Chinese General: If hostile forces invade my network sovereignty China can use military means to fight & hack back //
中國將軍:如果敵對勢力入侵我的網絡主權,中國可以用軍事手段進行反擊和反擊
(安卫平,北部战区副参谋长)
Original: “National Defense Reference”, No. 3, 2017
The cyberspace was born in the military field. For example, the first computer, the APA network and the GPS navigation system all originated from the military. Today, cyberspace security has been closely related to national security, and the military has once again become the protagonist of maintaining national cyberspace security. Whether facing normalized network penetration or large-scale cyberattacks, it is urgent for the military to move from guarding the “network camp gate” to guarding the “network country gate”, breaking through the traditional military missions and missions, and breaking through the traditional war preparation mode. With a new network of national defense thinking, the founding of the network era of the country’s strong shield.
From the “network camp door” to the “network country door”, the new era brings a new trend of military mission
Cyberspace is not only related to the maintenance of national strategic interests, but also directly affects political, economic, cultural security and social development. It has also become the blood and link of modern battlefield joint operations. The Chinese military cannot be limited to maintaining the internal network security of the military camp. It must also actively adapt to the trend of the times and take the responsibility of the country that guards the “network country.” Network strong army is an important part of the construction of a network powerhouse. From the “network camp door” to the “network country door” is the inevitable trend of the development of the domestic and international situation in the information age.
Guarding the “network country door” is forced by the cyberspace security situation. As the first big Internet country, China’s security situation is not optimistic, and strategic opponents have never stopped preparing for our network operations. The United States, Britain, France and other countries are actively preparing for cyberspace, giving military functions through cyberspace security legislation, developing cyber warfare forces, developing cyber warfare weapons and equipment, and advancing war to the “fifth space” of mankind, especially in China. In the historical process of the rise, under the leadership of the Cold War mentality and the containment subversion strategy, Western countries have used network technology and communication methods to implement uninterrupted harassment, subversion and cyberattacks, seriously affecting China’s national security and social development, and China has gradually become The hardest hit by cybersecurity threats, the test sites for virus attacks, and the destinations of conscious penetration, national security faces enormous risks.
In the coming period, as a new emerging country, China’s conflicts of interest with other parties will intensify. Firmly promoting the network defense strategy and strengthening the operational preparation of cyberspace are the inevitable ways to actively strive for the dominance and discourse power of cyberspace, and also the rise of China. The only way to go. As the main force of national security and stability, the military must adapt to the characteristics of cyberspace characteristics, become the backbone and main force to resist network intrusion and network subversion, and safeguard national security and social stability.
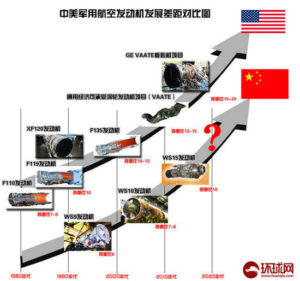
Winning cyber warfare is the trend of new military revolution in the information age. As one of the most advanced productivity in the information age, network technology has made cyberspace warfare a leading factor in guiding the evolution of modern warfare and affecting the overall situation of war. In recent years, from the “seismic net” attack in Iran, the cyber warfare in the Russian-Georgian conflict, the large-scale obstruction of the Ukrainian power grid, and the cyberattack of the US military against IS, the huge role played by cyberspace in actual combat has gradually emerged, indicating that cyber warfare Has become an important style of future joint operations.
The US military attaches great importance to the construction of cyberspace armaments, the establishment of the cyberspace command, the launch of cyberspace joint operations, the extensive expansion of cyber warfare forces, the maintenance of its cyberspace hegemony, and the formation of cyberspace control capabilities as a “third offset strategy”. “Absolute advantage is the most important competitive content.
Many countries in the world have followed suit, and the trend of militarization of cyberspace is obvious. The rigorous cyberspace military struggle situation requires the Chinese military to focus on the changes in the network battlefield space, adapt to the requirements of the information war era, and achieve the strong military goal of smashing and winning in cyberspace.
Effective network warfare is an intrinsic need to accelerate the construction of a network powerhouse. In the process of China’s development from a network power to a network power, it is inseparable from the strong cyberspace military power as a guarantee. The international competition in cyberspace is a comprehensive game of the country’s comprehensive strength. Among them, the quality of network military capacity building is directly related to national security and stability, and it is the core element of the entire national security field.
At present, the interests of countries in the world in the cyberspace are mutually infiltrated, and there is a situation in which you have me, I have you, cooperate with each other, and develop together. However, this kind of common development is not equal. The US and Western powers have taken advantage of the cyberspace dominance and have already achieved certain network warfare advantages, which has made my network development and interests subject to people. How can the military fulfill its mission of defending the earth in the construction of a network-strength country? The premise is to form a network environment that can contain the crisis and control the opponent’s network attack and defense capabilities and ensure peaceful development.
Therefore, the military needs to establish a deterrent strategic goal of effective warfare, form a strategic check and balance ability that can “destroy each other” with the enemy, thereby enhancing strategic competitiveness, ending cyberspace aggression, and ensuring the smooth advancement of the network power strategy.
From “keeping the soil to the responsibility” to “protecting the net and defending the country”, the new situation requires the military to undertake new tasks.
The military is the main force and pillar of national security, and cyberspace is no exception. The National Security Law, which was enacted on July 1, 2015, stipulates: “Citizens of the People’s Republic of China, all state organs and armed forces, political parties and people’s organizations, enterprises and institutions, and other social organizations have the responsibility to safeguard national security. And obligations.” The Cyber Security Law, promulgated in November 2016, emphasizes the need to maintain cyberspace sovereignty and national security.
On the basis of the laws of these two countries, on December 27, 2016, the National Cyberspace Security Strategy (hereinafter referred to as the “Strategy”) was officially launched, providing overall guidance for creating a new pattern of network powers at a new starting point. Basically follow, clearly put forward nine strategic tasks, further embodying the mission of the military in the process of building a network power.
With the national mission of protecting the network, the military must be a strong pillar to defend the cyberspace sovereignty. The first of the nine strategic tasks listed in the “Strategy” is “firmly defending the cyberspace sovereignty” and clearly proposes to “take all measures including economic, administrative, scientific, technological, legal, diplomatic, military, etc., and unswervingly maintain our network.” Space sovereignty.” It can be seen that the military must assume the military mission of using physical space and defend the national mission of the sovereign security and interests of virtual cyberspace.
Cyberspace sovereignty is the core interest of the state and an important component of national sovereignty. It indicates the independence, equal, self-defense and management power of the state in cyberspace. Once the hostile forces violated my cyberspace sovereignty, it would be equivalent to infringing on the national sovereignty of the physical space such as land, sea and air. China will have the right to take all measures including military means to give a firm response.
Internationally, the United States has long proposed a cyberspace deterrence strategy, declaring that attacks on US network information facilities are equivalent to war acts, and the United States will take military strikes to retaliate. Military means are the means of safeguarding national sovereignty and play a vital role in safeguarding national cyberspace security. Therefore, the military, air, sea and air military forces have been given the historical mission of protecting the cyberspace sovereignty. They must rely on the powerful physical space to defend the national interests of cyberspace and effectively deter the hostile forces from cyber-damaging attempts.
In accordance with the era of the Internet, the military must be the ballast stone to defend national security. The second item of the “Strategy” mission emphasizes the need to resolutely safeguard national security, prevent, deter and punish any use of the Internet for treason, secession, sedition, subversion or incitement to subvert the people’s democratic dictatorship.
In the era of information network, the military of all countries in the world has become an important participant in cyberspace. The level of cyberspace capability has become the main indicator for assessing the modernization of a country’s military. It is one of the main duties of the informationized military to carry out cyberspace missions and maintain national security.
Judging from the historical process of China’s development, it is necessary to be highly vigilant against the danger of the country being invaded, subverted, and divided in cyberspace in order to adapt to the national security strategy needs of building a well-off society in an all-round way. Highly alert to the reform caused by cyberspace. The danger of developing the overall situation is destroyed, and we are highly wary of the danger of interference and destruction in the development of socialism with Chinese characteristics.
Preventing problems before they occur requires the state to have the means to cope with and deal with these risks, and to have the powerful force to prevent, stop and legally punish cyberspace violations. Defending the country has always been an unshirkable historical responsibility of the military. The inherent mission and mission have determined that the Chinese military must assume the role of taking various measures in the cyberspace to safeguard the country’s political, economic, cultural security and social stability.
The strategic mission of both offensive and defensive, the military must be a strong backing to enhance the ability of cyberspace protection. The third and eighth items of the Nine Major Tasks in the Strategy clearly state that all necessary measures must be taken to protect key information infrastructure and its important data from attack and destruction, and that technology and management should be adhered to, protected and shocked; We will build a network space protection force that is commensurate with China’s international status and adapts to the network power. We will vigorously develop network security defense methods, timely discover and resist network intrusion, and build a strong backing for national security. Among all the political, diplomatic, military, and scientific and technological capabilities of the country to maintain security, military power has always been the foundation and support for all capabilities, the fundamental guarantee for all capabilities, and the ultimate support for national security.
Therefore, the military must undertake the strategic task of strengthening the national cyberspace protection capability. In the real society, the military is the reassurance of safeguarding national security, and it should also become the security dependence and guarantee of the people in cyberspace. As an important part of the national cyberspace protection capability, the military must achieve both offensive and defensive capabilities and a unified warfare. It has the ability to resolutely safeguard the interests and security of the country and the people in cyberspace, and effectively eliminate the various crises caused by cybersecurity threats. The turbulence of thoughts enables the people to truly feel that production and life are effectively protected and become the confidence of the people of the whole country in their confidence in the national network protection capabilities.
With the global responsibility of UNPROFOR, the military must be an important support for maintaining global cybersecurity. The last item of the “Strategy” mission clearly proposes to strengthen international cooperation in cyberspace, support the United Nations in playing a leading role, promote the development of universally accepted international rules on cyberspace, international anti-terrorism conventions on cyberspace, and improve the judicial assistance mechanism against cybercrime. International cooperation in the areas of policy and law, technological innovation, standards and regulations, emergency response, and protection of key information infrastructure.
Cyber terrorism and cybercrime are new forms of global threat catalyzed by information network fermentation. They pose a huge threat to the political, economic, military and cultural security of all countries in the world. It is not enough to rely solely on the power of the government and the people. Western countries have given the military the responsibility to protect cybersecurity and the power to fight cyber terrorism. Maintaining the security and stability of global cyberspace is in the fundamental interests of China and the rest of the world. The military should become an important defender of global cyberspace security and an important force in combating global cyber terrorism and cybercrime.
The globalization and unbounded nature of the Internet determine the international demand for combating cyber terrorism and transnational cybercrime. The military should promote military cooperation in network governance between countries under the framework of the UN Security Council, and use the strategies and technologies of the network era to establish joint defense and joint defense. Mechanism to effectively safeguard the security of the national and world cyberspace.
From “field training” to “network preparation”, new areas require new preparations for the military
Under the new historical situation, cyberspace puts forward new requirements for the military training and preparation mode. It should adapt to the new characteristics of cyberspace and the new mission of the military to carry out innovative reforms on the traditional model, and take the goal of strengthening the country and strengthening the military as the overall plan, and strengthen macro-coordination. Focusing on the legal needs of military operations in cyberspace, it closely follows the natural attributes of the “military and civilian integration” of cyberspace, builds a network security attack and defense system that combines peacetime and warfare, and builds a network defense force of “military and land use”.
Legislation empowerment provides a legal basis for the military to carry out its functional mission. The countries of the world, especially the western developed countries, attach great importance to the issue of network defense in cyber security legislation. The United States has successively issued a series of policies and regulations such as “National Security No. 16 Presidential Decree”, “Network Space Action Strategy”, and has continuously deepened and standardized on how to protect national network security in the field of network defense.
At present, it is necessary to clarify the duties and responsibilities of the cyberspace military from the legal level. It should be based on the National Security Law and the Cyber Security Law, and introduce the network defense law and related cyberspace military operational regulations, for the construction of the network defense field and the military. The action provides regulatory support and a program of action to make the military’s responsibilities and mission in cyberspace more specific and specific.
First, through network defense legislation to further define network sovereignty and network frontiers, clear the scope of the military’s responsibilities.
The second is to establish the operational authority of the military to defend the national cyberspace security through the construction of cyber warfare laws and regulations, and to distinguish military means against network intrusion and network destruction. Third, through the cyberspace international cooperation policy, the military will coordinate with other countries and civilian forces to combat international cyber terrorism and cybercrime.
The integration of military and civilian provides an innovative driving force for the construction of a network powerhouse. The integration of military and civilian is the main practice for the world powers to enhance the competitiveness of cyberspace. For the construction of China’s network powerhouses, building a military-civilian network security attack and defense system and developing a military-land dual-use defense information infrastructure is to inspire the innovation of military cyberspace combat capability. Source.
The first is to coordinate the military, civilian, and functional departments of the state, the military, and various levels of government, set up special command and coordination agencies, mobilize all national network forces, and build a network security attack and defense system that combines “military and civilian integration” and “peace and war.”
The second is to issue guidance on the in-depth development of cybersecurity military-civilian integration as soon as possible, and gradually carry out basic legal research and demonstration of military-civilian integration to guide the development of medium- and long-term military-civil integration.
Third, relying on the country’s existing public mobile communication network, optical fiber communication network and satellite system, the military and civilians will jointly build an information infrastructure covering the entire army of the whole country, and realize the unified construction and sharing of military and civilian.
The fourth is to establish an emergency response mechanism for military-civilian joints, increase the ability to train military authorities to control events, strengthen experts and emergency professional strength, and enhance the ability to quickly recover damaged networks or information systems.
Military-civilian joint training provides a practical environment for the generation of cyberspace military capabilities. The military-civilian sharing characteristics of cyberspace make military-civilian joint training an important means of military training in cyberspace around the world. The United States and NATO countries and other cyberspace joint military and civilian exercises have formed a series of, “network storm” and “network guards” and other exercises have attracted the participation of the government, enterprises, research institutions and even civilian hackers. Our military cyberspace military strength training also needs to attract a wide range of civil forces to participate.
First, do a good job in military and political cooperation, establish a military-civilian joint offensive and defensive drill mechanism, learn from the red-blue confrontation training methods in cyber warfare drills in developed countries such as the United States, actively build a “national network shooting range”, plan a series of joint exercises of the government and non-government organizations, and enhance the integration of military and civilian. The level of attack and defense of the network of the government and the people.
The second is to do a good job in military-enterprise cooperation, relying on net-based enterprises to set up a training field on the Internet, to promote the ability of the military and civilians to attack and defend, and jointly improve the ability to prevent unknown risks.
The third is to organize private network security companies and hacker talents, carry out network security competitions and other activities, and verify each other to jointly improve the level of network security protection technology and tactics.
The network reserve service provides a source of strength for building a powerful network army. As a backup supplement to the national defense force, reserve service has both military and civilian characteristics and is a powerful measure to realize the organic unification of cyberspace economic development and national defense construction.
First, it is led by the national security department, and overall planning is carried out according to national interests. A series of laws and regulations conducive to the construction of the network national defense reserve are introduced. From the top level, the main division of labor, promotion strategy, interest coordination, etc. of the military and civilian construction in the network defense reserve construction are solved. problem.
The second is to innovate the reserve organization and comprehensive coordination mechanism, and plan to integrate the reserve construction into all levels and fields of national network information development.
The third is to focus on the reform of the military and local management modes. Based on the management mechanisms of the provincial and municipal governments, the military, and local enterprises and institutions, establish a network of national defense reserve personnel to jointly cultivate and use the mechanism, improve the national emergency mobilization mechanism, and establish a national network defense special talent. The database will include the construction of network militia and reserve forces into the scope of mobilization of the people’s armed forces. In normal times, they will be incorporated into the militia emergency detachment for training. In an emergency, select the capable personnel to participate in the non-war military operations missions, and the wartime will be recruited according to the requirements. To transform the national defense potential into national defense strength.
Original Mandarin Chinese:
原載:《國防參考》2017年第3期
網絡空間誕生於軍事領域,如首台計算機、阿帕網和GPS導航系統等都源於軍方,時至今日,網絡空間安全已與國家安全息息相關,軍隊又再次成為維護國家網絡空間安全的主角,無論是面對常態化的網絡滲透,還是大規模的網絡攻擊,都迫切需要軍隊從守衛“網絡營門”走向守衛“網絡國門”,突破傳統的軍隊使命任務,突破傳統的應戰備戰模式,以全新的網絡國防思維,鑄造網絡時代國之堅盾。
從“網絡營門”到“網絡國門”,新時代帶來軍隊使命新趨勢
網絡空間不僅事關國家戰略利益維護,直接影響政治、經濟、文化安全和社會發展,也成為現代戰場聯合作戰的血脈和紐帶。中國軍隊不能局限於維護軍營內部網絡安全,更要主動適應時代趨勢,勇於承擔把守“網絡國門”的國家擔當。網絡強軍是網絡強國建設的重要一環,從“網絡營門”走向“網絡國門”是信息時代國內外形勢發展的必然趨勢。
守衛“網絡國門”是網絡空間安全形勢所迫。中國作為第一網絡大國,安全狀況不容樂觀,戰略對手從未停止對我網絡作戰準備。美、英、法等國積極備戰網絡空間,通過網絡空間安全立法賦予軍隊職能,發展網絡戰部隊,研發網絡戰武器裝備,將戰爭推進到了人類的“第五空間”,特別是在中國日益強大崛起的歷史進程中,西方國家在冷戰思維和遏制顛覆戰略的主導下,利用網絡技術手段和傳播方式實施不間斷的騷擾、顛覆和網絡攻擊行動,嚴重影響我國家安全與社會發展,中國逐漸成為網絡安全威脅的重災區、病毒攻擊的試驗場、意識滲透的目的地,國家安全面臨著巨大風險。
未來一段時期內,中國作為新興大國,與各方利益衝突還將加劇,堅定推進網絡國防戰略,加強網絡空間的作戰準備,是積極爭取網絡空間的主導權和話語權的必然途徑,也是中國崛起的必由之路。軍隊作為國家安全穩定的主要力量,必須適應網絡空間特點要求,成為抗擊網絡入侵、網絡顛覆的中堅和主力,維護國家安全和社會穩定。
打贏網絡戰爭是信息時代新軍事變革所趨。網絡技術作為信息時代最先進生產力之一,使得網絡空間作戰成為引導現代戰爭形態演變的主導因素,影響著戰爭全局。近年來,從伊朗“震網”攻擊、俄格衝突網絡戰、烏克蘭電網遭大規模阻癱以及美軍對IS的網絡攻擊,網絡空間在實戰中所展現出的巨大作用逐漸顯現,預示著網絡作戰已成為未來聯合作戰重要樣式。
美軍高度重視網絡空間軍備建設,成立網絡空間司令部,推出網絡空間聯合作戰條令,大幅度擴編網絡戰部隊,極力維護其在網絡空間霸權,把對網絡空間控制能力作為形成“第三次抵消戰略”絕對優勢最重要的競爭內容。
世界多國紛紛跟進,網絡空間軍事化趨勢明顯。嚴峻的網絡空間軍事鬥爭形勢要求中國軍隊著眼網絡戰場空間變化,適應信息化戰爭時代要求,實現在網絡空間能打仗、打勝仗的強軍目標。
有效網絡懾戰是加速網絡強國建設內在所需。在中國由網絡大國向網絡強國發展過程中,離不開強大的網絡空間軍事力量作為保障。網絡空間國際競爭表現為國家綜合實力的全面博弈,其中,網絡軍事能力建設的好壞,直接關係到國家安全與穩定,牽一發而動全身,是整個國家安全領域的核心要素。
當前,世界各國在網絡空間的利益互相滲透,出現“你中有我、我中有你,互相合作,共同發展”的局面。但是這種共同發展是不對等的,美國及西方強國利用網絡空間主導權,已經取得了一定的網絡懾戰優勢,使我網絡發展及利益受制於人。軍隊如何在網絡強國建設中完成守土有責的使命重托,前提就是要形成能夠遏制危機、懾控對手的網絡攻防能力,確保和平發展的網絡環境。
因此,軍隊需要確立有效懾戰的威懾戰略目標,形成能與敵“相互摧毀”的戰略制衡能力,從而增強戰略競爭力,懾止網絡空間侵略,保障網絡強國戰略順利推進。
從“守土有責”到“護網衛國”,新形勢要求軍隊承擔新任務
軍隊是保衛國家安全的主力和柱石,網絡空間也不例外。 2015年7月1日施行的《國家安全法》規定:“中華人民共和國公民、一切國家機關和武裝力量、各政黨和各人民團體、企業事業組織和其他社會組織,都有維護國家安全的責任和義務。”2016年11月頒布的《網絡安全法》強調了要維護網絡空間主權和國家安全。
在這兩個國家法律的基礎上,2016年12月27日,《國家網絡空間安全戰略》(下文簡稱《戰略》)正式出台,為在新的起點上開創網絡強國新格局提供了總體指導和基本遵循,明確提出了九大戰略任務,進一步體現了軍隊在建設網絡強國進程中的使命任務。
全力護網的國家使命,軍隊要做捍衛網絡空間主權的堅強柱石。 《戰略》中列出的九大戰略任務首項就是“堅定捍衛網絡空間主權”,明確提出要“採取包括經濟、行政、科技、法律、外交、軍事等一切措施,堅定不移地維護我國網絡空間主權”。可見,軍隊須承擔起運用實體空間的軍事手段,保衛虛擬網絡空間主權安全和利益的國家使命。
網絡空間主權是國家的核心利益,是國家主權的重要組成,表明國家在網絡空間所擁有的獨立權、平等權、自衛權和管理權。一旦敵對勢力侵犯了我網絡空間主權,就等同於侵犯了我陸海空等實體空間的國家主權,中國將有權利採取包括軍事手段在內的一切措施給予堅決回擊。
在國際上,美國早就提出網絡空間威懾戰略,宣告對美國網絡信息設施的攻擊等同於戰爭行為,美國會採取軍事打擊措施進行報復。軍事手段是維護國家主權的保底手段,在維護國家網絡空間安全中發揮著至關重要的作用。因此,陸海空天軍事力量理所應當地被賦予了保護網絡空間主權的歷史使命,必須憑藉強大的實體空間武力保衛網絡空間的國家利益,有力震懾敵對勢力的網絡破壞企圖。
依網衛國的時代擔當,軍隊要做保衛國家安全的壓艙石。 《戰略》任務的第二項著力強調要堅決維護國家安全,防範、制止和依法懲治任何利用網絡進行叛國、分裂國家、煽動叛亂、顛覆或者煽動顛覆人民民主專政政權的行為。
信息網絡時代,世界各國軍隊都已經成為網絡空間重要參與者,網絡空間能力水平成為評估一個國家軍隊現代化程度的主要指標,遂行網絡空間使命任務、維護國家安全成為信息化軍隊的主要職責之一。
從中國發展所處的歷史進程來看,要適應全面建成小康社會決勝階段的國家安全戰略需求,必須高度警惕國家在網絡空間被侵略、被顛覆、被分裂的危險,高度警惕由網絡空間引發改革發展大局被破壞的危險,高度警惕中國特色社會主義發展進程被干擾、破壞的危險。
防患於未然,要求國家必須具有應對和處置這些危險的手段措施,具有防範、制止和依法懲治網絡空間違法破壞行為的強大力量。保衛國家歷來是軍隊不可推卸的歷史責任,固有的使命任務決定了中國軍隊必須承擔起在網絡空間採取各種措施,維護國家政治、經濟、文化安全和社會穩定的時代擔當。
攻防兼備的戰略任務,軍隊要做提升網絡空間防護能力的堅強後盾。 《戰略》中九大任務的第三項和第八項明確提出,要採取一切必要措施保護關鍵信息基礎設施及其重要數據不受攻擊破壞,要堅持技術和管理並重、保護和震懾並舉;要建設與我國國際地位相稱、與網絡強國相適應的網絡空間防護力量,大力發展網絡安全防御手段,及時發現和抵禦網絡入侵,鑄造維護國家網絡安全的堅強後盾。在國家所有維護安全的政治、外交、軍事、科技能力中,軍事力量歷來是所有能力的基礎和支撐,是所有能力的根本保障,是國家安全的最終依托。
因此,軍隊必須承擔起提升國家網絡空間防護能力堅強後盾的戰略任務。現實社會中,軍隊是維護國家安全的定心丸,在網絡空間也同樣應成為人民群眾的安全依賴和保障。軍隊作為國家網絡空間防護能力生成的重要一環,必須做到攻防兼備、懾戰一體,有能力堅決維護國家和人民在網絡空間的利益和安全,能夠有效消除網絡安全威脅造成的各種危機和思想動盪,使人民能夠切實感受到生產生活得到有效保護,成為全國人民對國家網絡防護能力充滿信心的底氣所在。
聯防聯治的全球責任,軍隊要做維護全球網絡安全的重要支撐。 《戰略》任務最後一項明確提出要強化網絡空間國際合作,支持聯合國發揮主導作用,推動制定各方普遍接受的網絡空間國際規則、網絡空間國際反恐公約,健全打擊網絡犯罪司法協助機制,深化在政策法律、技術創新、標準規範、應急響應、關鍵信息基礎設施保護等領域的國際合作。
網絡恐怖主義和網絡犯罪是經過信息網絡發酵催化出的全球威脅新形態,對世界上所有國家的政治、經濟、軍事、文化安全都構成巨大威脅,僅僅依靠政府和民間的力量是不夠的,美國等西方國家紛紛賦予軍隊保護網絡安全的職責和打擊網絡恐怖主義的權限。維護全球網絡空間安全與穩定符合中國以及世界各國的根本利益,軍隊應成為全球網絡空間安全的重要維護者,成為打擊全球網絡恐怖主義和網絡犯罪的重要力量。
網絡的全球化、無界性決定了打擊網絡恐怖主義和跨國網絡犯罪的國際需求,軍隊應在聯合國安理會的框架下,推進國家間網絡治理軍事合作,利用網絡時代的戰略和技術,建立聯防聯治機制,切實維護國家和世界網絡空間安全。
從“沙場練兵”到“網絡備戰”,新領域需要軍隊備戰新舉措
在新的歷史形勢下,網絡空間對軍隊練兵備戰模式提出了全新的要求,應適應網絡空間新特點和軍隊新使命對傳統模式進行創新改革,以強國強軍目標為統攬,加強宏觀統籌,著眼網絡空間軍事行動的法理需求,緊扣網絡空間“軍民一體”的天然屬性,建設“平戰結合”的網絡安全攻防體系,打造“軍地兩用”的網絡國防力量。
立法賦權,為軍隊遂行職能使命提供法理依據。世界各國尤其是西方發達國家在網絡安全立法上高度重視網絡國防問題。美國先後出台了《國家安全第16號總統令》《網絡空間行動戰略》等一系列政策法規,對如何在網絡國防領域保護國家網絡安全進行了不斷的深化規範。
當前,從法律層面釐清網絡空間軍隊的職責任務非常必要,應以《國家安全法》《網絡安全法》為依據,出台網絡國防法和有關網絡空間軍事作戰條令法規,為網絡國防領域建設和軍事行動提供法規支撐和行動綱領,使軍隊在網絡空間的職責和使命更加明確具體。
一是通過網絡國防立法進一步界定網絡主權和網絡邊疆,清晰軍隊的職責範圍。
二是通過網絡作戰法規建設,明確軍隊遂行保衛國家網絡空間安全的行動權限,區分應對網絡入侵、網絡破壞等行為的軍事手段。三是通過網絡空間國際合作政策,明確軍隊協同他國、民間力量等打擊國際網絡恐怖主義、網絡犯罪的職能任務。
軍民融合,為網絡強國建設提供創新動力。軍民融合是世界強國提升網絡空間競爭力的主要做法,對於中國網絡強國建設來說,構建軍民融合網絡安全攻防體系,開發軍地兩用的國防信息基礎設施,是激發軍隊網絡空間作戰能力創新的源泉。
一是統籌國家、軍隊和各級政府等軍民融合職能部門,設置專門的指揮協調機構,調動一切國家網絡力量,建設“軍民一體”“平戰結合”的網絡安全攻防體系。
二是盡快出台網絡安全軍民融合深度發展指導性意見,逐步展開軍民融合基本法律研究論證,指導中長期軍民融合發展。
三是依托國家現有公共移動通信網、光纖通信網及衛星系統,軍民共建覆蓋全國全軍的信息基礎設施,實現軍民統建、分管共享。
四是建立軍民聯合的應急響應機制,加大培訓軍地主管部門控制事態的能力,加強專家和應急專業力量,提升快速恢復受損網絡或信息系統的能力。
軍民聯訓,為網絡空間軍事能力生成提供實戰化環境。網絡空間的軍民共用特性使得軍民聯訓成為世界各國網絡空間軍事演訓的重要方式。美國及北約等國家的網絡空間軍民聯合演習已經形成系列化,“網絡風暴”“網絡衛士”等演練活動吸引了政府、企業、研究機構甚至民間黑客的廣泛參與。我軍網絡空間軍事力量訓練也需要廣泛吸引民間力量參與。
一是搞好軍政合作,建立軍民聯合攻防演練機制,借鑒美國等發達國家網絡戰演練中的紅藍對抗訓練方法,積極建設“國家網絡靶場”,策劃政府、民間機構系列聯合演習,提升軍民一體、官民一體的網絡攻防水平。
二是搞好軍企協作,在互聯網上依靠網信企業設置演練場區,促進軍民之間攻防能力磨合,共同提高防範未知風險能力。
三是組織民間網絡安全公司和黑客人才,開展網絡安全競賽等活動,互相印證,共同提高網絡安全防護技戰術水平。
網絡預備役,為建設強大網軍提供力量源泉。預備役作為國防力量的後備補充,兼有軍事和民用雙重特點,是實現網絡空間經濟發展與國防建設有機統一的有力舉措。
一是以國家安全部門為主導,依據國家利益進行統籌規劃,出台有利於網絡國防預備役建設的系列法規政策,從頂層上解決網絡國防預備役建設中軍民共建的主體分工、推進策略、利益協調等問題。
二是創新預備役組織領導體制和綜合協調機制,有計劃地把預備役建設融入國家網絡信息化發展的各個層面和各個領域。
三是著眼軍隊和地方兩頭管理模式改革,以各省市政府、軍隊和地方企事業單位的管理機制為依托,建立網絡國防預備役人才聯合培養使用機制,完善國家應急動員機制,建立國家網絡防禦專用人才數據庫,將網絡民兵和預備役部隊建設納入人民武裝動員的範圍,平時按規定編入民兵應急分隊進行訓練,急時挑選精干人員隨隊參加遂行非戰爭軍事行動任務,戰時按需要成建制徵召使用,使國防潛力轉變為國防實力。
Referring url: https://military.people.com.cn/n1/2017/0417/c1011-29215670.html