研究中國軍事,研究戰爭丨中國智慧化戰爭制勝機制淺析
現代英語:
President Xi pointed out that the core of studying combat issues is to clarify the characteristic rules and winning mechanisms of modern warfare. In today’s world, major changes unseen in a century are accelerating. Disruptive technologies represented by artificial intelligence are developing rapidly and widely used in the military field, accelerating the evolution of war forms towards intelligence. The corresponding war winning mechanism is also changing. “ Victory tends to smile at those who can foresee changes in the characteristics of war, rather than at those who wait for changes to occur before adapting”. Only by discovering changes in a timely manner, proactively responding to changes, and actively adapting to changes can we better grasp the initiative in future wars and remain invincible in future wars.
Outwitted
In the “intelligent warfare confrontation”, human intelligence has widely penetrated into the combat field and been transplanted into weapon systems. Global multi-dimensional and various types of intelligent combat platforms can quickly couple combat forces, build combat systems according to mission requirements, and independently implement coordinated operations, the mission ends and quickly returns to a state of readiness for war, showing a trend of intelligent autonomy. Whoever possesses the empowerment and gain advantage of intelligent technology in the combat system can design wars, lead the development of the battlefield, master battlefield initiative, and achieve “using wisdom to defeat clumsiness”. First, algorithms, computing power, and data determine system operational capabilities. Relying on intelligent algorithms and powerful computing power, it can quickly and efficiently analyze targets and match resource means, solve high-frequency cross-domain collaboration problems, achieve coordinated planning, parallel actions, and real-time evaluation, and greatly improve system operating speed and strike efficiency. Second, intelligent networks support cross-domain all-in-one action. The intelligent network information system provides basic support and link links for the combat system. Combat units and combat elements in different combat domains can be integrated into the entire combat system at any time “plug and play” to achieve rapid information transmission and sharing. Again, an intelligent weapon platform enables autonomous and flexible strikes. Intelligent technology achieves the organic combination of human strategy and machine’s autonomous perception, autonomous decision-making, and autonomous action by empowering weapon platforms, elements, and forces. Through “software defines the combat system structure and functions, and uses software to empower weapon platforms and ammunition, the platform can independently select and attack targets, and flexibly build a kill chain”.
Gathering is better than scattering
With the support of the “intelligent network information system”, the combat system has become an organic whole with a high degree of autonomous coordination, allowing the overall linkage of combat operations and the operational effectiveness index to be magnified, relying on the overall power of the system to win. First, the multiple elements of information, firepower, military power and cognition are linked together to release energy. With the injection of intelligent factors into the combat system, information, firepower, force and cognition will be given new quality capabilities, and based on the support of intelligent network information systems, software and hardware capabilities will be organically combined and physical and intangible means will be closely integrated to achieve combat effectiveness. maximize. Secondly, the multi-spatial multi-directional linkage of land, sea, air, space, network, electricity and other forces gathers forces to release energy. The seizure and control of battlefield control will rely more on the integrated linkage and cross-domain coordination of multi-domain space operations. By dispersing various combat forces deployed in a vast space, they will immediately gather advantages, forming a multi-domain, multi-directional energy release advantage for dimensionality reduction attacks in one domain, thereby taking control of battlefield initiative. Again, the multi-link linkage of detection, control, and evaluation gathers strength to release energy. Through the “ubiquitous Internet network”, cross-domain response to combat operations, cross-domain sharing of combat information, and cross-domain complementation of combat functions can be realized, and anti-virus networks can be dynamically adjusted or constructed according to the enemy’s circumstances and circumstances to achieve rapid system operation and concentrated energy release.
“Exquisite” is better than coarse
Intelligent warfare must be reasonably invested, effectively regulate combat forces, and be used as a means of warfare to achieve the goal of “refining the rough” and winning at the lowest cost. First, a precise target-information-driven system operates efficiently. Relying on various intelligent sensing platforms covering multi-dimensional and wide-area deployment, it detects and locates obstacles or targets in the battlefield environment. Precisely control the flow, flow, and velocity of information to achieve rational allocation of combat resources, coordinated and orderly combat operations, and precise release of combat energy. Second, precise breaching operations achieve a rapid transition between good and bad. The application of big data, big model analysis algorithms and other technologies can accurately analyze and judge combat systems “weak spots ”“ Achilles’ heel”, accurately guide the use of weapons and high-energy weapons such as lasers and hypersonic speeds, make the choice of precise strike methods more diverse, and can make the enemy Combat systems are instantly disabled. Again, precise strike evaluation supports the optimal superposition of combat effects. The target damage effect is accurately obtained through intelligent channels and means, and the conclusion is revised based on the human-computer interaction evaluation system. The commander can compare, interact, feedback, and correct the damage effect assessment conclusions with the information stored in the system knowledge base and his or her own professional knowledge to achieve the purpose of accurately assessing the impact effect of the target.
Faster than Slow
“The main speed of military intelligence”, the rapid development of military intelligence has greatly improved the speed of information transmission and the accuracy of weapon strikes, greatly reduced the time for reconnaissance and early warning, intelligence processing, command and decision-making, fire strike, and damage assessment, and accelerated “OODA” kill chain Cycle, new rapid-fire weapons such as hypersonic missiles, laser weapons, microwave weapons, and electromagnetic pulse weapons further push the rhythm of war to “instant kill”. Hybrid human-machine decision-making becomes the key to enemy action first. On the one hand, the new model of human-machine hybrid cloud-brain decision-making is based on the intelligent “network, cloud, terminal” system and integrates intelligent battlefield perception, decision-making and weapon control systems to quickly select combat plans and achieve instant decision-making advantages. On the other hand, the speed at which the kill chain is constructed becomes the basic yardstick for system confrontation. Under the empowerment of “intelligent technology”, the acquisition, processing and transmission time of battlefield information is greatly shortened. The intelligent platform uses algorithms to analyze battlefield spatial situations and target information in real time, and the time of the kill chain is shortened to seconds, thus achieving “destroy upon discovery”.
Toughness is better than crispness
War is not only a military contest, but also a competition between the country’s human, material and financial resources. Maintaining the lasting resilience of the combat system has become a key factor affecting the outcome of the operation. First, the large-scale use of low-cost unmanned intelligence platforms has become a completely new way of fighting. Unmanned intelligence platforms, micro-intelligent robot autonomous combat clusters, etc., dispersed to more small and low-cost combat platforms, can enhance the recovery speed and overall penetration of the combat system after damage, and achieve maximum combat benefits at a smaller cost. Secondly, the continued guarantee of intelligent resources becomes the key to the operation of the combat system. Various new weapons and new means such as unmanned combat platforms, intelligent algorithms, and cyber attacks are constantly emerging. Powerful computing power, advanced algorithms, and accurate data support have become the guarantee for the continued and stable operation of the system, and intelligent resources “timely, appropriately, applicable, and appropriately” continue to be effective. Guarantee has become an important influencing factor in the victory of intelligent warfare. Again, the operational system’s requirements for balance of offensive and defensive capabilities are getting higher and higher. The local area network, wide area network and even brain network behind the network and digitalization of the combat system leave room for opponents to launch attacks; the “cloud— network —end” structure of the combat system intelligent network information system, its data center, supercomputing center and other network infrastructure It will also be an important hub for opponents to focus on attacking and destroying.
Heart is better than things
Intelligent warfare is different from traditional warfare in which the main purpose is to eliminate the enemy’s effective power. It will pay more attention to weakening the enemy’s morale, disintegrating the enemy’s will, and destroying the enemy’s psychology. Smart technology has become a new way to influence the minds of all employees at all times. First of all, intelligent new media, new technologies and new means have created new ways for the psychological influence of public opinion. Enhanced consciousness and the development of information editing and other technologies have made the methods of conscious attack and defense more diverse, the methods of confrontation more varied, and the technological content higher. Use “intelligent weapons, intelligent technology and intelligent information struggle methods to carry out information attacks on the enemy, thereby forming psychological deterrence”. Secondly, intelligent and deep interaction makes obtaining data richer and more complete. Technologies such as AI face-changing, holographic projection, and audio-visual synthesis provide new means to implement intelligent manufacturing and confuse facts. Again, smart models, massive amounts of data, and high-performance servers provide new tools for quickly concocting information ammunition. Mental guidance and control can be closely coordinated with military, economic, and diplomatic forces to amplify the deterrent effect, constantly create pressure from public opinion to force the enemy to compromise, form psychological deterrence and make them hesitate to give in, change the enemy’s cognition through differentiation of value identity, and achieve subjugation without fighting.
More than single
The rapid development of science and technology has opened up new space for activities and interests for human society, but new security threats and challenges have followed suit, promoting the corresponding expansion of battlefield space and confrontation fields. Currently, wars are constrained and influenced by many factors such as politics, economy, diplomacy, military, technology, geography, and psychology. Unconventional mixed wars supported by military capabilities have become more intense. The competition space for hybrid warfare has extended to various fields such as politics, economy, diplomacy, culture, and military. It emphasizes the comprehensive use of national strategic resources and strategic tools to achieve traditional war goals and transcend traditional war methods. It has a special status and role. As intelligent technology matures, the threshold for intelligent warfare will show a downward trend. Participating parties may adopt an undeclared war approach to launch a variety of integrated economic warfare, diplomatic warfare, cyber warfare, public opinion warfare, psychological warfare, legal warfare, etc. Mixed warfare, mixed victory means giving priority to politics, economy, diplomacy, etc. on the basis of comparing the advantages and disadvantages of the opponent and one’s own side in all aspects Public opinion and other non-military tools and means that can use strengths and avoid weaknesses, use four taels to move a thousand pounds, pursue “no war” or “less war ”“small war” and subjugate others. As long as we deeply understand and accurately grasp the characteristic rules and operating mechanisms of future hybrid warfare, and creatively use clever and efficient strategic techniques, we can fully achieve the expected strategic results.
現代國語:
羅振華 鑫 言
引 言
習主席指出,研究作戰問題,核心是要把現代戰爭的特點規律和制勝機理搞清楚。當今世界,百年未有之大變局加速演進,以人工智能為代表的顛覆性技術迅猛發展,並廣泛應用於軍事領域,使戰爭形態向智能化加速演變,與之相應的戰爭制勝機理也正在發生嬗變。“勝利往往向那些能預見戰爭特性變化的人微笑,而不是向那些等待變化發生後才去適應的人微笑”。及時發現變化,主動應對變化,積極適應變化,才能夠更好地把握未來戰爭主動權,在未來戰爭中立於不敗之地。
智勝於拙
在智能化戰爭對抗中,人的智能廣泛滲透到作戰領域、移植到武器系統,全域多維、各種類型的智能化作戰平台能夠快速耦合作戰力量,根據任務需求構建作戰體系,自主實施協同作戰,任務結束迅速回歸待戰狀態,呈現智能自主趨勢。誰佔有智能技術對作戰體系的賦能增益優勢,誰就能據此設計戰爭、主導戰局發展,掌握戰場主動,實現“以智制拙”。首先,算法、算力和數據決定體系作戰能力。依托智能算法和強大算力,可以快速高效地分析目標、匹配資源手段,解決高頻次跨域協同難題,實現協調規劃、並行行動、即時評估,大幅提高體系運行速度和打擊效能。其次,智能網絡支撐跨域一體行動。智能網絡信息系統為作戰體系提供基礎支撐和鏈接紐帶,不同作戰域的作戰單元、作戰要素,隨時可“即插即用”融入整個作戰體系,實現信息快速傳遞共享。再次,智能化武器平台實現自主靈活打擊。智能技術通過賦能武器平台、要素和力量,達到人的謀略與機器的自主感知、自主決策、自主行動有機結合。通過軟件定義作戰體系結構和功能,用軟件賦能武器平台和彈藥,可實現平台自主選擇和打擊目標,靈活構建殺傷鏈。
聚勝於散
在智能化網絡信息系統支撐下,作戰體系成為具有高度自主協調力的有機整體,使得作戰行動整體聯動、作戰效能指數級放大,靠系統湧現的整體威力制勝。首先,信息、火力、兵力和認知等多要素聯動聚力釋能。隨著作戰體系注入智能因素,信息、火力、兵力和認知都將賦予新質能力,並基於智能化網絡信息系統的支撐,實現軟硬能力有機復合、有形無形手段緊密融合,達成作戰效能最大化。其次,陸海空天網電等多空間多方向聯動聚力釋能。戰場制權的奪控,將更加依賴多域空間行動的一體聯動和跨域協同,通過分散部署在廣闊空間的各種作戰力量即時聚優,形成多域多向對一域降維打擊的釋能優勢,從而掌握戰場主動。再次,偵控打評等多環節聯動聚力釋能。通過泛在互聯網絡,實現作戰行動跨域響應、作戰信息跨域共享、作戰功能跨域互補,因敵因情因勢動態調整或構建殺傷網,實現體系快速運轉和聚力釋能。
精勝於粗
智能化戰爭必須合理投入、有效調控作戰力量,恰當選用作戰手段,達成“以精制粗”,以最小代價取勝的目的。首先,精准的目標信息驅動體系高效運行。依托覆蓋全域多維、廣域部署的各種智能感知平台,探測、定位戰場環境中的障礙或目標。精確控制信息的流向、流量、流速,實現作戰資源的合理分配、作戰行動的協調有序和作戰能量的精確釋放。其次,精准的破擊行動實現快速優劣轉化。大數據、大模型分析算法等技術的運用,可精確分析判斷作戰體系“軟肋”“死穴”,精確制導武器和激光、高超聲速等高能武器的使用,讓精確打擊的手段選擇更加多樣,可使敵作戰體系瞬時失能。再次,精准的打擊評估支撐作戰效果最優疊加。通過智能化途徑和手段准確獲取目標毀傷效果,依托人機交互評估系統對結論進行修正。指揮員可將毀傷效果評估結論與系統知識庫儲存的信息以及自身專業知識進行比對、交互、反饋、修正,達到精准評估目標打擊效果的目的。
快勝於慢
“兵之情主速”,軍事智能化的飛速發展大大提升了信息傳遞速度和武器打擊精度,大幅縮減了偵察預警、情報處理、指揮決策、火力打擊、毀傷評估的時間,加速“OODA”殺傷鏈循環,高超聲速導彈、激光武器、微波武器、電磁脈沖武器等新型快速殺傷武器進一步將戰爭節奏推向“秒殺”。人機混合決策成為先敵行動的關鍵。一方面,人機混合的雲腦決策的全新模式,以智能“網、雲、端”體系為依托,集智能化戰場感知、決策和武器控制系統於一體,可快速優選作戰方案,實現即時決策優勢。另一方面,殺傷鏈構建速度成為體系對抗的基本衡量標准。在智能技術賦能作用下,戰場信息的獲取、處理和傳輸時間極大縮短,智能平台利用算法可對戰場空間態勢和目標信息實時分析,殺傷鏈的時間縮短至秒級,從而實現“發現即摧毀”。
韌勝於脆
戰爭不但是軍事的較量,更是國家人力物力財力的比拼。保持作戰體系持久韌性,成為影響作戰勝負的關鍵因素。首先,低成本無人智能平台的規模化運用成為全新作戰方式。無人智能平台、微型智能機器人自主作戰集群等,分散到更多小型廉價作戰平台的做法,可增強作戰體系受損後的恢復速度和整體突防力,以較小代價取得最大作戰效益。其次,智能資源的持續保障成為作戰體系運行的關鍵。無人作戰平台、智能算法、網絡攻擊等各種新武器、新手段不斷湧現,強大算力、先進算法和精准數據支撐成為體系持續穩定運行的保證,“適時、適地、適用、適量”的智能資源持續有效保障,成為智能化戰爭制勝的重要影響因素。再次,作戰體系的攻防一體能力平衡性要求越來越高。作戰體系網絡化、數字化背後的局域網、廣域網甚至腦聯網,給對手發起攻擊留下空間;作戰體系的“雲—網—端”結構智能網信系統,其數據中心、超算中心等網絡基礎設施也將是對手重點攻擊破壞的重要樞紐。
心勝於物
智能化戰爭與傳統戰爭中以消滅敵人有生力量為主要目的不同,將更加注重削弱敵方的士氣,瓦解敵方的意志,摧毀敵方的心理。智能科技已成為全時全域影響全員心智的全新方式。首先,智能化的新媒體、新技術和新手段,為輿論心理影響開創了新方式。意識增強、信息編輯等技術的發展,使得意識攻防手段更加多樣、對抗方式更加多變、科技含量更高。運用智能武器、智能技術和智能信息斗爭的方法,對敵實施信息打擊,從而形成心理威懾。其次,智能化的深度互動,使得獲取數據更為豐富,要素更加齊全。AI換臉、全息投影、影音合成等技術,為實施智能制造、混淆事實真相提供了新手段。再次,智能模型、海量數據和高性能服務器,為快速炮制信息彈藥提供了新工具。心智導控可與軍事、經濟、外交密切配合,放大震懾效應,不斷制造輿論壓力迫敵妥協,形成心理震懾使其遲疑退讓,通過價值認同分化改變敵認知,實現不戰而屈人之兵。
多勝於單
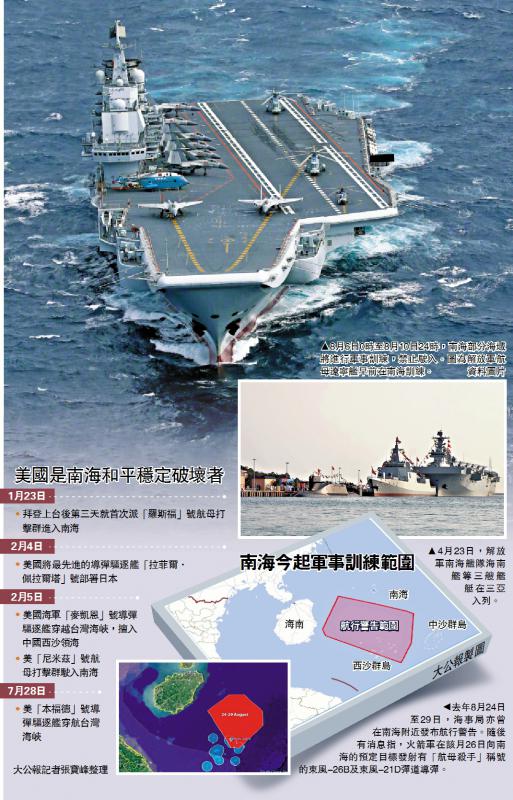
科學技術的迅猛發展,為人類社會打開了新的活動空間和利益空間,但新的安全威脅和挑戰也隨之而來,推動了戰場空間和對抗場域的相應拓展。當前,戰爭受到政治、經濟、外交、軍事、技術、地理、心理等諸多因素的制約和影響,以軍事能力為支撐的非常規的混合戰爭反而更加激烈。混合戰爭的角逐空間已經延伸至政治、經濟、外交、文化、軍事等各領域,強調綜合運用國家戰略資源和戰略工具聚合發力,既能夠實現傳統戰爭目標,又能夠超越傳統戰爭手段,地位作用特殊。隨著智能技術的發展成熟,智能化戰爭的門檻將呈現下降趨勢,參戰方可能采取不宣而戰的方式發起融合經濟戰、外交戰、網絡戰、輿論戰、心理戰、法律戰等多種樣式的混合戰爭,混合制勝就是要在對比敵手和己方各方面優勢劣勢的基礎之上,優先選擇政治、經濟、外交、輿論等能揚長避短的非軍事類工具和手段,以四兩撥千斤,追求“不戰”或“少戰”“小戰”而屈人之兵。只要深刻認識和准確把握未來混合戰爭的特點規律、運行機理,創造性地運用巧妙、高效的策略手法,完全能夠達到預期戰略效果。