Chinese Military Information Warfare Attacks on Mind and Spirit //
中國軍隊信息戰隊思想和精神的攻擊
| June 01, 2004 08:58 |
| If the 1991 Gulf War was the first time that the United States brought information warfare from the research report to the actual battlefield, then the Iraq war that ended last year may be the further development of information warfare in actual combat. Information warfare, as the focus of the new military revolution in the 21st century, has increasingly attracted people’s attention. However, through the information campaign to study the lively scenes, we will find that quite a few people only understand information warfare from the perspective of military and technology alone, but information warfare is not so simple.
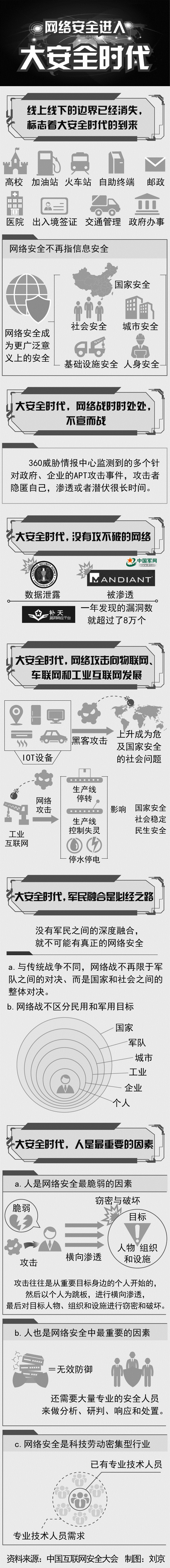
Information warfare is a new emergence of human beings entering the information age. a phenomenon of war. It is not a simple style of warfare, but a new form of warfare relative to firepower. The emergence of information warfare has formed a major breakthrough in many traditional war concepts such as the object of war, the boundaries of war, and the content of war. Among them, the focus should be on the ideological and spiritual side of information warfare. What you see is only the tip of the iceberg . There are dozens of concepts about information warfare in the world. However, many of them only understand information warfare from the military and technical perspectives. Even the United States, which is in the leading position of information warfare, is only from the last It was only at the end of the century that this issue was considered from a strategic and social point of view. This is not comprehensive. An important prerequisite for understanding information warfare is that information warfare should not be viewed simply with the war view of the industrial age. In the information age, computers and networks have dramatically changed the shape of war in the past. In the information war, the army and the society, the military and civilians, the war and the crime, the state and the individual have been intertwined in many cases, and they are unclear and unreasonable. Information warfare broadly refers to the war against the information space and the competition for information resources in the military (including political, economic, cultural, scientific, and social fields). It mainly refers to the use of information to achieve the national strategic goals; narrowly Refers to the confrontation between the warring parties in the armed field in the field of information, and seizes the right to control the information. It should be emphasized that information warfare is not a simple military technical issue and should not be understood as a combat style. Information warfare is actually a form of war. The term “information” is understood relative to the times, and corresponds to the agricultural and industrial eras; in terms of social forms, it is also in line with agricultural and industrial societies. At the same time, it is one of the three major resources that human beings must compare with matter and energy. Investigating information warfare, only by knowing at this level can we reveal information warfare in the true sense. The rise of information warfare lies not in what kind of nouns it uses, nor in the war nouns. It is as simple as the buzzwords of “information,” “information,” “information age,” and “digitalization.” It is the inevitable result of the development of society and science and technology, with revolutionary and epoch-making significance. The information wars that emerged at the end of the 20th century, or the information wars we have seen, are only the tip of the iceberg, and are only partial and limited information wars embodied in the military field. Only when the world reaches full network and the earth becomes a small village in the true sense can we see the broad and real information war. Information warfare is not just about the military. When it comes to information warfare, people often think of the army first. Indeed, in the traditional war, the army is the protagonist of the war, and the battlefield is also the stage of the military. Under the conditions of information warfare, the situation is very different. The scope of the battlefield has greatly expanded, and the war has become far more than just military affairs, but has developed into a national war under high-tech conditions. Information warfare is not only carried out through the military, but also through the entire social network. With the construction of the world information highway, information warfare has been difficult to define boundaries. Any social NGO or even an individual who has ordinary computer equipment and masters computer communication technology may use a globally connected computer and communication system to participate in an information war. The information warfare is not only the main manifestation of the army: First, the participants in the information war are no longer limited to military personnel, but also include ordinary people. Information warfare combatants can be either regular soldiers or teenage hackers. Second, many of the weapons and equipment used in information warfare, such as computers and optical instruments, can no longer be military supplies, and are available in the civilian goods market. Take the United States, an information war powerhouse, as an example. The US military’s information warfare system relies heavily on civilian information infrastructure. Senior US military personnel referred to the informationization of the US military’s military as “buy from the market.” Third, information warfare is not only on the battlefield, but on the entire society. “The battlefield is only where the soldiers are killed. It no longer covers information warfare.” Information warfare is not only played in wartime.
In the Iraq war, the power of public opinion wars opened the eyes of the world. It has been said that the “discussion war”, one of the forms of information warfare, has been going on since the war. Earlier cases of “public opinion wars” can be traced back to the “Oath of the Oath” of China’s Xia Dynasty and later “Looking for Cao Yuwen” and “Discussing Wushu”. The “discussion of public opinion” has no boundaries between wartime and peace. It controls, manipulates, plans, and utilizes various public opinion tools to systematically deliver selected information to the audience, affecting the audience’s emotions, motivations, judgments, and choices, thus having a major and direct impact on the outcome of the war. As for the information warfare and cyber warfare in the information war, it is even more ignoring the difference between wartime and peacetime. At that time, the US Clinton Administration put forward the idea of building an information highway and promoting global informationization. This move has made the world believe that the United States is leading the human society into the information age. However, the strategic intention of the United States is actually that when the informationization of human society is still in a blank, it will expand the information territory of the United States in order to occupy the opportunity of informationization. As a result, the future development of global informationization will follow the US road map. The United States can integrate the countries of the world into the informatization map of the United States. Looking at it now, this strategic attempt by the United States is far more effective than winning a war of blood and hurricanes. When information warfare is not only a battle, this is not only manifested in the blurring of the preparation and implementation of information warfare, especially in the attack of information warfare on people’s thoughts and spirit. The formation of thoughts and spirits is a subtle process. Through the information superiority, we can achieve the goal of “no war and defeated soldiers” or “less war and defeated soldiers”. The general approach is to use information superiority to create contrast between the enemy and the enemy, use psychological warfare and strategic deception to shake, frustrate the enemy’s military, people’s hearts and government beliefs, and destroy the enemy’s normal political and economic operation system. Means can put the enemy in a state of paralysis, curb the will of the hostile country to wage war, or deprive it of its ability to war. In the 1980s, the scenes of the US-Soviet confrontation were very interesting. Reagan, the US president who is good at acting, has proposed an aggressive “Star Wars” plan, claiming to make all the strategic nuclear missiles of the Soviet Union useless. As soon as the plan was announced, the United States started to promote all the propaganda machines and caused a great sensation in the world. The Soviet leaders convened an emergency meeting in succession and decided to resolutely respond to the blood and establish a strategic defense shield of the Soviet Union. In fact, the “Star Wars” program in the United States only carried out a little bit of technical experimentation. It didn’t cost much at all, but a movie of the same name “Star Ball” was popular in the world. However, the Soviets were very hardworking and hard work. When the national economy was on the verge of collapse, the vast ruble was still thrown into the arms race. The Soviet Union, which had been unable to do so, ran out of the last drop of blood after seven years. It cannot be said that the collapse of the Soviet economy and the collapse of the regime were not dragged down by the US information war. Paying attention to the people’s war that defends the boundaries of information. Under the conditions of information warfare, national sovereignty has a new content. The extension of national security has expanded and its connotation has become more abundant. The influence of information warfare is no longer limited to the military field, but radiates to the whole. Human society. Under the conditions of information warfare, the important magic weapon for a weak country to defeat a powerful country is the people’s war. Only by insisting on the people’s war under the conditions of information warfare can we effectively defend the national information territory and safeguard national information sovereignty. In addition to information technology and tactics, the most important thing is to grasp the construction of the information talent team and build the two lines of the national spirit defense line in the information age. Those who have talents are in the world. The outcome of the information warfare depends to a large extent on human factors, and must be supported by a large number of high-tech information warfare personnel. In the information warfare, a small number of top information talents can often play a key role in the outcome of the war. During the Second World War, in order to grab a German atomic physicist, the US military changed the direction of the attack of the three Army divisions. After the end of World War II, the history of “the wise man grabbed the people, the fools took the device” was even more intriguing. In the East, the Soviets were busy carrying the seized tanks and cannons; in the West, Americans hurriedly transported more than 3,000 German scientists back home. More than half a century has passed, and the country that grabbed talents is still continuing to write a history of robbing people, and its economy, technology and military are incomprehensible. The country that robbed the weapon was now facing the reality of being robbed. After the disintegration, the Soviet Union had tens of thousands of outstanding scientific and technological talents to change their positions to serve the opponents of the year. As a commanding height of military struggle, the struggle for talents is more decisive in the military contest of the information age. Compared with the “hard killing” brought about by information warfare, the “soft killing” of information warfare is even more terrible. The spiritual realm is the most “window of vulnerability” under the conditions of information warfare. As information technology becomes more developed, channels become more and more fluent, and information sources are more extensive. People will get more and more information and get information faster and faster. The means of modernization have transmitted the information to be transmitted to the countries of the world effectively without any restrictions. At present, developed countries pay great attention to using their advanced information technology to establish a global network of radio, television, and computer networks, thereby exporting their political opinions and values on a large scale and expanding the information frontier. As a result, countries with backward informationization have been subjected to a strong spiritual impact. Therefore, in order to win the people’s war under the conditions of information warfare, from the individual, the media, the army to the whole country, we must comprehensively enhance the awareness of information and national defense, establish the concept of defending the national information territory and information boundary, and consciously build an invisible spiritual defense line. Related Links Scanning the overall situation of the world information war It can be said that the development of the world information warfare has gone through three stages. The first stage: the period of information warfare before the Gulf War in 1991; the second stage: the implementation and maturity of the information war after the Gulf War to 1998; the third stage: the development period of the information warfare after 1998 . At present, the new military revolution triggered by information warfare is still going on around the world. The transformation of mechanized warfare into information warfare has been fully carried out in the world. The armed forces of major countries around the world are adjusting their strategies and tactics, preparing equipment, and combat training in accordance with the information warfare, in preparation for winning information warfare. All the wars after the Gulf War have been marked with traces of information warfare. The power of information warfare is impacting all areas of society. Information warfare techniques and techniques click Currently, the world’s countries in the application and development of information warfare technology are mainly: 1. Reconnaissance and surveillance technology. Various means of reconnaissance, surveillance, early warning and navigation, including space-based, space-based, sea-based and foundation. 2. Platform integrated information warfare system. Realize radar warning, missile launch and attack alarm, information support, information interference and avoidance, and synergistic integration, and integrate with other information equipment on the platform to achieve information sharing. 3. Network command and control warfare technology. 4. Computer virus technology. 5. Attacking weapons technology. Including electromagnetic pulse weapons, ultrasonic weapons and infrasound weapons. 6. Advanced electronic countermeasures technology. The latest information warfare equipment glimpse In the development of information warfare weapons, in recent years, the following equipments have been developed or put into active service in various countries. 1. The Joint Surveillance and Target Attack Radar System is a battlefield information processing system that accurately detects moving and fixed targets to cope with the implementation of long-range precision strikes, and provides commanders with important information about combat development and combat management. 2. The Joint Tactical Air-to-Ground Information Station is a weapon support system that processes the vital information needed for space-based sensor data and operational capabilities for early warning missile launches. 3. A beam-energy weapon can penetrate targets hundreds of kilometers or even thousands of kilometers in an instant without leaving a “hard injury”, especially for the direct destruction of high-precision guided high-tech weapons. Therefore, it is considered to be tactical air defense and anti-armor. Optoelectronic countermeasures and even strategic anti-missile, anti-satellite, anti-satellite, multi-purpose ideal weapon for all spacecraft. 4. Smart warfare, woven with a fiber optic network and a conductive polymer network, and a miniature measurement system that monitors the soldier’s physical condition. In the future battlefield, a soldier was injured. At the moment of his fall, the medical staff at the ambulance center can accurately determine whether it is a bullet or a knife wound, where the injured part is, and other basic injuries. In addition, there are military robots, shipboard electronic warfare systems, high-power RF amplifier technology, advanced antenna technology and signal processing technology. The information warfare is fiercely competitive. Looking at the world, more than 20 countries including Britain, France, Israel, and Russia have conducted in-depth research on information warfare. The development of information warfare in the United States is at the forefront of the world, mainly in technology, equipment, and theory. United States: The information war strategy was changed from defense to attack. In order to improve the US military’s information warfare technical capabilities, the US Department of Defense has a specialized information system processing agency responsible for maintaining the 2.5 million computers used by the US military. It is also studying how to improve the attack capabilities of computers and create communication networks and financial systems that destroy hostile countries. And the intrusion of the power system. As early as the fall of 2000, the US Space Command Center began to develop aggressive computer weapons. This means a major adjustment in the US military’s information war strategy—from strategic defense to strategic attack. Russia: The focus of information warfare is on “Heavenly Soldiers.” The development of information warfare in Russia has concentrated on the development of “Heavenly Soldiers” — the astronauts. In 2002, Russia invested about 31.6 billion rubles for space research, 5.4 billion rubles for the development of global navigation systems, and strengthened the development of lasers, high-power microwaves and anti-satellite weapons. Japan: Accelerate the formation of information warfare units. The Japanese Defense Agency is forming an information warfare force of 5,000 people, focusing on the development of cyber weapons as the focus of future defense plans, and speeding up the construction of the Japanese Army’s digital forces. EU and other Western countries: embarking on the construction of digital troops. Countries such as France, Germany, Britain, Canada, Australia, the Netherlands and Sweden are also developing platforms and individual C4I systems. More than 10 countries, including France, Britain, Germany, Australia, Canada, Italy, and Israel, are embarking on the implementation of digital military and digital battlefield construction plans. Among them, most countries are concentrating human and financial resources to develop the equipment needed for digital units, and a few countries in the past have conducted several digital force test exercises. In the future, while the above-mentioned countries continue to develop the digital “hardware” of the battlefield, they will begin to consider the composition of the digital units, and more countries will join the ranks of the digital construction of the troops. |
| Source: China National Defense News |
Original Mandarin Chinese:
如果說,1991年的海灣戰爭是美國第一次把信息戰從研究報告中搬上實戰戰場,那麼去年結束的伊拉克戰爭也許就是信息戰在實戰中的進一步發展。信息戰,作為21世紀新軍事革命狂飆的重心,已經越來越引起人們的重視。然而,透過信息戰研究熱鬧的場面,我們會發現,相當多的人們只是從單純軍事和技術的角度認識信息戰的,但信息戰其實並不這麼簡單——
信息戰是人類進入信息時代新出現的一種戰爭現象。它不是一種簡單的作戰樣式,而是相對於火力戰的一種新的戰爭形態。信息戰的出現對諸如戰爭對象、戰爭界限、戰爭內容等許多傳統戰爭理念都形成了重大突破,其中尤其應該引起關注的是信息戰攻擊思想和精神的一面。
看到的只是冰山一角
目前世界上關於信息戰的概念有幾十種,然而,很多卻只是單純從軍事和技術的角度來認識信息戰的,即使處於信息戰領先地位的美國也只是從上個世紀末才開始從戰略高度和社會意義上思考這個問題,這很不全面。認識信息戰的一個重要前提是,不應該簡單地用工業時代的戰爭觀來看待信息戰。信息時代,電腦和網絡大大改變了以往的戰爭形態。信息戰中,軍隊與社會、軍人與平民、戰爭與犯罪、國家與個人在很多情況下已經交織在一起,分不清,理還亂。
信息戰廣義地指對壘的軍事(也包括政治、經濟、文化、科技及社會一切領域)集團搶佔信息空間和爭奪信息資源的戰爭,主要是指利用信息達成國家大戰略目標的行動﹔狹義地是指武力戰中交戰雙方在信息領域的對抗,奪取制信息權。需要強調的是,信息戰不是一個簡單的軍事技術問題,不應該被理解為一種作戰樣式。信息戰實際上是一種戰爭形態。
“信息”這個名詞相對於時代來理解,是與農業時代、工業時代相對應的﹔就社會形態而言,又是與農業社會、工業社會相呼應。同時,它又是與物質、能量相提並論的人類必須的三大資源之一。考察信息戰,隻有從這個層次上去認識,才能揭示真正意義上的信息戰。
信息戰的崛起不在於它用了什麼樣的名詞,也不是戰爭名詞上冠以“信息化 ”、“信息”、“信息時代”、“數字化”這些時髦的詞藻那麼簡單。它是社會和科技發展的必然結果,帶有革命性、劃時代的意義。 20世紀末出現的信息戰,或者說我們已經看到的信息戰只是冰山之一角,僅僅是體現在軍事領域中的局部和有限的信息戰。隻有當世界達到全面網絡化,地球成為真正意義上的小村落時,我們才能看到那種廣義上、真正的信息戰。
信息戰不隻靠軍隊打
一提起打信息戰,人們往往首先就想到軍隊。確實,傳統戰爭中,軍隊是戰爭的主角,戰場也主要是軍人的舞台。信息戰條件下,情況則大不一樣。戰場的範疇大大擴展,戰爭變得遠遠不只是軍隊的事情,而是發展成高技術條件下的全民戰。信息戰不只是通過軍隊,同時也可以通過全社會網絡來實施。隨著世界信息高速公路的建設,信息戰已難以劃定界限。任何社會民間組織甚至個人隻要擁有普通計算機設備、掌握計算機通訊技術,都有可能利用全球聯網的計算機與通信系統參與一場信息戰。
信息戰不隻打軍隊主要表現在:第一,信息戰的參與者不再僅限於軍人,而且還包括普通民眾。信息戰作戰人員既可以是正規軍人,也可以是十幾歲的少年黑客。第二,信息戰所使用的許多武器裝備,如計算機、光學儀器等可以不再是軍用品,在民用品市場上都可買到。以信息戰強國美國為例,美軍的信息戰系統在很大程度上依賴民用信息基礎設施。美國軍方高層人士把美軍軍隊信息化變革稱為“從市場上買來的”。第三,信息戰作戰不單在戰場,而是分佈於整個社會。 “戰場只是士兵陣亡的地方,已不再囊括信息戰交戰場所。”
信息戰不隻在戰時打
自有戰爭以來,進攻者發動戰爭,防御者抵禦侵略,都要進行周密的戰爭準備。特別是機械化戰爭,呈現出明顯的階段性、程序化。而信息時代的戰爭,戰爭準備與實施的界限則日趨模糊,甚至混為一體。環顧世界,不難發現,信息強國幾乎每天都在進行戰爭:輿論宣傳、情報對抗、網絡偵察等等。這些實際上都是轉化了形式的信息戰,可以稱之為輿論戰、情報戰、網絡戰。
伊拉克戰爭中,輿論戰的威力讓世人大開眼界。有人說,作為信息戰作戰形式之一的“輿論戰”自有戰爭以來就一直在進行著。進行“輿論戰”的較早案例甚至可以追溯到中國夏朝的《甘誓》以及後來的《討曹檄文》與《討武檄文》。 “輿論戰”的進行完全沒有戰時與平時的界限。它通過控制、操縱、策劃、利用各種輿論工具,有計劃地向受眾傳遞經過選擇的信息,影響受眾的情感、動機、判斷和抉擇,從而對戰爭結果產生重大而直接的影響。至於信息戰中的情報戰、網絡戰就更是無視戰時與平時的分別了。當年,美國克林頓政府提出了構建信息高速公路、推進全球信息化的主張。此舉曾讓世人認為美國正在引領人類社會步入信息化時代。然而,美國的戰略意圖其實是趁人類社會的信息化尚處於一片空白之時,跑馬圈地,擴張美國的信息疆域,以期佔住信息化的先機。如此一來,全球信息化未來的發展就將按美國的路線圖行進。美國可以一舉將世界各國納入美國規劃的信息化版圖。現在看,美國的這一戰略企圖,其成效已遠遠勝於贏得一場硝煙彌漫、血雨腥風的戰爭。
信息戰不隻打戰時,這不僅表現為信息戰戰爭的準備與實施界限模糊,尤其體現在信息戰對人的思想和精神的攻擊上。思想和精神的形成是一個潛移默化的過程,通過信息優勢可以達成“不戰而屈人之兵”或“少戰而屈人之兵”的目標。其一般做法是:利用信息優勢在敵我之間製造反差,運用心理戰和戰略欺騙等手段,動搖、沮喪敵方軍心、民心和政府信念,破壞敵方正常的政治、經濟運行體系,通過上述手段可以使敵國處於癱瘓狀態,遏制敵對國家發動戰爭的意志,或使其喪失戰爭能力。
上個世紀80年代美蘇對峙中的一幕場景很值得人玩味。擅長演戲的美國總統裡根提出了一個咄咄逼人的“星球大戰”計劃,號稱要讓蘇聯的所有戰略核導彈失去作用。該計劃一宣布,美國就開動全部的宣傳機器拼命鼓吹,在全世界引起了巨大轟動。蘇聯領導人連續召開緊急會議,決定不惜血本堅決應對,建立起蘇聯的戰略防禦盾牌。其實,美國的“星球大戰”計劃隻進行了星星點點的技術實驗,壓根就沒有花多少錢,倒是一部同名的《星球大球》的電影風靡世界。而蘇聯人卻非常認真地埋頭苦幹,在國民經濟已經瀕臨崩潰的情況下,仍然把大把的盧布投向軍備競賽。本來已經力不從心的蘇聯在7年之後流盡了最後一滴血。不能說,蘇聯經濟的崩潰及政權的垮台沒有受美國信息戰的拖累。
關注保衛信息邊界的人民戰爭
在信息戰條件下,國家主權有了新的內容,國家安全的外延擴大了、內涵更豐富了,信息戰的影響也不再僅僅局限於軍事領域,而且輻射到整個人類社會。在信息戰條件下,弱國戰勝強國的重要法寶就是人民戰爭。隻有堅持打信息戰條件下的人民戰爭才能切實保衛國家信息疆域,維護國家信息主權。這其中除了信息技術和戰法等因素外,最主要的是抓住信息人才隊伍建設與構築信息時代的全民精神防線兩個環節。
得人才者興天下。信息戰的戰果如何,在很大程度上取決於人的因素,必須有大量的高技術信息戰人才作支撐。
在信息戰中,為數不多的頂尖信息人才往往能對戰爭的勝負起到關鍵作用。二戰期間,美軍為了把一個德國原子物理學家搶到手,竟然將3個陸軍師的進攻方向作了改變。二戰結束後那段“智者搶人,愚者奪器”的歷史更是耐人尋味。在東方,蘇聯人忙著搬運繳獲來的坦克大砲﹔在西方,美國人卻急急把3000多名德國科學家運回國內。半個多世紀過去了,當年搶人才的國家如今仍然在續寫著搶人的歷史,其經濟、科技和軍事不可一世。當年搶兵器的國家如今則在無奈地面對著被搶的現實。解體後的蘇聯有上萬名優秀科技人才改換門庭,服務於當年的對手。人才之爭作為軍事鬥爭的一個制高點,在信息時代的軍事較量中,更具有決定性的意義。
與信息戰所帶來的“硬殺傷”相比,信息戰的“軟殺傷”更為可怕。信息戰條件下精神領域是最“易受攻擊之窗”。
隨著信息技術越來越發達,信道越來越流暢,信息來源更為廣泛,人們獲取的信息將越來越多,獲取信息的速度也越來越快。現代化的傳播手段把所要傳遞的信息幾乎不受任何限制,有效地傳到世界各國。當前,發達國家十分注意利用它們的先進信息技術,建立覆蓋全球的廣播、電視、計算機網絡,藉此大規模輸出其政治主張和價值觀念,擴充信息疆域。其結果是信息化發展落後的國家受到強烈的精神沖擊。因此,要想打贏信息戰條件下的人民戰爭,從個人、媒體、軍隊到整個國家都必須全面增強信息國防意識,樹立保衛國家信息疆域和信息邊界的觀念,自覺築起無形的精神防線。
相關鏈接
世界信息戰總體形勢掃描
可以認為,世界信息戰的發展經歷了3個階段。
第一階段:1991年海灣戰爭以前信息戰的醞釀和提出時期﹔
第二階段:海灣戰爭後至1998年前信息戰的實施和成熟時期﹔
第三階段:1998年後至今遏制信息戰的發展時期。
當前,信息戰引發的新軍事革命仍在全球進行。機械化戰爭向信息戰的轉變已在全球全面展開。全世界各主要國家的軍隊正按照信息戰思想調整戰略戰術、編制裝備、作戰訓練等,為打贏信息戰作準備。海灣戰爭以後的所有戰爭無不烙上信息戰的痕跡。信息戰的威力正沖擊著社會的各個領域。
信息戰實戰技法點擊
當前,世界各國在信息戰技術手段的應用與發展上主要有:
1.偵察監視技術。包括天基、空基、海基和地基在內的各種偵察、監視、預警、導航等手段。
2.平台一體化信息戰系統。實現雷達告警、導彈發射和攻擊告警、信息支援、信息幹擾及規避、協同一體化,而且與平台上其他信息設備綜合為一體,達成信息共享。
3.網絡指揮控制戰技術。 4.計算機病毒技術。
5.攻心武器技術。包括電磁脈沖武器、超聲波武器和次聲波武器。 6.先進電子對抗技術。
最新信息戰裝備掠影
在信息戰武器發展上,近年來各國研製或已投入現役的主要有以下裝備。
1.聯合監視與目標攻擊雷達系統,是一種戰場信息處理系統,能精確探測移動的和固定的目標,以配合實施遠距離精確打擊,還能向指揮官提供有關戰況發展和戰鬥管理的重要情報。
2.聯合戰術空對地信息站,是一種武器支援系統,能處理供預警導彈發射用的天基傳感器數據、作戰能力所需的重要信息。
3.束能武器,能在瞬間穿透數百公裡甚至數千公裡外的目標而不留下“硬傷”,尤其對精確制導高技術武器有直接的破壞作用,因此被認為是戰術防空、反裝甲、光電對抗乃至戰略反導、反衛星、反一切航天器的多功能理想武器。
4.智能戰衣,編織有光纖網絡和導電聚合網絡,並有監視士兵身體狀態的微型測量系統。在未來戰場上,一名士兵受了傷,就在其倒地的瞬間,救護中心的醫務人員就能準確判斷出是彈傷還是刀傷、受傷部位在何處以及其他基本傷情。
此外,還有軍用機器人、艦載電子戰系統、強功率射頻放大器技術、先進的天線技術和信號處理技術等等。
信息戰國力競爭激烈
放眼世界,現在已有英國、法國、以色列、俄羅斯等20多個國家對信息戰展開深入研究。美國信息戰發展走在世界前列,主要體現在技術、裝備、理論等方面。
美國:信息戰戰略由防轉攻。為了提高美軍信息戰技術能力,美國國防部有專門信息系統處理機構負責維護美國軍方使用的250萬台電腦,並在抓緊研究如何提高電腦的攻擊能力,製造破壞敵對國的通信網絡、金融系統及電力系統的入侵病毒。早在2000年秋天,美國太空指揮中心已開始研製攻擊性電腦武器。這意味著美軍信息戰戰略的重大調整———由戰略防禦轉向戰略進攻。
俄羅斯:信息戰重心在“天兵”。俄羅斯的信息戰發展集中力量發展“天兵 ”———航天兵。 2002年俄羅斯投入約316億盧布用於太空專項研究,54億盧布用於全球導航系統的研發,還加強了激光、高功率微波和反衛星武器的研製。
日本:加快組建信息戰部隊。日本防衛廳正在組建5000人規模的信息戰部隊,把網絡武器的開發作為今后防衛計劃的重點,並加快了日本陸軍數字化部隊的建設。
歐盟和其他西方國家:著手數字化部隊建設。法、德、英、加、澳、荷蘭和瑞典等國也在研製平台和單兵的C4I系統。法國、英國、德國、澳大利亞、加拿大、意大利、以色列等10多個國家都在著手執行數字化部隊和數字化戰場建設計劃。其中,多數國家正在集中人力財力開發數字化部隊所需要的裝備,少數走在前面的國家已進行過多次數字化部隊試驗演習。今後,上述國家在繼續開發戰場數字化“硬件”的同時,將開始考慮數字化部隊的編成結構,並將有更多的國家加入部隊數字化建設的行列。
來源:中國國防報
Original Referring URL: http://people.com.cn/BIG5/junshi/1078/