so that China from the network power into a network power, which is to enhance China’s information security important basis.
Network security has risen to the national strategy, the state is also vigorously invested to promote the construction of network security. But do a good job of network security is not an organization, a department of things, but the need for the participation of the whole society. From the city of Wuhan issued “on the support of national network security personnel and innovation base development policy measures” invested 4.5 billion construction funds, to June 1, 2017 formally implemented the “People’s Republic of China Network Security Law”, are for network security Healthy, steady development and make efforts. We also call for the social responsibility as a safe enterprise, institutions, individuals actively into the network security building, for the country, the national network security protection contribute a force.
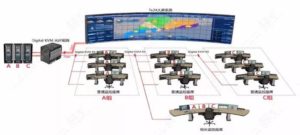
3 Tencent to promote the establishment of China’s first strongest Internet security matrix
Tencent security has 17 years of capacity accumulation and 800 million users of large data operating experience, is China’s leading Internet security products, security services provider. In the spirit of “open, joint, shared” concept, will accumulate years of ability and data sharing to partners, is committed to the Internet security and open platform construction, enhance the security of the Internet security industry chain, enhance user safety awareness, and jointly promote China’s Internet security Environmental construction.
At present, Tencent has promoted the establishment of China’s first Internet security matrix, covering the basic security of the laboratory matrix, security product matrix, security, large data platform matrix, and Internet security open platform matrix, committed to China’s Internet security new ecological construction, open core competencies And data for China’s Internet security and ecological construction unremitting efforts.

First, the overall status of network security scan
1.1 affect the world’s six major network security incidents, the cumulative impact of the world
1.1.1 WikiLeaks CIA top secret file leak event
March 7, 2017, WiKiLeaks announced thousands of documents and revealed the CIA on the hacker hacking technology, Mobile phones and smart TVs, but also can invade attacks on Windows, Mac and Linux operating systems, and even control smart cars to launch assassination activities. Outside the name of the leak event named Vault 7, Vault 7 published confidential documents recorded by the United States Central Intelligence Agency (CIA) conducted by the global hacker attacks.
Vault7 contains 8761 confidential documents and documents, which documents the CIA for Android and Apple smart phones developed by the intrusion crack technology details, some of which can also get the complete control of the target device. WikiLeaks founder A Sangqi said the document shows the “CIA network attack the overall ability”, and WikiLeaks in the release of these documents claimed that “CIA network armory has been out of control.”

1.1.2 Shadow Broker Public NSA (US National Security Agency) Hacker Arsenal
On April 14, 2017, Shadow Brokers published a large number of very destructive hacking tools used by the Equation Group in the NSA (National Security Agency) on steemit.com, including You can remotely break the global about 70% of the Windows machine vulnerability exploit tools. Anyone can use NSA’s hacker weapons to attack someone else’s computer. Among them, there are ten tools most likely to affect Windows personal users, including eternal blue, eternal king, eternal romance, eternal collaboration, emerald fiber, eccentric hamster, Eskimo volume, elegant scholar, eclipse wings and respect review. Hackers do not need any operation, as long as the network can invade the computer, like shock waves, Sasser and other famous worms can instantly blood wash the Internet.

1.1.3 “WannaCry” extortion virus broke out in the world on May 12th
May 12, 2017, “WannaCry” (want to cry) bitbell blackmail virus in the global outbreak, the event affected more than 150 countries and regions, more than 10 million organizations and institutions and more than 30 million Internet users, the total loss Up to more than 500 billion yuan. Including hospitals, educational institutions and government departments, without exception, suffered an attack. Blackmail virus worms in conjunction with the way the spread of the attack is a large-scale outbreak of the important reasons.
User’s most obvious symptoms after poisoning is the computer desktop background is modified, many files are encrypted lock, the virus pops up prompted the user to the relevant bit coin address transfer $ 300 in order to unlock the file. At present, security companies have found ways to restore encrypted files.

1.1.4 FireBall Fireball virus infected more than 250 million computers
June 1, 2017, foreign security agency Check Point reported that the outbreak of a “FireBall” virus abroad, and claimed that more than 250 million computers worldwide are infected, the most affected countries are India (10.1%) and Brazil (9.6%). The United States has 5.5 million computers in the move, accounting for 2.2%. In the infected business network, India and Brazil accounted for 43% and 38% respectively, compared with 10.7% in the US.
This malware will force the browser home page to its own website and search engine, and redirect the search results to Google or Yahoo. These forged search engines track user data and secretly collect user information. The author of this virus for the production of China’s Rafotech company, the company’s Web site has been unable to visit.

1.1.5 “dark cloud” series virus upgrade to “dark cloud III” again struck
June 9, 2017, Tencent computer housekeeper detected, as early as 2015 was first discovered and intercepted killing the “dark cloud” virus resurgence, upgrade to “dark cloud Ⅲ”, through the download station large-scale transmission, at the same time through Infected disk MBR boot boot, the number of infected users has reached millions.
After the upgrade of the “dark cloud Ⅲ” will be the main code stored in the cloud, real-time dynamic updates, and its function is currently downloaded to promote malicious Trojans, lock the browser home page, tampering to promote navigation page id. Once the user in the move, the computer will become a “broiler” to form a “botnet”, and the use of DDoS attacks built on a cloud service provider platform chess class site, resulting in the site access becomes abnormal card slow.

1.1.6 new round of extortion virus “Petya” struck, more destructive
June 27, 2017, a new round of extortion virus “Petya” attacked a number of countries in Europe, including Ukraine, Russia, India, Spain, France, Britain, Denmark and other countries have been attacked, the governments of these countries, Banks, enterprises, power systems, communications systems and airports are affected by different procedures.
This virus is more destructive than “WannaCry”, the virus on the computer’s hard disk MFT encryption, and modify the MBR, so that the operating system can not enter. According to the relevant analysis, said the information on the boot interface even if the information provided to the hackers is no way to decrypt, therefore, had to doubt the “Petya” the real purpose of the virus. “Petya” is more like a purposeful attack, the target can not repair the devastating attack, rather than extortion for the purpose.

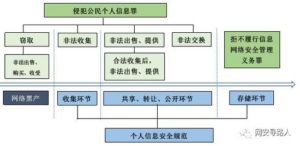
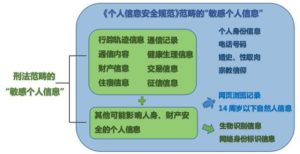
1.2 “People’s Republic of China Network Security Law” formally implemented
June 1, China’s first comprehensive standard of cyberspace security management of the basic law – “People’s Republic of China Network Security Law,” the formal implementation of a total of seven chapters seventy-nine, the content is very rich, with six outstanding highlights. One is clear the principle of cyberspace sovereignty; the second is clear the network products and service providers of security obligations; third is clear the network operator’s security obligations; four is to further improve the personal information protection rules; five is the establishment of the key Information infrastructure security protection system; six is to establish a key information infrastructure important data cross-border transmission rules.
At the same time the new law also pointed out that should take a variety of ways to train network security personnel, and promote network security personnel exchanges. The implementation of the new law marks the network security of China from the law, cyber space management, network information dissemination order norms, cybercrime punishment and so forth will open a new page, to protect China’s network security, safeguarding the overall security of the country has far-reaching and significant The meaning of.
1.3 The size of Internet users in China is equivalent to the total population of Europe, the safety gap of up to 95%
1.3.1 Chinese Internet users reached 731 million, equivalent to the total population of Europe
As of December 2016, the scale of Internet users in China reached 731 million, the penetration rate reached 53.2%, more than the global average of 3.1 percentage points, more than the Asian average of 7.6 percentage points. A total of 42.99 million new Internet users, the growth rate of 6.2%. The size of Chinese Internet users has been equivalent to the total population of Europe.
1.3.2 mobile users continue to grow, the proportion of mobile phone users accounted for 95.1%
As of December 2016, China’s mobile phone users reached 695 million scale, the growth rate of more than 10% for three consecutive years. Desktop computers, notebook computers are using the decline in the number of mobile phones continue to squeeze the use of other personal Internet devices.
1.3.3 security talent gap is huge, up to 95%
Although the number of Internet users in China has been ranked first in the world, but China’s information security industry in the very few people, security personnel and its lack. According to relevant information, in recent years, China’s education and training of information security professionals only 3 million people, and the total demand for network security personnel is more than 700,000 people, the gap up to 95%. 710 million Internet users in China network security issues, has become the industry and the country to solve the problem.
Beijing Institute of Electronic Science and Technology, vice president of the Ministry of Education of Higher Education Information Teaching Committee of the Secretary-General Fenghua pointed out that the current important information systems and information infrastructure in China need all kinds of network information security personnel will be 15,000 per year The rate of increase, by 2020 the relevant talent needs will grow to 1.4 million. But at present, only 126 colleges and universities in China have set up 143 network security related professionals, accounting for only 10% of the 1200 science and engineering institutions.
Analysis on the situation of network virus threat in the first half of 2017
2.1 Tencent security anti-virus laboratory PC-side virus interception over 1 billion, the chain by 30%
2.1.1 Trojan horse intercepts an average of nearly 170 million times per month
In the first half of 2017, Tencent security anti-virus laboratory statistics show that PC-side total has blocked the virus 1 billion times, the overall number of viruses compared to the second half of 2016 Tencent security anti-virus laboratory to intercept the number of viruses increased by 30% Interception Trojan virus nearly 170 million times. April, June to intercept the peak of the virus, interceptions are 180 million times.

2017 Q2 quarter compared to 2016 Q2 quarter, Tencent security anti-virus laboratory virus blocking an increase of 23.7%. From 2014 to 2017 Q2 season, the amount of virus blocking the number of malicious programs increased year by year.

2.1.2 PC users in Guangdong, the highest number of poisoning, poisoning peak for the morning 9-11 points
2.1.2.1 found a total of 230 million times in the first half of the user machine Trojan virus
The first half of 2017 Tencent security anti-virus laboratory found a total of 230 million times the user machine Trojan virus, compared to the second half of 2016 down 0.5%, an average of 38.8 million poisoning machines per month for virus killing. 2017 Q2 quarter compared to Q1 quarter, a slight increase in the number of poisoning machines.

In the second quarter of 2017, the number of users in the second quarter of 2016 increased by 3% compared with the same period in the second quarter of 2016. From 2015 to 2017 Q2 season, the number of poisoning machine growth trend is obvious, was increasing year by year state.

2.1.2.2 PC end user poisoning peak for the morning 9:00 to 11:00
According to statistics, the peak time of daily poisoning for the morning 10 am – 11 am, in line with business and ordinary users 9 am – 11 am to open the computer processing work of the law. This time the user poisoning virus type is more use of e-mail, sharing, etc. spread Office document macro virus, indicating that the office security situation is still grim.

2.1.2.3 PC end poisoning user provinces up to Guangdong, which ranks first in Shenzhen
According to Tencent security anti-virus laboratory to monitor the number of poisoning PC statistics, from the urban distribution point of view, the Internet is more developed city users poisoning situation is heavy, the country ranked the first city to intercept the virus in Shenzhen City, accounting for 3.76% , The second for the Chengdu City, accounting for 3.57% of all interceptions, the third for the Guangzhou City, accounting for 3.39% of all interceptions.

From the provincial geographical distribution, the largest number of PC poisoning in Guangdong Province, accounting for 13.29% of the total intercept, the second in Jiangsu Province, accounting for 7.75% of all interceptions, the third in Shandong Province, accounting for all Intercept the amount of 7.12%.

2.1.3 The largest virus category accounted for 53.8% of the Trojan virus, blackmail virus added 13.39%
2.1.3.1 PC-side of the first major virus is still Trojans, PE-infected virus type, but the spread of large
According to Tencent security anti-virus laboratory 2017 Q2 season to obtain the virus sample analysis, from the virus type, Trojans accounted for 53.80% of the total number, is still the first major virus. Adware class (adware, forced installation, user privacy, spam, etc.) for the second largest virus category, accounting for 39.02% of the total number. Backdoor category for the third largest virus category, accounting for 5.13% of the total number. Compared to the 2017 Q1 quarter, the virus type did not change much.

The number of virus samples from the top of the division, ranked first and second is still the Trojans and Adware class, but ranked third in the PE infection, accounting for 25.07% of the total number.

There are not many types of infectious samples, which is difficult to produce infectious virus, hackers and other programmers need to master the technology, high cost, long development time and other factors. At the same time, the transmission of infectious virus is very large, the survival time is relatively long, therefore, less species of PE infection type in the sample transmission level accounted for a certain proportion, which is due to infection with a wide range of viruses, Fast propagation characteristics.
2.1.3.2 extortion virus sample number Q2 added 13.39%, the first is not WannaCry
The extortion of the virus is the purpose of extortion money for the purpose of making the Trojan horse infected computer user system specified data files are malicious encryption, resulting in user data loss. At present, most of the domestic extortion of the virus by the need to pay the rupiah to be able to decrypt. As the bit currency completely anonymous circulation, the current technical means can not track behind the extortion behind the virus operator, which also makes the extortion virus from 2013 after the explosive growth.
The amount of extortion
According to Tencent security anti-virus laboratory to detect the extortion virus, 2017 in the first half of the total has been found in the number of extortion virus samples in about 300 million, the average monthly detection of the number of extortion virus nearly 500,000, Q2 quarterly extortion virus samples The number increased by 13.39% over Q1 quarter. May, June to intercept the peak of the virus, respectively, 57 million, 530,000.

Extortion virus type
According to the relevant data analysis shows that the May 12 outbreak of the WannaCry extortion virus is the most active in this quarter, the greatest impact on the virus. The virus and other viruses in the way of transmission is significantly different, due to the use of the windows system vulnerabilities, making the virus can spread around the world, as the quarter of the hot safety events. On June 27, a new type of extortion virus called Petya began spreading around the world, and its extortion was similar to WannaCry, but more destructive, directly encrypting the MFT of the user’s hard drive and modifying the MBR, causing the user to fail to windows system.
Although the impact of the virus is large, but from the sample size point of view, the largest or with the spread of infection PolyRansom virus. This virus will be infected, encrypted users of the file to extortion, but because there is no use like WannaCry virus key encryption, but the use of a simple encryption algorithm, and the algorithm is reversible, anti-virus software can help users to restore files, So although the number of samples in the first, but the impact is not great. This type of extortion virus accounted for 78.84% of all extortion virus, we can see the spread of infectious virus strong.

From the sample size point of view, in addition to infectious extortion virus, the first is Blocker, accounting for 36.82% of all extortion virus, the second category is Zerber, accounting for 23.63% of all extortion virus, the third category Is the most affected this quarter, WannaCry extortion virus, accounting for all extortion virus 12.06%. WannaCry virus volume quickly rose to the third position, because the means of communication using the spread of vulnerability.

The current extortion virus mainly uses the following kinds of transmission:

Document infection spread
File infection is the use of infectious virus transmission characteristics, such as PolyRansom virus is the use of infectious virus characteristics, encrypted users all the documents and then pop-up information. Because the PE class file is infected with the ability to infect other files, so if the file is carried by the user (U disk, network upload, etc.) to run on other computers, it will make the computer’s files are all infected with encryption.
Site hanging horse spread
Web site is through the site or the site server to obtain some or all of the authority, in the web page file to insert a malicious code, these malicious code, including IE and other browser vulnerabilities use code. When a user accesses a linked page, a malicious code is executed if the system does not update the exploit patch used in the malicious code.
The virus can also use known software vulnerabilities to attack, such as the use of Flash, PDF software vulnerabilities, to the site with malicious code to add the file, the user with a loopholes in the software to open the file will be executed after the malicious code, download virus.
Using system vulnerabilities
May outbreak of WannaCry is the use of Windows system vulnerabilities to spread, the use of system vulnerabilities is characterized by passive poisoning, that is, users do not have to visit a malicious site, not open the unknown file will be poisoned. This virus will scan with the network vulnerabilities in other PC host, as long as the host is not marked with a patch, it will be attacked.
Tencent anti-virus laboratory to remind you, timely updates third-party software patches, timely update the operating system patches to prevent known vulnerabilities attack.
Mail attachment spread
The extortion virus that spreads through e-mail attachments usually disguises documents that users need to view, such as credit card spending lists, product orders, and so on. The attachment will hide the malicious code, when the user opens the malicious code will begin to perform, release the virus. This type of camouflage virus is usually sent to enterprises, universities, hospitals and other units, these units in the computer usually save the more important documents, once malicious encryption, the possibility of payment of ransom far more than ordinary individual users.
Network share file spread
Some small-scale spread of extortion virus will be spread through the way the file spread, the virus will upload the virus to the network sharing space, cloud disk, QQ group, BBS forums and other places to share the way to send a specific crowd to trick the download and install The
Tencent anti-virus laboratory to remind users to download the software go to the official formal channel download and install, do not download the unknown program, such as the need to use the unknown source of the program can be installed in advance Tencent computer housekeeper for security scanning.
2.2 mobile side killing a total of 693 million Android virus, mobile phone users over 100 million
2.2.1 mobile side of the virus package growth trend slowed down, but the total is still 899 million
In the first half of 2017, Tencent mobile phone housekeeper intercepted Android new virus package totaled 8990000, compared with 2016 in the first half of a small decline, but the total is still very large.

2.2.2 Guangdong mobile users poisoning the most, the number of mobile phone users decreased by 45.67%
2.2.2.1 Tencent mobile phone housekeeper in the first half were killing Android virus 693 million times
In the case of a large number of virus infection users in the case, the first half of 2017 Tencent mobile phone housekeeper killing the virus has reached 693 million times, an increase of 124.24%, the total number of more than double the first half of 2016 more than doubled. Malicious programs and Trojans to reduce the cost of production, virus transmission channel diversification is an important factor in this phenomenon.

In addition to June, the first half of 2017 killing more than 100 million times a month, of which the number of mosquitoes in January up to 136 million times, almost the first half of 2014, 140 million in the killing of the same level.

2.2.2.2 2017 in the first half of the number of mobile phone users over 100 million
In the first half of 2017, the number of virus infected users was 109 million, down 45.67% year on year, compared with 2015, the first half of 2016 compared to all declined.

January 2017 single month infected users reached 21.66 million, the highest for the first half, then the number of infected users began to slow down.

2.2.2.3 the number of mobile users poisoning Guangdong ranks first
In the infected mobile phone users geographical distribution, Guangdong ranked first, accounting for up to 11.41%.

2.2.3 hooliganism and resources accounted for more than 80%, two-dimensional code is most easy to poison
2.2.3.1 mobile-side virus in the hooliganism and tariff consumption accounted for more than 80%
In the first half of 2017, the proportion of mobile phone viruses, rogue behavior and tariff consumption accounted for the highest, to 44.59% and 44.44% ratio of one or two. Ranked third of the same access to privacy accounted for 5.85%, lodging fraud, malicious deductions, remote control, system damage and malicious spread accounted for 1.94%, 1.55%, 0.80%, 0.74% and 0.08%.

Hooliganism refers to the malicious behavior of a virus that has a rogue attribute. Such as the recent WannaCry virus and once again concerned about the mobile phone lock screen Serbia virus with rogue behavior. This type of virus through the forum paste it and other means to spread, the drug will usually use plug-in, free, brush drill, red envelopes and other words on the Trojan virus packaging, induction users download and install. After the installation of the virus will be forced to lock the phone screen, forcing the victim had to contact the drug maker in order to make the equipment back to normal.

Whether the computer or mobile phone, with rogue behavior of the extortion virus to the user losses are difficult to estimate, if accidentally poisoning, not only will cause property damage, will also lead to loss of important information, so users should be careful to guard.
Tariff is also a common type of mobile phone virus, such a virus usually in the user without the knowledge or unauthorized circumstances, by sending text messages, frequent connections to the network, etc., resulting in user tariff losses. Part of the malicious promotion of the virus to help third-party advertisers to increase traffic for the purpose of the user to download and install the virus, access to mobile portal privileges, the implementation of the download malicious advertising software. These software will continue to push a variety of pop advertising, affecting the user’s mobile phone experience, and even those who will disclose user privacy information, stolen online banking accounts, resulting in serious personal and property safety.

Infected with the world’s ultra-36 million Andrews device malicious ad click software “Judy” is a tariff consumption of mobile phone viruses. The malware is hidden in a Korean tour. After completing the download and install, the infected device will send the information to the target page and automatically download the malicious code in the background and access the advertising link, theft of user traffic, to the user Consumption.
2.2.3.2 two-dimensional code, software bundles are the main source of mobile virus source
Mobile virus channel sources are mainly seven categories, namely, two-dimensional code, software bundles, electronic market, network disk communication, mobile phone resource station, ROM built-in and mobile forum. The diversification and diversification of the entrance of the virus channel also further increases the risk and risk of the user’s exposure.

In the first half of 2017, two-dimensional code became the source of mainstream virus channels, accounting for up to 20.80%. Two-dimensional code in the various areas of the popularity of more and more users to develop a habit of sweeping the random, the drug maker also increased for the two-dimensional code channel virus package delivery ratio. Part of the virus is embedded in the two-dimensional code, as long as swept away will automatically download the malicious virus, ranging from mobile phone poisoning, while the personal privacy information is caused by leakage, resulting in property losses.
Third, anti-harassment fraud effect is remarkable, but the user loss situation is grim
3.1 the first half of the number of spam messages over 566 million, illegal loans over 50%
3.1.1 In the first half of 2017, the total number of spam messages continued to grow close to 600 million
Low spread costs and the existence of a huge chain of interests, resulting in spam messages have been difficult to be effectively remediation, the number of users is also increasing the number of reports. In the first half of 2017, Tencent mobile phone housekeeper received a total of 586 million copies of spam messages reported by users, an increase of 40.69%, more than 2 times in the first half of 2014.

3.1.2 users to report spam messages up to the provinces of Guangdong, the largest city for Shenzhen
In the geographical distribution of spam messages, the top three provinces that reported spam messages were Guangdong, Jiangsu and Shandong, accounting for 12.91%, 6.98% and 5.70% respectively. In addition, Henan, Zhejiang, Sichuan, Hebei, Beijing, Hunan and Shanghai also ranked the top ten. These provinces or municipalities are generally distributed in the eastern coastal and central regions, and densely populated and economically developed are their greatest common ground, which creates favorable conditions for fraudulent bulk spam messages and profiteering.

City, the first half of 2017 users in Shenzhen reported a total of 23.34 million spam messages (accounting for 3.98%), Chengdu, Guangzhou and Suzhou, two to four, the number of spam messages are 10 million level.

3.1.3 2017 first half of the common types of fraud SMS
Although the overall amount of fraud SMS reported a downward trend, but its means of diversification and secrecy makes the dangers of fraud has always been high. According to Tencent mobile phone housekeeper to monitor the 28.57 million fraud messages show that illegal loans, online shopping, viral Web site, malicious Web site and pseudo-base station is the highest proportion of several fraudulent SMS type.
One of the illegal loan fraud messages a dominant, accounting for more than 50%. In the modern “room full of things” and rely on home buyers to seek a sense of security in the context of the community, the loan to buy a house has become a major social needs. Liar also keep up with this social pain points, a large number of illegal loans to send text messages, to profit.

3.2 harassing telephone users labeled up to 235 million times, down 27.12%
3.2.1 2017 users in the first half of the total number of harassment calls 235 million times down 27.12%
After the first half of 2015, after the explosive growth in the first half of 2015, the number of harassing telephone marks began to decline year by year in the first half of 2016, and the total number of harassing telephone marks in the first half of 2017 was 235 million, down from the first half of 2016 %.

3.2.2 In the first half of 2017, more than 50% of harassing calls were sounded
User-tagged harassing phone types are divided into five categories. Among them, the sound ranked first, accounting for more than 50%. This kind of harassing phone will not cause serious harm to the user, but will still affect the use of mobile phones, interference users. Phishing calls accounted for 15.14%, ranked second, in addition to advertising sales, real estate intermediary and insurance management also occupy a certain percentage.

3.2.3 harassing telephone calls for the highest proportion of verification code
According to Tencent mobile phone housekeeper users take the initiative to report the harassment of telephone malicious clues show that asking for verification code, fake leadership, transfer, online shopping and offense is the most common keywords. Which requires the highest proportion of verification code, nearly 24.74% of the harassing phone, the liar will be through various means to ask for verification code, and verification code as an important private information, once leaked, it is easy to cause property damage.

3.2.4 fraud telephone mark down 59.68% year on year, Beijing up
In the user has been marked 235 million harassing phone, scams like telephone ratio is far less than loud, but its substantial harm caused by the largest. Based on Tencent mobile phone housekeeper user fraud phone tag data show that in the first half of 2017 defraud telephone mark down 59.68%, a total of 35.59 million.

These frauds are targeted at the target area is more clear to the eastern coastal economically developed areas and inland central provinces. On the urban side, Beijing is the largest number of cities with the largest number of fraudulent calls, up to 1.826 million. Shenzhen and Guangzhou, respectively, to 141.8 million and 1.257 million mark the number followed. Shanghai, Xi’an, Changsha, Chengdu, Hangzhou, Chongqing and Wuhan are ranked fourth to ten.

3.3 malicious Web site to intercept up to 47.8 billion, pornographic fraud head of the site
3.3.1 The number of malicious web sites detected in the first half of 2017 exceeded 1.83 billion
In the first half of 2017, Tencent security in the PC and mobile side detected a total of more than 183 million malicious web site, the overall trend of rising volatility. Which in June detected 35.75 million malicious Web site, the highest for the first half, the lowest in April, the number of 25.53 million detection.

3.3.2 Pornography The website is still the main means of committing malicious web sites
In the effective detection of malicious Web site at the same time, the first half of 2017 Tencent security in the PC and mobile side to intercept malicious sites up to 47.8 billion times, equivalent to 265 million times a day intercept. This huge data also further illustrates the grim situation of Internet security.

In Tencent’s securely intercepted malicious Web site, pornographic websites, gambling sites, information scams, malicious files, fake ads and phishing scams are the most widely distributed six categories of malicious Web sites. Which accounted for half of the site of pornography, accounting for 51.98%, pornographic fraud sites will be embedded fraudulent advertising or trick users to pay online. Malicious Web site will also be embedded in the fraud message to spread, to increase the confusion, so users see the text in the URL, should consciously raise vigilance, remember not to click.

3.4 iOS harassment and fraud phone calls fell by about 35%, calendar ads into new harassment
3.4.1 iOS harassment calls and phishing calls appear more substantial decline
In September 2016, Tencent mobile phone housekeeper and Apple introduced a new version of iOS10, the first increase in interception harassment and fraud phone features, effectively alleviate the troubled iPhone users troubled phone problems. Data show that the first half of 2017 iOS users were marked a total of 14.492 million harassing telephone, fraud, telephone 2.196 million times.
From the overall trend point of view, the first half of the iOS harassment phone signs showed a downward trend in the number of signs in January the highest number of 3.195 million times, only 2.0 million in April, the first half of the lowest peak. In contrast, the overall trend of fraudulent phone is more stable. From the above data can be seen, the first half of 2017 harassing telephone and phishing calls have emerged a more substantial decline, which is inseparable from the relevant departments, mobile operators and mobile phone users to work together.

3-4 calendar ads into the third largest harassment of Apple phones
Spam, harassing the phone, calendar advertising has become the main source of iPhone users harassment. Among them, the calendar advertising harassment problem is increasingly serious. 61.1% of users have experienced calendar ads, including gambling ads, real estate advertising, taxi software advertising top three.

3.5 Tencent Kirin system to combat pseudo-base station protection 150 million people
3.5.1 Tencent Kirin system to intercept 230 million fraud messages to protect 150 million people
In the first half of 2017, Tencent Kirin pseudo-base station real-time positioning system for the national users to intercept 230 million pseudo-base station fraud messages, the total impact of the number of 150 million people.
3.5.2 pseudo-base station regional characteristics: Sichuan, Shaanxi, Hubei, Hubei and Hubei provinces up
From the geographical point of view, Tencent Kirin for Sichuan, Shaanxi, Beijing, Hubei, Hunan users to intercept the largest number of fraudulent SMS, the five provincial administrative departments to intercept the number of fraud messages more than 50% of the total.

From the city point of view, the number of intercepting the number of fraud messages Top 10 cities such as Beijing, Chengdu, Xi’an, etc. are almost capital cities or economically developed cities, due to densely populated, urban residents income is higher, by pseudo-base station fraud gang included in the key attack Object.

3.5.3 pseudo-base station crime time characteristics: the most frequent working hours
From the time of committing the crime point of view, pseudo-base station fraud messages sent between 9 am to 19 pm, which in 10 am to 12 pm, 15 pm to 18 pm for the two peaks. It is easy to see that the peak of fraudulent SMS coincides with the daily working hours.

3.5.4 Content characteristics: Industrial and Commercial Bank of China, China Mobile most “lying gun”
Pseudo-base station SMS type, the points exchange, account abnormalities and bank credit card mention category accounted for close to 90%. These three categories often associated with operators, banks, often points to clear, credit card to mention the amount, account real name, abnormal and other reasons to fraud.

Tencent Kirin intercepted pseudo-base station counterfeit port, counterfeit industrial and commercial bank fraud SMS up to (up to 52%), Top 5 counterfeit port in addition to middle peasants construction of four major banks, as well as operators China Mobile. It is not difficult to see that these “lying gun” business because the user community is huge, business mode, short message is particularly important, so become a pseudo-base station fraud group to simulate the main object to send.

Fake base station SMS reach the user’s operator distribution, China Mobile accounted for 74%, followed by China Telecom (16%), China Unicom (10%).

Fourth, the first half of 2017 safety personnel development progress and results
4.1 “Network Security Law” to promote the comprehensive training of talent
June 1, 2017 from the implementation of the “Internet Security Law” for the first time in the form of legal provisions of the network space security field of personnel requirements, not only reflects the country’s attention to the network of talent, but also for the State Council and the local network The rules of safety personnel training provide the highest level of legal basis.
“Network Security Law” provides that: state support enterprises and institutions of higher learning, vocational schools and other education and training institutions to carry out network security-related education and training, to take a variety of ways to train network security personnel, and promote network security personnel exchanges. Network security personnel not only include technical talent, but also management talent. The current network security is not only the technical contest, it is the idea, the rules of the contest, familiar with international rules, power relations network security personnel in the future of cyberspace competition can play a greater role. Therefore, the training of network security personnel not only to cultivate traditional talents, but also based on the domestic, look at the world, cultivate a comprehensive understanding of network diplomacy talent.
At the same time, the provisions of the provisions of the “network of security personnel exchanges”, reflects the training mechanism for China’s open innovation and innovative ideas. Talent training is inseparable from the advanced countries of academic research and technical exchanges, the business organizations should attract foreign high-end technical personnel, while speeding up the training of our top talent.
4.2 security personnel training “Tencent mode”: to create talent closed-loop
As an advocate of Internet security open platform, Tencent has been “network security” as an important part of the enterprise design and strategic project. In the process of continuous attention and support of safe personnel selection and training, Tencent has gradually recruited a set of safety personnel selection system in the aspects of campus recruitment, social recruitment, promotion of internal talents, salary and welfare, etc .; at the same time, Security events and promote personnel training program, Tencent has gradually formed a mature, perfect, and for social reference to the safety of personnel training system.
Tencent in 2017, the parties launched the Tencent Information Security Competition (TCTF), through the internationalization of the system to explore talent, through high-quality counseling mechanism and professional mentor team training personnel and through the construction of enterprises and universities bridge transport personnel. At the same time, Tencent through the creation of “Hundred Talents Program” to build the Internet security personnel training closed-loop, through the TCTF contest layers of competition examinations, selected the most potential of 100 security personnel, and through continuous follow-up training to build the Internet security complex, Leading talent.
Tencent hopes to TCTF as a professional security personnel training platform between enterprises and universities to build a bridge between the formation of selection, training, transportation in one of the closed-loop talent for the Chinese new forces to provide a multi-dimensional growth environment, and further promote the development of China’s network security The
4.3 Tencent security joint laboratory set up the first anniversary: escort six key areas of the Internet
July 2016, Tencent security integration of its laboratory resources, the establishment of the first domestic Internet laboratory matrix – Tencent security joint laboratory, which covers Cohen Laboratory, basaltic laboratory, Zhan Lu laboratory, cloud tripod laboratory, Anti-virus laboratory, anti-fraud laboratory, mobile security laboratory, including seven laboratories. Laboratory focus on security technology research and security attack and defense system structures, security and security coverage covers the connection, systems, applications, information, equipment and cloud, touch the six key areas of the Internet.
2016, Tencent security joint laboratory for Google, Microsoft, Apple, adobe and other international manufacturers to dig a total of 269 loopholes, ranking first in the country. In addition, by virtue of “the world’s first long-range non-physical contact with the invasion of Tesla car” research results, Tencent security joint laboratory Cohen laboratory selected “Tesla security researcher Hall of Fame”, and Tesla CEO Maske’s personal thanks The
In the field of anti-fraud in the country concerned, the anti-fraud laboratory in Tencent Security Joint Laboratory has formed a set of new standards for anti-fraud evaluation based on AI innovation + ability and openness in the field of anti-fraud research. Stop mode. In the AI innovation and the ability to open the two-wheel drive, the laboratory has launched Hawkeye anti-telephone fraud system, Kirin pseudo-base station real-time positioning system, God anti-phishing system, God investigation funds flow control system, God sheep intelligence analysis platform Five systems, and through the Tencent cloud SaaS services open to the need for government units, enterprises, etc., to help users prevent Internet fraud.
Five, safe hot event inventory
5.1 outbreak of Serbian virus and virus outbreak
5.1.1 WannaCry extortion virus broke out globally on 12 May
Event Background:
On May 12th, WannaCry (wanna cry) bitbell blackmail virus broke out on a global scale. According to Tencent security anti-virus laboratory security researchers found that the extortion event compared with the past, the biggest difference is that the extortion virus combined with the way worms to spread. Due to the leak in the NSA file, WannaCry spread vulnerability code is called “EternalBlue”, so some reports that the attack is “eternal blue”.
Virus Detailed Explanation:
The outbreak of blackmail virus in the past two years is largely related to the increasing perfection of encryption algorithms. The continuous updating of cryptography and algorithms ensures the security of data transmission and preservation in our daily network. Unfortunately, the author of the extortion virus also used this feature, so that although we know the Trojan algorithm, but do not know the author to use the key, there is no way to restore the file is maliciously encrypted.
Encryption algorithms are usually divided into symmetric encryption algorithm and asymmetric encryption algorithm two categories. These two types of algorithms are used in the blackmail virus.
The encryption and decryption of the symmetric encryption algorithm uses exactly the same key, which is characterized by a faster operation, but when using such an algorithm alone, the key must be exchanged with the server using a method that is recorded in the process And the risk of leakage. The symmetric encryption algorithms commonly used for blackmail viruses include AES and RC4.
Asymmetric encryption algorithm is also known as public key encryption algorithm, which can use the public key to encrypt the information, and only the owner of the private key can be decrypted, so as long as the public key and save the private key, you can guarantee The encrypted data is not cracked. The asymmetric encryption algorithm is usually slower than symmetric encryption. The asymmetric encryption algorithms commonly used by blackmail viruses include RSA algorithms and ECC algorithms.
Usually, the blackmail virus will combine these two categories of encryption algorithms, both can quickly complete the entire computer a large number of documents encryption, but also to ensure that the author’s private key is not leaked.
5.1.2 new round of extortion virus “Petya” struck, more destructive
Event Background:
June 27 A new round of extortion virus Petya attacked several European countries. This virus is more damaging than WannaCry. The virus encrypts the computer’s hard disk MFT and modifies the MBR so that the operating system can not enter. Compared to the previous, Petya more like a purpose of the attack, rather than a simple extortion. Tencent Hubble analysis system has been able to identify the virus and determine the high risk, the use of Tencent computer housekeeper can kill the virus.
Virus Detailed Explanation:
Petya Serbia virus virus poisoning will scan the network after the machine, through the eternal blue loopholes since the spread, to achieve the purpose of rapid propagation. Foreign security researchers believe that Petya extortion virus variants will be spread through the mailbox attachment, using the vulnerability to carry the DOC document to attack. After poisoning, the virus will modify the system MBR boot sector, when the computer restart, the virus code in the Windows operating system before taking over the computer, the implementation of encryption and other malicious operations. After the computer restarts, it will display a disguised interface, this interface is actually a virus display, the interface is suspected of being a disk scan, in fact, the disk data encryption operation.
5.1.3 Laurent virus Tencent security response program
For the outbreak of extortion virus, Tencent security emergency response program, for the advance prevention, in the virus cleanup and after the file recovery three cases, to the majority of users to deal with recommendations:
Pre-prevention
1. Use the computer housekeeper’s extortion virus immune tools, automated installation system patches and port shielding, or manually download and install.
2. Back up the data, install the security software, turn on the protection.
a) the relevant important documents using offline backup (that is, the use of U disk, etc.), such as backup;
b) the use of some computers with the system restore function, without attack before setting the system restore point, after the attack can restore the system, defense file encryption;
c) install Tencent computer housekeeper, open real-time protection, to avoid attack;
d) the use of computer housekeeper’s document guardian of the file backup, protection.
3. To establish an inactivated domain name for immunization.
According to the existing sample analysis, there is a trigger mechanism for extortion software, if you can successfully access the specified link, the computer will be in the extortion of the virus directly after the exit, it will not file encryption.
a) Ordinary users can be connected to the site, to ensure access to the site, you can avoid the attack to avoid being encrypted (only known to extortion virus);
b) enterprise users can build Web Server through the intranet, and then through the way DNS DNS domain name resolution to Web Server IP way to achieve immunity; through the domain name of the visit can also monitor the situation of intranet virus infection.
Things in the virus clean up
1. Unplug the cable and other ways to isolate the computer has been attacked to avoid infection with other machines.
2. Use the computer steward’s antivirus function to directly check out the blackmail software, scan clean up directly (isolated machines can be downloaded through the U disk, etc. to install the offline package).
3. Back up the relevant data directly after the system reload.
After the file is restored
1. Blackmail software with the ability to restore part of the encrypted file, you can directly through the extrapolated software to restore part of the file; or directly click on the blackmail interface, “Decrypt” pop-up recovery window to restore the list of files.
2. You can use third-party data recovery tool to try data recovery, cloud users can contact Tencent security cloud tripod laboratory to help deal with.
5.2 DDOS attacks continue, dark clouds variants frequently struck
Event Background:
June 9, a 2017 years since the largest DDoS network attack activities swept the country, Tencent security cloud tripod laboratory released traceability analysis report, through the attack source machine analysis, engineers found in the machine dark cloud Ⅲ variants. Through the flow, memory DUMP data and other content analysis, Tencent cloud tripod laboratory to determine the large-scale DDoS attacks by the “dark cloud” hacker gang initiated. After the upgrade, “Dark Cloud III” will be the main code stored in the cloud, real-time dynamic updates.
Virus Detailed Explanation:
“Dark cloud” series Trojan from the beginning of 2015 by Tencent anti-virus laboratory for the first time to capture and killing, has been more than two years. In the past two years, the Trojan constantly updated iteration, continue to fight against the upgrade.
From the beginning of April this year, the Trojans comeback again, the outbreak of the outbreak of the dark horse than the previous version of the more obvious promotion features, so we named it dark clouds Ⅲ. Dark clouds Ⅲ compared with the previous version has the following characteristics and differences:
First, more subtle, dark cloud Ⅲ is still no file without a registry, compared with the dark cloud II, cancel the number of kernel hooks, cancel the object hijacking, become more hidden, even professionals, it is difficult to find traces The
Second, the compatibility, because the Trojan mainly through the hook disk drive StartIO to achieve the protection and protection of the virus MBR, such a hook is located in the bottom of the kernel, different types of brand hard drive need hook point is not the same, this version of the Trojan increased More judgment code, able to infect the vast majority of the market and hard disk.
Third, targeted against security software, security vendors, “first aid kit” type of tool to do a special confrontation, through the device name of the way to try to prevent the pit of some tools to load the run.
5.3 in the first half of the focus of fraud cases inventory
5.3.1 Xu Yuyu telegraphic case
August 2016, just by the Nanjing University of Posts and Telecommunications Xu Yuyu, received a fraudulent phone, the other scholarship in the name of cheating Xu Yuyu University of the cost of 9900 yuan. After the report of Xu Yuyu emotional abnormalities, leading to sudden cardiac death, unfortunately died, triggering social concern about the unprecedented fraud. The case was publicly declared on July 19, 2017, the principal Chen Wenhui was sentenced to life imprisonment, confiscation of all personal property. The other six defendants were sentenced to 15 to 3 years imprisonment and fined. This verdict, to the community to pass the court in accordance with the law severely punished the telecommunications network fraud crime clear attitude.
Proposed: Xu Yuyu tragedy enough to cause public vigilance. Internet era, each person’s information flow are online through different channels of circulation, to the lawless elements can take advantage of the machine. Faced with such an environment, we should be on the strange phone and SMS alert. Even if the other can speak personal accurate information, can not be trusted, any event needs to be verified by reliable channels to protect their own security.
5.3.2 Henan large telecommunications fraud: lied to sell college entrance examination answers cheat nearly 100 million students
June 2017, Henan HebiCity police cracked the big telecommunications fraud, arrested two suspects, seized more than 70 copies of bank cards. These suspects under the guise of selling college entrance examination questions answer the way, through the network of college entrance examination candidates to implement fraud. According to the police preliminary investigation, fraud victims accumulated more than 3,500 people, involving more than 3 million yuan.
Prevention recommendations: the annual admission of college entrance examination, college entrance examination fraud is a high period of time. Candidates and parents need to beware of all the so-called “internal indicators”, false check the site, false search results such as college entrance examination in the name of all kinds of fraud means, do not have luck, deceived.
5.3.3 Wuhan female teachers suffered a series of telecommunications fraud 7 months to cheat 2.53 million
Wuhan, a secondary school teacher Chen, master’s degree, 2017 May to the police alarm fraud. It is understood that in November 2016, Chen received a strange call, said its social security card was stolen brush, and directly to the phone to the “Hunan Provincial Public Security Department.” Answer the phone “police” said Ms. Chen involved a fraudulent money laundering case, as “washing charges”, Ms. Chen half a year to the other side of the transfer of 2.53 million, the debt owed more than 300 million. The case is still in the investigation.
Precautionary advice: people need to be alert to unfamiliar calls and text messages. When receiving a suspected fraud or SMS, pay attention to verify the identity of the other party, especially the other party to the designated account remittance, do not easily remittance, should be the first time to inform the family to discuss or consult the public security organs; The public security department can not provide a security account, but will not guide you transfer, set a password.
Six, security experts advice
In the computer use, set the security factor high password. Using a password that is not easily guessed by violent attacks is an effective way to improve your security. Violent attack is an attacker using an automated system to guess the password. Avoid using words that can be found in the dictionary, do not use pure digital passwords; use special characters and spaces, and use uppercase and lowercase letters. This password is harder to crack than use your mother’s name or birthday as a password. In addition, the password length for each additional one, the combination of the composition of the password characters will increase in multiple, so the long password will be more secure.
Regularly upgrade the software, update the security patch. In many cases, it is important to patch the system before installing and deploying the production application software. The final security patch must be installed on the PC’s system. If not for a long time without a security upgrade, may lead to the computer is very easy to become an unethical hacker attack target. Therefore, do not install the software on a computer that does not have a security patch update for a long time.
Protect your data by backing up important documents. Back up your data, which is one of the important ways you can protect yourself from minimizing the loss in the face of a disaster. If the amount of data is huge, the data can be saved to the hard disk. But more convenient way, you can use Tencent computer steward class of security software, at any time to automatically restore the data to the local, you can also store to the cloud, maximize the data to ensure security.
Do not easily trust the external network, open network risk is huge. In an open wireless network, such as in a wireless network with a coffee shop, the network risk will multiply, this concept is very important. This does not mean that in some untrusted external network can not use the wireless network, but to always keep the security and caution of security. The key is that the user must be through their own systems to ensure safety, do not believe that the external network and its own private network as safe.
Improve the unfamiliar telephone, SMS alertness, do not believe in which the content. Fraudulent forms of SMS diversification, a variety of new SMS Trojans flooding through the temptation of the SMS comes with the virus link to pay the class, privacy stealth virus rapid growth. For the “college entrance examination”, “school notice”, “test report card”, “household registration management”, “mobile phone real name system”, “video video” and “traffic violation” and other text messages embedded in the URL link should be vigilant, Do not click anywhere. For unfamiliar calls, SMS should be vigilant and wary, do not believe what the other side of the content, if necessary, to verify their identity information.
Protect personal privacy information, do not easily disclose personal information to others. Personal account, password, ID card information and other key personal privacy information, it is absolutely free to any unfamiliar SMS, the phone revealed. Receive a strange message, the phone asked personal privacy, be sure to be vigilant. When publishing a message on a social platform, beware of important privacy information in the form of photos, screenshots, etc. Do not arbitrarily discard tickets, tickets or courier documents containing personal information to prevent personal information from being stolen.
Mobile phone users should develop good habits to use security software to protect the safety of mobile phones. Mobile phone users can download and install such as Tencent mobile phone housekeeper a class of mobile phone security software, regular mobile phone physical examination and virus killing, and timely update the virus database. For the latest popular and difficult to remove the virus or vulnerability, you can download the killing tool in time to kill or repair. At the same time open Tencent mobile phone housekeeper harassment intercept function, which can effectively intercept fraud phone, SMS, enhance mobile phone security.
Original Mandarin Chinese:
1 互联网安全形势严峻,大力发展网络安全防护势在必行
在互联网高速发展,已经成为社会发展动力的同时,互联网安全也变得越来越重要。2014年,中央网络安全与信息化领导小组正式成立,习近平亲自担任组长,国家和政府对网络安全的重视程度可见一斑。在中央网络安全和信息化领导小组第一次会议上,习近平首次提出“网络强国”战略,“没有网络安全就没有国家安全”,网络安全是一个关系国家安全和主权、社会的稳定、民族文化的继承和发扬的重要问题。其重要性,正随着全球信息化步伐的加快而变到越来越显著。“家门就是国门”,安全问题刻不容缓。
在中国,网络已走入千家万户,网民数量世界第一,我国已成为网络大国。互联网已经深度介入民众生活的方方面面。根据一份关于民众信息的调查报告显示,大学生和白领群体的互联网使用率已经接近100%,九成以上大学生和白领群体最主要的信息获取渠道为互联网。网民在互联网上进行的行为主要有获取新闻资讯、学习工作、即时沟通、网络社交及各类休闲娱乐。在全民联网的时代,网民的网络安全如何保证?企业网络在面对网络攻击时如何进行有效的防御?这些都已经成为国家、政府和安全行业正在面临和需要尽快解决的重要问题。
从国内的“暗云Ⅲ”病毒,到席卷全球的“WannaCry”敲诈勒索病毒,再到“Petya”恶性破坏性病毒,无一不说明目前的网络安全形势严峻,企业安全防护脆弱,大力发展网络安全防护势在必行。
2大力加强网络安全建设,人才匮乏现状急需改善
我国虽然已成网络大国,但离网络强国还有距离。木马和僵尸网络、移动互联网恶意程序、拒绝服务攻击、安全漏洞、网页钓鱼、网页篡改等网络安全事件多有发生,基础网络设备、域名系统、工业互联网等我国基础网络和关键基础设施依然面临着较大的安全风险,加强网络安全建设迫在眉睫。
同时,我国网络安全人才匮乏的现状急需改善。作为一个网络大国,中国除研究开发计算机设备,提升网络传输速度以外,还应加紧计算机信息安全人才的培育工作,让中国从网络大国变为网络强国,这是提升我国信息安全保障的重要基础。
网络安全已经上升至国家战略,国家也在大力投入、推动网络安全建设。但做好网络安全工作不是某个机构、某个部门的事,而是需要全社会的参与。从武汉市地方出台《关于支持国家网络安全人才与创新基地发展的政策措施》投入45亿建设资金,到2017年6月1日正式施行的《中华人民共和国网络安全法》,都是为了网络安全健康、稳健的发展而做出的努力。我们也呼吁作为有社会责任的安全企业、机构、个人积极投入到网络安全建设中来,为国家、国民的网络安全防护贡献一份力量。
3腾讯推动建立中国首个最强互联网安全矩阵
腾讯安全拥有17年能力积累及8亿用户海量大数据运营经验,是中国最为领先的互联网安全产品、安全服务提供者。本着“开放、联合、共享”的理念,将多年积累的能力和数据共享给合作伙伴,致力于互联网安全开放平台建设,提升互联网安全产业链安全能力,提升用户安全意识,共同推进中国互联网安全环境的建设。
目前,腾讯已推动建立中国首个互联网安全矩阵,涵盖基础安全的实验室矩阵、安全产品矩阵、安全大数据平台矩阵,以及互联网安全开放平台矩阵,致力于中国互联网安全新生态建设,开放核心能力和数据,为中国互联网安全生态建设不懈努力。

一、网络安全整体现状扫描
1.1 影响全球的六大网络安全事件,累计影响遍及全球
1.1.1维基解密CIA绝密文件泄露事件
2017年3月7日,维基解密(WiKiLeaks)公布了数千份文档并揭秘了美国中央情报局关于黑客入侵技术的最高机密,根据泄密文档中记录的内容,该组织不仅能够入侵iPhone手机、Android手机和智能电视,而且还可以入侵攻击Windows、Mac和Linux操作系统,甚至可以控制智能汽车发起暗杀活动。外界将此次泄漏事件取名为Vault 7,Vault 7公布的机密文件记录的是美国中央情报局(CIA)所进行的全球性黑客攻击活动。
Vault7包含8761份机密文档及文件,这些文件记录了CIA针对Android以及苹果智能手机所研发的入侵破解技术细节,其中有些技术还可以拿到目标设备的完整控制权。维基解密创始人阿桑奇表示,文件显示出“CIA网络攻击的整体能力”,而维基解密在发布这些文件时声称“CIA的网络军械库已失控”。

1.1.2影子经纪人公开NSA(美国国家安全局)黑客武器库
2017年4月14日,影子经纪人(Shadow Brokers)在steemit.com上公开了一大批NSA(美国国家安全局)“方程式组织” (Equation Group)使用的极具破坏力的黑客工具,其中包括可以远程攻破全球约70%Windows机器的漏洞利用工具。任何人都可以使用NSA的黑客武器攻击别人电脑。其中,有十款工具最容易影响Windows个人用户,包括永恒之蓝、永恒王者、永恒浪漫、永恒协作、翡翠纤维、古怪地鼠、爱斯基摩卷、文雅学者、日食之翼和尊重审查。黑客无需任何操作,只要联网就可以入侵电脑,就像冲击波、震荡波等著名蠕虫一样可以瞬间血洗互联网。

1.1.3 “WannaCry”敲诈勒索病毒5月12日在全球爆发
2017年5月12日,“WannaCry”(想哭)比特币勒索病毒在全球范围内爆发,本次事件波及150多个国家和地区、10多万的组织和机构以及30多万网民,损失总计高达500多亿人民币。包括医院、教育机构以及政府部门,都无一例外的遭受到了攻击。勒索病毒结合蠕虫的方式进行传播,是此次攻击事件大规模爆发的重要原因。
用户中毒后最明显的症状就是电脑桌面背景被修改,许多文件被加密锁死,病毒弹出提示,要求用户向相关比特币地址转账300美元以便解锁文件。目前安全公司已经找到恢复加密文件的相关办法。

1.1.4 FireBall火球病毒感染超过2.5亿电脑
2017年6月1日,国外安全机构Check Point发报告称在国外爆发了“FireBall”病毒,并声称全球有超过2.5亿台电脑受到感染,其中受影响最大的国家分别是印度(10.1%)和巴西(9.6%)。美国有550万台电脑中招,占2.2%。受感染的企业网络中,印度和巴西分别占到43%和38%,美国则为10.7%。
此恶意软件强行将浏览器主页改为自家网站和搜索引擎,并将搜索结果重定向到谷歌或雅虎。这些伪造的搜索引擎跟踪用户数据,暗中搜集用户信息。而制作此病毒的作者为中国的Rafotech公司,目前该公司网站已无法访问。

1.1.5“暗云”系列病毒升级为“暗云III”再度来袭
2017年6月9日,腾讯电脑管家检测到,早在2015年就被首次发现并拦截查杀的“暗云”病毒死灰复燃,升级为“暗云Ⅲ”,通过下载站大规模传播,同时通过感染磁盘MBR实现开机启动,感染用户数量已达数百万。
升级过后的“暗云Ⅲ”将主要代码存储在云端,可实时动态更新,其功能目前主要有下载推广恶意木马、锁定浏览器主页、篡改推广导航页id等。用户一旦中招,电脑便会沦为“肉鸡”形成“僵尸网络”,并利用DDoS攻击影响搭建在某云服务商平台上的棋牌类网站,导致该网站访问变得异常卡慢。

1.1.6新一轮勒索病毒“Petya”来袭,更具破坏性
2017年6月27日,新一轮勒索病毒“Petya”袭击了欧洲多个国家,包括乌克兰、俄罗斯、印度、西班牙、法国、英国、丹麦等国在内都遭受了攻击,这些国家的政府、银行、企业、电力系统、通讯系统及机场等都受到了不同程序的影响。
此病毒相比“WannaCry”更具破坏性,病毒对电脑的硬盘MFT进行了加密,并修改了MBR,让操作系统无法进入。而根据相关的分析表示,开机界面上留下来的信息即使提供给黑客也是没有办法进行解密的,因此,不得不怀疑此次“Petya”病毒的真正目的。“Petya”更像是在做有目的性的攻击,对目标进行无法修复的破坏性攻击,而并非以敲诈勒索为目的。

1.2《中华人民共和国网络安全法》正式施行
6月1日,我国第一部全面规范网络空间安全管理的基础性法律——《中华人民共和国网络安全法》正式施行,共有七章七十九条,内容十分丰富,具有六大突出亮点。一是明确了网络空间主权的原则;二是明确了网络产品和服务提供者的安全义务;三是明确了网络运营者的安全义务;四是进一步完善了个人信息保护规则;五是建立了关键信息基础设施安全保护制度;六是确立了关键信息基础设施重要数据跨境传输的规则。
同时新法还指出应采取多种方式培养网络安全人才,促进网络安全人才交流。新法的施行标志着我国网络安全从此有法可依,网络空间治理、网络信息传播秩序规范、网络犯罪惩治等即将翻开崭新的一页,对保障我国网络安全、维护国家总体安全具有深远而重大的意义。
1.3中国网民规模相当于欧洲人口总量,安全人才缺口高达95%
1.3.1中国网民规模达7.31亿,相当于欧洲人口总量
截至2016年12月,我国网民规模达7.31亿,普及率达到53.2%,超过全球平均水平3.1个百分点,超过亚洲平均水平7.6个百分点。全年共计新增网民4299万人,增长率为6.2%。中国网民规模已经相当于欧洲人口总量。
1.3.2移动端网民规模持续增长,手机网民占比达95.1%
截至2016年12月,我国手机网民规模达6.95亿,增长率连续三年超过10%。台式电脑、笔记本电脑的使用率均出现下降,手机不断挤占其他个人上网设备的使用。
1.3.3安全人才缺口巨大,高达95%
虽然我国网民数量已居全球首位,但我国从事信息安全行业的人非常少,安全人才及其匮乏。据相关资料显示,近年我国高校教育培养的信息安全专业人才仅3万余人,而网络安全人才总需求量则超过70万人,缺口高达95%。7.1亿中国网民的网络安全问题,已成为行业乃至国家亟待解决的问题。
北京电子科技学院副院长、教育部高等学校信息安全专业教学指导委员会秘书长封化民指出,当前中国重要行业信息系统和信息基础设施需要各类网络信息安全人才还将以每年1.5万人的速度递增,到2020年相关人才需求将增长到140万。但是目前,我国只有126所高校设立了143个网络安全相关专业,仅占1200所理工院校的10%。
二、2017上半年网络病毒威胁形势分析
2.1腾讯安全反病毒实验室PC端病毒拦截超10亿,环比增30%
2.1.1 木马病毒拦截量平均每月近1.7亿次
2017年上半年腾讯安全反病毒实验室统计数据显示,PC端总计已拦截病毒10亿次,病毒总体数量相比2016年下半年腾讯安全反病毒实验室拦截的病毒数增长30%;平均每月拦截木马病毒近1.7亿次。4月、6月为拦截病毒的高峰,拦截量均为1.8亿次。

2017年Q2季度相较于2016年Q2季度,腾讯安全反病毒实验室病毒拦截量同比增长了23.7%。从2014年到2017年Q2季度病毒拦截量来看,恶意程序数量逐年攀升。

2.1.2 PC端广东用户中毒最多,中毒高峰期为上午9-11点
2.1.2.1 上半年共发现2.3亿次用户机器中木马病毒
2017年上半年腾讯安全反病毒实验室共发现2.3亿次用户机器中木马病毒,相比2016年下半年下降0.5%,平均每月为3,880万中毒机器进行病毒查杀。2017年Q2季度相比Q1季度中毒机器数略有增长。

2017年Q2季度相较于2016年Q2季度报毒用户量同比增长3%。从2015年到2017年Q2季度中毒机器数增长趋势明显,呈逐年递增状态。

2.1.2.2 PC端用户中毒高峰期为上午9点到11点
根据统计,每天中毒高峰时间为上午10点-上午11点,符合企业及普通用户上午9点-上午11点开启电脑处理工作的规律。这段时间用户中毒的病毒类型较多为利用邮件、共享等方式传播的Office文档类宏病毒,说明企业办公安全防护形势依旧严峻。

2.1.2.3 PC端中毒用户省份最多为广东,其中深圳市居首
根据腾讯安全反病毒实验室监测到的中毒PC数量统计,从城市分布来看,互联网较为发达的城市用户中毒情况较重,全国拦截病毒排名第一城市为深圳市,占全部拦截量的3.76%,第二名为成都市,占全部拦截量的3.57%,第三名为广州市,占全部拦截量的3.39%。

从省级地域分布来看,全国PC中毒数量最多的是广东省,占全部拦截量的13.29%,第二名为江苏省,占全部拦截量的7.75%,第三名为山东省,占全部拦截量的7.12%。

2.1.3第一大病毒种类为占比53.8%的木马病毒,勒索病毒新增13.39%
2.1.3.1 PC端第一大种类病毒依然是木马,PE感染型病毒种类少但传播性大
根据腾讯安全反病毒实验室2017年Q2季度获取到的病毒样本分析,从病毒种类上,木马类占总体数量的53.80%,依然是第一大种类病毒。Adware类(广告软件、强制安装、收集用户隐私、弹垃圾信息等)为第二大病毒类,占总体数量的39.02%。后门类为第三大病毒类,占总体数量的5.13%。相比2017年Q1季度,病毒种类并没有太大变化。

从病毒样本的数量上来划分,排在第一位和第二位的仍然是木马类和Adware类,但排在第三位的变成了PE感染型,占总体数量的25.07%。

感染型样本的种类并不多,这与感染型病毒制作难度大、黑客等编程人员需要掌握的技术多、成本高、开发时间久等因素有关。同时,感染型病毒的传播性很大,存活时间相对也比较久,因此,种类少的PE感染型种类在样本传播量级上占了一定的比例,这也是由于感染型病毒具有大范围感染、快速传播的特性。
2.1.3.2敲诈勒索病毒样本数量Q2新增13.39%,第一并不是WannaCry
敲诈勒索病毒是以敲诈勒索钱财为目的,使得感染该木马的计算机用户系统中的指定数据文件被恶意加密,造成用户数据丢失。目前,由国外传进国内的敲诈勒索病毒大多需要支付比特币赎金才能进行解密。由于比特币完全匿名流通,目前技术手段无法追踪敲诈勒索病毒背后的幕后操纵者,这也使得敲诈勒索病毒从2013年后呈现爆发式增长。
敲诈勒索病毒查杀量
根据腾讯安全反病毒实验室检测到的敲诈勒索病毒显示,2017上半年总计已发现敲诈勒索病毒样本数量在300万左右,平均每月检测到敲诈勒索病毒数量近50万个,Q2季度勒索病毒样本数量较Q1季度新增13.39%。5月、6月为拦截病毒的高峰,分别为57万个、53万个。

敲诈勒索病毒种类
根据相关数据分析显示,5月12日爆发的WannaCry敲诈勒索病毒是本季度最活跃、影响最大的病毒。该病毒与其他病毒在传播方式上有显著差异,由于使用了windows系统漏洞,使得该病毒能够在全球范围内传播,成为本季度的热点安全事件。在6月27号一种名为Petya的新型勒索病毒开始在世界各地传播,其敲诈手段与WannaCry相似,但更具有破坏性,直接加密了用户硬盘的MFT并修改了MBR,导致用户无法进入到windows系统。
以上病毒影响虽大,但从样本量上来看,最大的还是带有感染传播方式的PolyRansom病毒。此病毒会感染、加密用户的文件进行敲诈,但由于并没有使用像WannaCry病毒之类的密钥加密方式,而是使用了简单的加密算法,并且算法可逆,杀毒软件可以帮助用户正常恢复文件,因此虽然在样本量上排名第一,但影响并不是很大。此类敲诈病毒占了所有敲诈类病毒的78.84%,由此可见感染型病毒的传播能力之强。

从样本量上来看,除感染型敲诈病毒外,排在第一的是Blocker,占全部敲诈类病毒的36.82%,第二大类是Zerber,占全部敲诈类病毒的23.63%,第三大类才是本季度影响最大的WannaCry敲诈病毒,占全部敲诈类病毒的12.06%。WannaCry病毒量之所以快速上升到了第三的位置,是因为传播手段使用了漏洞传播。

目前的敲诈勒索病毒主要采用以下几种传播方式:

文件感染传播
文件感染传播是利用感染型病毒的特点进行传播,如PolyRansom病毒就是利用感染型病毒的特点,加密用户所有文档后再弹出勒索信息。由于PE类文件被感染后具有了感染其他文件的能力,因此如果此文件被用户携带(U盘、网络上传等)到其他电脑上后运行,就会使得该电脑的文件也被全部感染加密。
网站挂马传播
网站挂马通过是在获取网站或者网站服务器的部分或全部权限后,在网页文件中插入一段恶意代码,这些恶意代码主要包括IE等浏览器漏洞利用代码。用户访问被挂马的页面时,如果系统没有更新恶意代码中利用的漏洞补丁,则会执行恶意代码。
该类病毒也可以利用已知的软件漏洞进行攻击,例如利用Flash、PDF软件漏洞,向网站中加入带有恶意代码的文件,用户使用带有漏洞的软件打开文件后便会执行恶意代码,下载病毒。
利用系统漏洞传播
5月爆发的WannaCry就是利用Windows系统漏洞进行传播,利用系统漏洞传播的特点是被动式中毒,即用户没有去访问恶意站点,没有打开未知文件也会中毒。此种病毒会扫描同网络中存在漏洞的其他PC主机,只要主机没有打上补丁,就会被攻击。
腾讯反病毒实验室提醒大家,及时更新第三方软件补丁,及时更新操作系统补丁,以防被已知漏洞攻击。
邮件附件传播
通过邮件附件进行传播的敲诈勒索病毒通常会伪装成用户需要查看的文档,如信用卡消费清单、产品订单等。附件中会隐藏恶意代码,当用户打开后恶意代码便会开始执行,释放病毒。这类伪装病毒通常会批量发送给企业、高校、医院机构等单位,这些单位中的电脑中通常保存较重要的文件,一旦被恶意加密,支付赎金的可能性远远超过普通个人用户。
网络共享文件传播
一些小范围传播的敲诈勒索病毒会通过共享文件的方式进行传播,病毒作者会将病毒上传到网络共享空间、云盘、QQ群、BBS论坛等地方,以分享的方式发送给特定人群诱骗下载安装。
腾讯反病毒实验室提醒用户,下载软件请到官方正规渠道下载安装,切勿下载未知程序,如需要使用未知来源的程序,可提前安装腾讯电脑管家进行安全扫描。
2.2 移动端共查杀Android病毒6.93亿次,手机染毒用户数超1亿
2.2.1移动端病毒包增长趋势减缓,但总数仍有899万
2017年上半年腾讯手机管家截获Android新增病毒包总数达899万,相较2016年上半年有小幅度下降,但总数仍十分巨大。

2.2.2 移动端广东用户中毒最多,染毒手机用户数同比减少45.67%
2.2.2.1上半年腾讯手机管家共查杀Android病毒6.93亿次
在病毒感染用户数大幅下降的情况下,2017年上半年腾讯手机管家查杀病毒次数却达到6.93亿次,同比增长124.24%,总数是2016年上半年的一倍有余。恶意程序和木马病毒的制作成本降低、病毒传播渠道多样化是造成这一现象的重要因素。

除6月以外,2017年上半年每月查杀病毒次数均超过1亿次,其中1月份查杀次数更高达1.36亿次,几乎与2014年上半年1.4亿的查杀次数持平。

2.2.2.2 2017年上半年染毒手机用户数超1亿
2017年上半年病毒感染用户数为1.09亿,同比减少45.67%,与2015年、2016年上半年相比皆有所下降。

2017年1月单月感染用户数达到2166万,为上半年最高纪录,此后感染用户数开始缓慢下降。

2.2.2.3 移动端中毒用户数量广东居首
在感染手机病毒的用户地域分布方面,广东排名第一,占比高达11.41%。

2.2.3流氓行为和资源占比超80%,二维码最易中毒
2.2.3.1移动端病毒中流氓行为和资费消耗占比超80%
2017年上半年手机病毒类型比例中,流氓行为和资费消耗占比最高,以44.59%和44.44%的比例分列一、二位。排名第三的隐私获取同样占据了5.85%,诱骗欺诈、恶意扣费、远程控制、系统破坏和恶意传播占比分别为1.94%、1.55%、0.80%、0.74%和0.08%。

流氓行为是指病毒私自执行具有流氓属性的恶意行为。如近期因WannaCry病毒而再次引起关注的手机锁屏勒索病毒就带有流氓行为。这类病毒主要通过论坛贴吧等途径进行扩散,制毒者通常会利用外挂、免费、刷钻、红包等字眼对木马病毒进行包装,诱导用户下载安装。病毒完成安装后就会强制锁定手机屏幕,迫使受害者不得不联系制毒者付款,才能使设备恢复正常。

不管是电脑还是手机,带有流氓行为的勒索病毒给用户带来的损失都是难以估量的,如果不慎中毒,不仅会造成财产损失,还将导致重要资料丢失,因此用户应谨慎防范。
资费消耗也是常见的手机病毒类型,此类病毒通常在用户不知情或未授权的情况下,通过发送短信、频繁连接网络等方式,导致用户资费损失。部分恶意推广病毒以帮助第三方广告商提高点击量为目的,通过诱导用户下载安装病毒,获取手机Root权限,执行下载恶意广告软件。这些软件会不断推送各种弹窗广告,影响用户手机体验,更甚者还会泄露用户隐私信息、盗走网银账户等,造成严重的人身及财产安全。

感染了全球超3600万安卓设备的恶意广告点击软件“Judy”就属于资费消耗类手机病毒。该恶意软件暗藏于一款韩国手游中,在完成下载安装后,会将感染设备的信息发送到目标页面,并在后台自动下载恶意代码并访问广告链接,盗刷用户流量,给用户造成资费消耗。
2.2.3.2 二维码、软件捆绑是移动病毒主要渠道来源
手机病毒渠道来源主要有七大类,分别是二维码、软件捆绑、电子市场、网盘传播、手机资源站、ROM内置和手机论坛。病毒渠道入口的分散化与多元化,也进一步增加了用户染毒的几率与风险。

2017年上半年,二维码成为了主流病毒渠道来源,占比高达20.80%。二维码在各大领域的普及让越来越多的用户养成了随手扫码的习惯,制毒者也因此加大针对二维码渠道的病毒包投放比例。部分被嵌入病毒的二维码,只要一扫就会自动下载恶意病毒,轻则造成手机中毒,重则导致个人隐私信息泄露,造成财产损失等。
三、反骚扰诈骗效果显著,但用户损失形势严峻
3.1上半年垃圾短信数超5.86亿条,非法贷款类超50%
3.1.1 2017年上半年垃圾短信持续增长 总数接近6亿
较低的传播成本及其背后存在的巨大利益链,导致垃圾短信一直难以得到有效整治,用户举报数也是有增无减。2017年上半年,腾讯手机管家共收到用户举报垃圾短信数5.86亿条,同比增长40.69%,是2014年上半年的2倍有余。

3.1.2用户举报垃圾短信最多的省份为广东,最多的城市为深圳
在垃圾短信的地域省份分布方面,用户举报垃圾短信最多的前三省份分别为广东、江苏和山东,占比分别为12.91%、6.98%和5.70%。此外河南、浙江、四川、河北、北京、湖南和上海同样位列前十。这些省份或直辖市普遍分布在东部沿海和中部地区,人口密集和经济发达是它们最大的共同点,这也为诈骗分子批量发送垃圾短信并牟取利益创造了有利条件。

城市方面,2017年上半年深圳用户共举报垃圾短信2334万条(占比3.98%),成都、广州和苏州分列二至四位,垃圾短信举报数均为千万级别。

3.1.3 2017年上半年常见的诈骗短信类型
虽然诈骗短信举报量整体呈现下降趋势,但其手段的多样化和隐秘性却让诈骗短信的危害性始终高居不下。据腾讯手机管家监测到的2857万条诈骗短信显示,非法贷款、网购、病毒网址、恶意网址和伪基站是占比最高的几大诈骗短信类型。
其中非法贷款类诈骗短信一家独大,占比超过50%。在现代人“有房万事足”和依靠买房寻求安全感的社会大背景下,贷款买房成为了一大社会需求。骗子也紧跟这一社会痛点,大量发送非法贷款短信,借此牟利。

3.2骚扰电话用户标记量达2.35亿次,同比下降27.12%
3.2.1 2017年上半年用户共标记骚扰电话2.35亿次 同比下降27.12%
在经历了2015年上半年的爆发式增长后,2016年上半年开始,骚扰电话标记数呈现逐年下降趋势,2017年上半年骚扰电话标记总数为2.35亿次,相较2016年上半年同比下降27.12%。

3.2.2 2017年上半年骚扰电话超过50%为响一声
用户标记的骚扰电话类型主要分为5大类。其中,响一声排名第一,占比超过50%。这类骚扰电话虽然不会对用户造成实质性危害,但仍会影响手机使用,干扰用户。诈骗电话占比15.14%,排名第二,此外广告推销、房产中介和保险理财等也占据了一定比例。

3.2.3 骚扰电话中索要验证码占比最高
据腾讯手机管家用户主动上报的骚扰电话恶意线索情况显示,索要验证码、假冒领导、转账、网购和犯法是最常见的关键词。其中索要验证码占比最高,将近24.74%的骚扰电话中,骗子会通过各种手段索要验证码,而验证码作为重要的隐私信息,一旦泄露,很容易会造成财产损失。

3.2.4 诈骗电话标记数同比下降59.68%,北京最多
在用户已标记的2.35亿次骚扰电话中,诈骗类电话占比虽远不及响一声多,但其造成的实质性危害却最大。基于腾讯手机管家用户诈骗电话标记相关数据显示,2017年上半年诈骗电话标记数同比下降59.68%,总数为3559万。

这些诈骗电话针对的目标地域较为明确,以东部沿海经济发达地区与内陆中心省份为主。城市方面,北京是诈骗电话标记数最多的城市,总数达182.6万。深圳和广州分别以141.8万和125.7万的标记数紧随其后。上海、西安、长沙、成都、杭州、重庆和武汉则分列第四至十位。

3.3 恶意网址拦截次数高达478亿,色情欺诈网站居首
3.3.1 2017年上半年检出恶意网址数量超1.83亿
2017年上半年,腾讯安全在PC和移动端共计检测出恶意网址数量超过1.83亿,整体呈现波动上升趋势。其中6月份检测出3575万个恶意网址,为上半年最高纪录,4月份则最低,检测数量为2553万。

3.3.2色情欺诈网站仍是恶意网址主要作案手段
在有效检测恶意网址的同时,2017年上半年腾讯安全在PC和移动端共拦截恶意网址高达478亿次,相当于每天拦截2.65亿次。这一庞大数据也进一步说明了互联网安全的严峻形势。

在腾讯安全拦截的恶意网址中,色情欺诈网站、博彩网站、信息诈骗、恶意文件、虚假广告和钓鱼欺诈网站是传播最广泛的六大类恶意网址。其中色情欺诈网站占据半壁江山,占比为51.98%,色情欺诈网站会内嵌欺诈广告或诱骗用户进行在线支付。恶意网址也会内嵌在诈骗短信中进行传播,以增加迷惑性,因此用户在看到短信中的网址时,应自觉提高警惕性,切记不要随便点击。

3.4 iOS骚扰及诈骗电话降幅约35%,日历广告成新的骚扰
3.4.1 iOS骚扰电话和诈骗电话出现较大幅度下降
2016年9月,腾讯手机管家携手苹果公司推出iOS10全新版本,首次增加拦截骚扰和诈骗电话功能,有效缓解了iOS用户倍受困扰的骚扰电话难题。数据显示,2017年上半年iOS用户共标记骚扰电话1449.2万次,诈骗电话219.6万次。
从整体趋势上看,上半年iOS骚扰电话标记数呈现波动下降趋势,1月标记数最高,为319.5万次,4月则只有202万次,为上半年最低峰。相较而言,诈骗电话整体趋势则更加稳定。从以上各项数据可以看出,2017年上半年骚扰电话和诈骗电话都出现了较大幅度的下降,这离不开相关部门、手机运营商和手机用户的共同努力。

3.4.2日历广告成苹果手机的第三大骚扰
垃圾信息、骚扰电话、日历广告逐渐成为iPhone用户的主要骚扰源头。其中,日历广告骚扰问题日益严重。61.1%的用户遭遇过日历广告,其中博彩广告、房地产广告、打车软件广告居前三。

3.5 腾讯麒麟系统打击伪基站保护1.5亿人次
3.5.1腾讯麒麟系统共拦截2.3亿条诈骗短信,保护1.5亿人次
2017年上半年度,腾讯麒麟伪基站实时定位系统为全国用户拦截2.3亿条伪基站诈骗短信,总计影响人数达1.5亿人次。
3.5.2伪基站地域特征:川陕京鄂湘五省最多
从地域上看,腾讯麒麟为四川、陕西、北京、湖北、湖南用户拦截的诈骗短信数量最多,这5个省级行政区拦截的诈骗短信数量超过全国总量50%以上。

从城市来看,拦截诈骗短信数量Top 10的城市如北京、成都、西安等几乎均为省会城市或经济较发达城市,由于人口密集、城市居民收入较高,被伪基站诈骗团伙列入重点攻击对象。

3.5.3 伪基站作案时间特征:工作时间最频繁
从作案时间来看,伪基站诈骗短信发送之间集中在上午9时至下午19时,其中又以上午10时至12时、下午15时至18时为两个高峰。不难看出,诈骗短信高峰期与每日工作时段相合。

3.5.4内容特征:工商银行、中国移动最“躺枪”
伪基站短信类型中,积分兑换、账户异常和银行信用卡提额类则占比接近90%。这三类常与运营商、银行有关,常以积分到期清零、信用卡提额、账户实名、异常等理由进行诈骗。

腾讯麒麟拦截的伪基站仿冒端口中,仿冒工商银行的诈骗短信最多(高达52%),Top 5仿冒端口除中农工建四大银行,还有运营商中国移动。不难看出,这些“躺枪”的企业是因为用户群体巨大,业务模式中短信息又尤为重要,所以成为伪基站诈骗团伙主要模拟的发送对象。

伪基站短信触达用户的运营商分布中,中国移动占比74%,位居其后是中国电信(16%)、中国联通(10%)。

四、2017年上半年安全人才建设进展及成果
4.1《网络安全法》促进对人才的综合性培养
2017年6月1日起施行的《网络安全法》首次以法律条款的形式对网络空间安全领域的人才问题进行规定,不仅体现出国家对网络人才的重视,更是为国务院以及各地方出台网络安全人才培养的细则提供了最高位阶的法律依据。
《网络安全法》规定:国家支持企业和高等学校、职业学校等教育培训机构开展网络安全相关教育与培训,采取多种方式培养网络安全人才,促进网络安全人才交流。网络安全人才不仅包括技术人才,也包括管理人才。当前网络安全不仅是技术的较量,更是理念、规则的较量,熟悉国际规则、大国关系的网络安全人才在未来的网络空间竞争中能够发挥更大的作用。因此,网络安全人才的培养不仅要培养传统型人才,更要立足国内,放眼全球,培养懂得网络外交的综合性人才。
同时,条款中规定的“网络安全人才的交流”,体现了我国对于人才培养机制的开放创新理念。人才的培养离不开与先进国家的学术研讨和技术交流,各企业机构应当吸引国外的高端技术人才,同时加快我国顶尖人才的培养。
4.2 安全人才培养“腾讯模式”:打造人才闭环
作为互联网安全开放平台的倡导者,腾讯一直将“网络安全”当作企业顶层设计的重要组成部分和战略性工程。在持续关注和支持安全人才选拔和培养的过程中,腾讯目前已经逐渐在校园招聘、社会招聘、内部人才的培训晋升、薪酬福利等方面摸索出一套安全人才选拔制度;同时,通过持续打造顶级安全赛事和推动人才培养计划,腾讯已经逐渐形成一套成熟、完善,并可供社会借鉴的安全人才培养体系。
腾讯在2017年联合各方发起了腾讯信息安全争霸赛(TCTF),通过国际化的赛制发掘人才、通过优质辅导机制和专业的导师队伍培养人才以及通过搭建企业与高校的桥梁输送人才。同时,腾讯通过打造“百人计划”,构建互联网安全人才培养的闭环,通过TCTF大赛的层层比赛考试,选拔出最具潜力的百名安全人才,并通过后续持续培养,打造互联网安全领域复合型、领军型人才。
腾讯希望以TCTF作为专业安全人才培养平台在企业与高校间搭建起桥梁,形成集选拔、培养、输送于一体的人才闭环,为中国安全新生力量提供多维的成长环境,进一步推动我国网络安全事业发展。
4.3腾讯安全联合实验室成立一周年:护航六大互联网关键领域
2016年7月,腾讯安全整合旗下实验室资源,成立国内首个互联网实验室矩阵——腾讯安全联合实验室,旗下涵盖包括科恩实验室、玄武实验室、湛泸实验室、云鼎实验室、反病毒实验室、反诈骗实验室、移动安全实验室在内的七大实验室。实验室专注安全技术研究及安全攻防体系搭建,安全防范和保障范围覆盖了连接、系统、应用、信息、设备及云,触达六大互联网关键领域。
2016年,腾讯安全联合实验室为谷歌、微软、苹果、adobe等国际厂商共计挖掘269个漏洞,位居国内第一。另外,凭借“全球首次远程无物理接触方式入侵特斯拉汽车”研究成果,腾讯安全联合实验室科恩实验室入选“特斯拉安全研究员名人堂”,并获特斯拉CEO马斯克的亲笔致谢。
在举国关注的反诈骗领域,腾讯安全联合实验室中的反诈骗实验室基于多年来在反诈骗领域的深耕研究,已经形成一整套基于AI创新+能力开放的反欺诈评价新标准,形成有效的止损模式。在AI创新和能力开放的双轮驱动下,实验室目前已推出鹰眼反电话诈骗系统、麒麟伪基站实时定位系统、神荼反钓鱼系统、神侦资金流查控系统、神羊情报分析平台五大系统,并通过腾讯云的SaaS服务开放给有需要的政府单位、企业等,帮助用户防范互联网诈骗。
五、安全热点事件盘点
5.1 勒索病毒集中爆发及病毒详解
5.1.1 WannaCry敲诈勒索病毒5月12日在全球爆发
事件背景:
5月12日,WannaCry(想哭)比特币勒索病毒让在全球范围内爆发。据腾讯安全反病毒实验室安全研究人员分析发现,此次勒索事件与以往相比最大的区别在于,勒索病毒结合了蠕虫的方式进行传播。由于在NSA泄漏的文件中,WannaCry传播方式的漏洞利用代码被称为“EternalBlue”,所以也有的报道称此次攻击为“永恒之蓝”。
病毒详解:
勒索病毒近两年的爆发,很大程度上与加密算法的日益完善有关。密码学及算法的不断更新保证了我们日常网络中数据传输和保存的安全性。遗憾的是,勒索病毒的作者也利用了这个特性,使得我们虽然知道了木马的算法,但由于不知道作者使用的密钥,也就没有办法恢复被恶意加密的文件。
加密算法通常分为对称加密算法和非对称加密算法两大类。这两类算法在勒索病毒中都被使用过。
对称加密算法的加密和解密使用的是完全相同的密钥,特点是运算速度较快,但是单独使用此类算法时,密钥必须使用某种方法与服务器进行交换,在这个过程中存在被记录和泄漏的风险。勒索病毒常用的对称加密算法包括AES算法和RC4算法。
非对称加密算法也被称为公钥加密算法,它可以使用公开的密钥对信息进行加密,而只有私钥的所有者才可以解密,因此只要分发公钥并保存好私钥,就可以保证加密后的数据不被破解。与对称加密相比,非对称加密算法的运算速度通常较慢。勒索病毒常用的非对称加密算法包括RSA算法和ECC算法。
通常,勒索病毒会将这两大类加密算法结合起来使用,既可以迅速完成对整个电脑大量文件的加密,又能保证作者手中的私钥不被泄漏。
5.1.2 新一轮勒索病毒“Petya”来袭,更具破坏性
事件背景:
6月27日新一轮勒索病毒Petya袭击了欧洲多个国家。此病毒相比WannaCry更具破坏性。病毒对电脑的硬盘MFT进行了加密,并修改了MBR,让操作系统无法进入。相比此前,Petya更像是有目的性的攻击,而并非简单的敲诈勒索。腾讯哈勃分析系统已经能够识别此病毒并判定为高度风险,利用腾讯电脑管家可查杀该病毒。
病毒详解:
Petya勒索病毒变种中毒后会扫描内网的机器,通过永恒之蓝漏洞自传播,达到快速传播的目的。有国外安全研究人员认为,Petya勒索病毒变种会通过邮箱附件传播,利用携带漏洞的DOC文档进行攻击。中毒后,病毒会修改系统的MBR引导扇区,当电脑重启时,病毒代码会在Windows操作系统之前接管电脑,执行加密等恶意操作。电脑重启后,会显示一个伪装的界面,此界面实际上是病毒显示的,界面上假称正在进行磁盘扫描,实际上正在对磁盘数据进行加密操作。
5.1.3勒索病毒腾讯安全应对方案
针对勒索病毒集中爆发,腾讯安全紧急发布应对方案,针对事前防范、事中病毒清理和事后文件恢复三种情形,向广大用户提出处理建议:
事前预防
1.利用电脑管家的勒索病毒免疫工具,自动化安装系统补丁和端口屏蔽,或手动下载、安装。
2.备份数据,安装安全软件,开启防护。
a)对相关重要文件采用离线备份(即使用U盘等方式)等方式进行备份;
b)利用部分电脑带有的系统还原功能,在未遭受攻击之前设置系统还原点,遭受攻击之后可以还原系统,防御文件加密;
c)安装腾讯电脑管家,开启实时防护,避免遭受攻击;
d)采用电脑管家的文档守护者进行文件的备份、防护。
3.建立灭活域名实现免疫。
根据对已有样本分析,勒索软件存在触发机制,如果可以成功访问指定链接,电脑便会在中了勒索病毒后直接退出,便不会进行文件加密。
a)普通用户在可以联网状态下,保证对该网址的可访问,则可以避免在遭受攻击后避免被加密(仅限于已知勒索病毒);
b)企业用户可以通过在内网搭建Web Server,然后通过内网DNS的方式将域名解析到Web Server IP的方式来实现免疫;通过该域名的访问情况也可以监控内网病毒感染的情况。
事中病毒清理
1.拔掉网线等方式隔离已遭受攻击电脑,避免感染其他机器。
2.利用电脑管家的杀毒功能直接查杀勒索软件,直接进行扫描清理(已隔离的机器可以通过U盘等方式下载离线包安装)。
3.备份相关数据后直接进行系统重装。
事后文件恢复
1.勒索软件带有恢复部分加密文件的功能,可以直接通过勒索软件恢复部分文件;或直接点击勒索软件界面上的”Decrypt”可弹出恢复窗口,恢复列表中文件。
2.可以使用第三方数据恢复工具尝试数据恢复,云上用户可直接联系腾讯安全云鼎实验室协助处理。
5.2 DDOS攻击不断,暗云变种频繁来袭
事件背景:
6月9日,一场2017年以来最大规模的DDoS网络攻击活动席卷全国,腾讯安全云鼎实验室发布溯源分析报告,通过对攻击源机器进行分析,工程师在机器中发现暗云Ⅲ的变种。通过对流量、内存DUMP数据等内容进行分析,腾讯云鼎实验室确定本次超大规模DDoS攻击由“暗云”黑客团伙发起。升级过后的“暗云III”将主要代码存储在云端,可实时动态更新。
病毒详解:
“暗云”系列木马自2015年初被腾讯反病毒实验室首次捕获并查杀,至今已有两年多。在这两年多时间里,该木马不断更新迭代,持续对抗升级。
从今年4月开始,该木马卷土重来,再次爆发,本次爆发的暗云木马相比之前的版本有比较明显的晋级特征,因此我们将其命名为暗云Ⅲ。暗云Ⅲ与之前版本相比有以下特点和区别:
第一、更加隐蔽,暗云Ⅲ依旧是无文件无注册表,与暗云Ⅱ相比,取消了多个内核钩子,取消了对象劫持,变得更加隐蔽,即使专业人员,也难以发现其踪迹。
第二、兼容性,由于该木马主要通过挂钩磁盘驱动器的StartIO来实现隐藏和保护病毒MBR,此类钩子位于内核很底层,不同类型、品牌的硬盘所需要的 hook点不一样,此版本木马增加了更多判断代码,能够感染市面上的绝大多数系统和硬盘。
第三、针对性对抗安全软件,对安全厂商的“急救箱”类工具做专门对抗,通过设备名占坑的方式试图阻止某些工具的加载运行。
5.3上半年重点诈骗类案件盘点
5.3.1 8.19徐玉玉电信诈骗案宣判
2016年8月,刚刚被南京邮电大学的徐玉玉,接到了一通诈骗电话,对方以奖学金的名义,骗走徐玉玉上大学的费用9900元。报案后的徐玉玉情绪异常,导致心源性猝死,不幸离世,引发社会对电信诈骗的空前关注。此案于2017年7月19日公开宣判,主犯陈文辉被判处无期徒刑,没收个人全部财产。其他六名被告人被判15年到3年不等的有期徒刑并处罚金。这一判决,向社会传递了法院依法从严惩处电信网络诈骗犯罪的鲜明态度。
防范建议:徐玉玉的惨剧足够引起公众的警惕。互联网时代,每个人的信息流转都在线上通过不同的渠道流转,给了不法分子可乘之机。面对如此环境,我们更应该对陌生电话和短信保持警觉。哪怕对方能说出个人精确的信息,都不能亲信,任何事件都需要经由可靠渠道多方验证,以保护自身安全。
5.3.2河南特大电信诈骗案:谎称卖高考答案骗近百考生300万元
2017年6月,河南鹤壁市警方破获了这起特大电信诈骗案,抓获犯罪嫌疑人两人,缴获作案用银行卡70余张。这些犯罪嫌疑人假借售卖高考试题答案的方式,通过网络对高考考生实施诈骗。据警方初步调查,诈骗受害人累计超过3500余人,涉案金额超过300万元。
防范建议:每年高考录取期间,都是高考诈骗案件高发的时间段。考生和家长需要谨防一切所谓“内部指标”、虚假查分网址、虚假查询录取结果等以高考招生为名的各种诈骗手段,切勿抱有侥幸心理,上当受骗。
5.3.3武汉女教师遭遇连环电信诈骗 7个月被骗253万
武汉某中学教师陈女士,名校硕士学历,2017年5月向警方报警遭遇诈骗。据了解,2016年11月,陈老师接到一陌生来电,称其社保卡被盗刷,并直接将电话转至“湖南省公安厅”。接电话的“民警“称陈女士牵涉到一桩诈骗洗钱案,为“洗刷罪名”,陈女士半年时间累计向对方转账253万,为此欠下债务达300多万。目前案件仍在侦办中。
防范建议:民众需要警惕陌生电话和短信。当接到疑似诈骗电话或短信时,要注意核实对方身份,尤其是对方要求向指定账户汇款时,不要轻易汇款,应第一时间告知家属商量解决或咨询公安机关;。公安部门不可能提供安全账户,更不会指导您转账、设密码。
六、安全防范专家建议
在电脑使用中,设置安全系数高的密码。使用不会被暴力攻击轻易猜到的密码,是提高安全性的有效办法。暴力攻击是攻击者使用自动化系统来猜测密码。避免使用从字典中能找到的单词,不要使用纯数字密码;使用包含特殊字符和空格,同时使用大小写字母,这种密码破解起来比使用母亲的名字或生日作为密码要困难的多。另外,密码长度每增加一位,密码字符构成的组合就会成倍数增加,因此长密码会更加安全。
定期升级软件,更新安全补丁。很多情况下,在安装部署生产性应用软件之前,对系统进行补丁测试工作是至关重要的,最终安全补丁必须安装到个人电脑的系统中。如果很长时间没有进行安全升级,可能会导致计算机非常容易成为不道德黑客的攻击目标。因此,不要把软件安装在长期没有进行安全补丁更新的计算机上。
通过备份重要文档,保护你的数据安全。备份你的数据,这是你可以保护自己在面对灾难的时候把损失降到最低的重要方法之一。如果数据量巨大,日常可以将数据保存至硬盘上。但更便捷的方式,可以利用腾讯电脑管家一类的安全防护软件,随时将数据自动化备份至本地,也可以存储至云端,最大化保证了数据安全。
不要轻易信任外部网络,开放性网络风险巨大。在一个开放的无线网络中,例如在具有无线网络的咖啡店中,网络风险会成倍增长,这个理念是非常重要的。这并非意味着在一些非信任的外部网络中不能使用无线网络,而是要时刻保持对用网安全的谨慎和警惕。关键是,用户必须通过自己的系统来确保安全,不要相信外部网络和自己的私有网络一样安全。
提高对陌生电话、短信的警惕性,勿轻信其中内容。诈骗短信形式多样化,各种新型短信木马泛滥使得通过诱惑性的短信自带病毒链接的支付类、隐私窃取类病毒迅速增长。对于“高考查分”、“开学通知”、“考试成绩单”、“户籍管理”、“手机实名制”、“录像视频”和“交通违章”等短信中内嵌的网址链接,应时刻提高警惕,切勿随意点击。对于陌生电话、短信应该提高警惕性和戒心,不要轻信对方所说的任何内容,必要时要对其身份信息进行核实。
保护个人隐私信息,不轻易向他人透露个人信息。个人账号、密码、身份证信息等属于关键个人隐私信息,因此绝对不能随意在任何陌生短信、电话进行透露。收到陌生短信、电话询问个人隐私时,请务必提高警惕。在社交平台发布消息时,谨防通过照片、截图等形式泄露重要隐私信息。不随意丢弃含有个人信息的机票、车票或快递单据,以防个人信息被窃取。
手机用户应养成使用安全软件来保护手机安全的良好习惯。手机用户可下载安装如腾讯手机管家一类的手机安全软件,定期给手机进行体检和病毒查杀,并及时更新病毒库。针对最新流行且难以清除的病毒或者漏洞,可下载专杀工具及时查杀或修复。同时开启腾讯手机管家骚扰拦截功能,可有效拦截诈骗电话、短信,提升手机安全。
Referring URL:
https://guanjia.qq.com/news/n1/2039.html