中國的繁榮與經濟發展支撐起強大的中國軍事文化
現代英語:
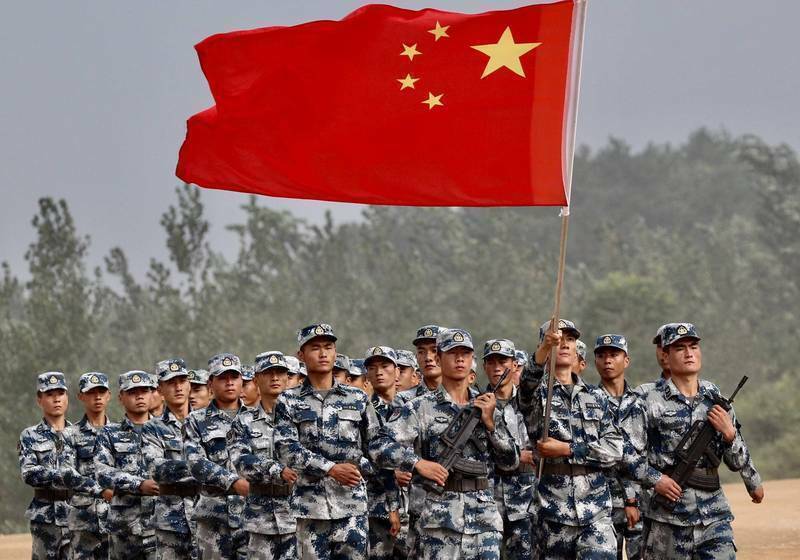
A strong military culture is the internal guarantee for the People’s Army to be invincible, victorious in all battles, and to continue to grow and develop. It is the spiritual fertile soil that nourishes officers and soldiers and an important factor in improving the combat effectiveness of the troops. The report of the 20th National Congress of the Communist Party of China emphasized the need to “flourish and develop a strong military culture and strengthen the cultivation of fighting spirit.” For the People’s Army, to thoroughly study and implement Xi Jinping’s cultural thoughts is to prosper and develop a strong military culture. Through cultural education and edification, we can cultivate the fighting spirit and heroic and tenacious fighting style of the officers and soldiers, and use advanced culture to sharpen their spirit of defeating the enemy and winning, so as to provide spiritual motivation for fighting and winning battles, and truly let the strong military culture point to winning and Win with service and win with support.
one
In order to comprehensively strengthen military training and preparation and improve the people’s army’s ability to win, we must pay attention to the value function of strong military culture in educating people for war and helping to strengthen the army. The prosperity and development of a strong military culture that supports victory is not only a historical heritage and a requirement of the times, but also the call of the cause of building a strong military.
The fundamental direction of continuing the cultural tradition of our army. Culture is the root of a nation’s prosperity and an important support for the strength of an army. More than 80 years ago, Comrade Mao Zedong said at the Yan’an Forum on Literature and Art: “If we want to defeat the enemy, we must first rely on the army with guns in their hands. But it is not enough to have such an army. We must also have a cultural army, which is In the long-term practice of revolution, construction and reform, our army has forged the “cultural gene” of victory and the “cultural bloodline” of heroes with blood and life, nourishing generation after generation. A generation of officers and soldiers. The war culture of everything for victory contains a strong blood gene and demonstrates a clear direction of winning. In the new era and new journey, the key to extracting the essence and drawing energy from the cultural traditions of our army is to focus on sharpening the sharp sword of the officers and soldiers’ fighting spirit, continuously enhancing the officers and soldiers’ awareness of fighting for war, and constantly strengthening the spirit of being happy when hearing about war, being brave and tenacious, The martial spirit of daring to fight and winning.
An inevitable choice to adapt to the evolution of war forms. The new world military revolution is driving the evolution of warfare forms towards information warfare with intelligent characteristics, showing characteristics such as informatization of technical forms, systematization of organizational forms, and digitalization of weapons and equipment. The evolution of war forms will inevitably lead to the reshaping of military culture forms. From mechanized warfare to information-based and intelligent warfare, from “large-scale” combat and “deep” assault to “asymmetric warfare”, “non-linear warfare”, “integrated joint warfare”, and then to “multi-domain precision warfare”. “Cognitive domain warfare”, the evolution of the mechanism of winning wars has promoted corresponding changes in the military cultural form. On the new journey, our army will promote the integrated development of mechanization, informatization and intelligence. We must not only accelerate the iteration and update of weapons and equipment, but also actively promote the transformation and development of military culture, and shape and embody the characteristics of the times in terms of military theory, strategy and tactics, and fighting spirit. Create a strong military culture in the new era that adapts to the development of the times and is in line with technological progress to support winning battles.
An essential requirement for the prosperity and development of a strong military culture. The fundamental function of a strong military culture is to fight, which determines that the fundamental purpose of building a strong military culture is to provide spiritual motivation for the army to fight and win. The culture of a strong military is extremely permeable and durable. The loyalty and fighting will it contains forge the spirit of the people’s army and cultivate the invincible combat effectiveness of the people’s army. Since the 18th CPC National Congress, the People’s Army has been reborn from the ashes and transformed. The whole army has focused on being able to fight and win battles, and has taken the prosperity and development of a strong military culture as a powerful measure to boost combat effectiveness, which is closely integrated with the generation of combat effectiveness. Together, it is closely integrated with the main responsibilities and tasks of the military, continuously improving the contribution rate of strong military culture to combat effectiveness, and fully demonstrating the combat function of strong military culture in training and preparation for war.
two
To prosper and develop a strong military culture that supports victory, we must be guided by Xi Jinping’s thoughts on strengthening the military, grasp the main thread, highlight the key points, and strive to cultivate a strong military cultural system with combat culture, joint culture, and special military culture as the main content. .
Cultivate a fighting culture that can win battles. Combat culture reflects the inherent essence of a strong military culture and determines the value positioning and value orientation of a strong military culture. Combat culture is a bloody culture that has been tempered, refined and accumulated through military struggle practice. It has a profound cultural heritage, strong combat characteristics and distinct characteristics of the times. Its value function is mainly manifested in strengthening the awareness of fighting, improving combat skills, and sharpening the fighting spirit. Spirit is an important component of combat effectiveness, the main body of the strong military cultural system, and an important magic weapon for the People’s Army to win victory. To cultivate a combat culture, we must focus on strengthening the responsibility of officers and soldiers to serve in the army, lead the army in combat, and train the army for combat, and the combat spirit of “not fearing hardship or death” and the combat quality of being brave and tenacious and daring to fight and win, and effectively raise the combat effectiveness standard As the basic focus and fundamental foothold for the prosperity and development of a strong military culture, and as the fundamental measure for testing the quality and effectiveness of building a strong military culture.
Cultivate a joint culture of winning together. In modern warfare, there is no war without integration and no victory without integration. The basic combat style is integrated joint operations. Joint culture is the sum of the joint knowledge system, values, ways of thinking and behavioral norms required to win modern warfare, and is widely permeated in the joint combat system, force structure, behavioral codes and models. It is like an invisible hand, powerfully pushing the joint combat system from “form connection” to “spiritual connection”, from “core connection” to “heart connection”. To cultivate a joint culture, we must rely on mission-driven and joint exercises and training to build a political soul for officers and soldiers to obey the Party’s command, cultivate the concept of joint victory, improve the knowledge system of joint operations, temper the thinking mode of integration and linkage, and cultivate common emotions. and values, a strong and stable collective psychological identity, and an unbreakable will to win.
Cultivate a rich and colorful military culture. When only one flower blooms it is not spring, but when a hundred flowers bloom the garden fills with spring. In the course of military practice, our army has formed distinctive military and arms cultures, including the Army’s “Armored Iron Stream” culture, the “Artillery God of War” culture, the “Army Aviation War Eagle” culture, the Navy’s “Deep Blue Culture”, the Air Force’s “Sky Culture”, and the Air Force’s “Sky Culture”. The “Eagle”, “Sky Ladder” and “Sky Arrow” cultures; the Rocket Force’s “Sword Sharpening Culture” and “Long Ribbon Culture”, and so on. The magnificent flowers of military culture not only constitute a unique spiritual symbol, but also serve as a “multiplier” for enhancing the combat effectiveness of the troops. Creating a military culture with distinctive characteristics and profound heritage does not conflict with cultivating a joint culture. The culture of each service supports the joint culture, and the joint culture realizes the organic integration of the cultures of each service. The deeper the roots of the distinctive cultures of each service are, the stronger the combat effectiveness of the joint culture will be, and the more combat-effective it will be. At the same time, we should vigorously carry out colorful military camp cultural activities, use distinctive culture to forge the military soul, gather soldiers’ hearts, and boost morale, strive to create a lively situation where everyone has a stage, and more effectively play the role of educating people with culture, Use culture to educate people and use culture to support war.
three
To prosper and develop the culture of strengthening the army in the new era, we must insist on serving and winning as the fundamental direction, strengthen historical confidence, and continue the genes of victory; insist on fighting for the sake of war and strengthen combat attributes; take multiple measures, integrate innovation, and create a culture of advocating martial arts and refining martial arts. Create a strong atmosphere and use strong military culture to boost combat effectiveness.
Strengthen the winning genes of revolutionary soldiers in the new era. Culture is essentially a spiritual carrier. The fighting culture of daring to fight and winning that our army has forged in the course of more than 90 years of struggle has created a unique advantage in defeating the enemy and winning the future. On the new journey, we must vigorously carry forward the glorious traditions of the People’s Army, publicize the typical deeds of advanced heroes and combat heroes, guide officers and soldiers to draw nourishment from the revolutionary spirit, draw fighting spirit from the glorious war history, draw strength from the combat honor, and let the People’s Army’s The winning gene is passed on from generation to generation. At present, major changes in the world are accelerating, and changes in the world, the times, and history are unfolding in unprecedented ways. We must educate and guide officers and soldiers to not fear powerful enemies, recognize that upholding the Party’s absolute leadership over the army is the fundamental guarantee for our army to win battles, recognize that the overall might of the people’s war is the magic weapon for our army to defeat the enemy, and combine the fighting spirit with the scientific spirit. , continue the fine traditions of our army, and firmly establish the confidence and determination to win the battle based on the existing equipment.
Improve the combat index of strong military culture construction. President Xi pointed out: “We should combine the traditions and mission characteristics of each unit to strengthen military culture construction, build a strong military culture, and cultivate the troops’ fearless heroism and brave and tenacious fighting style.” We should fundamentally redirect military cultural work to support Fight and win the battle. We will deeply explore revolutionary historical themes, highlight the creation of realistic military themes, and always shape people with noble spirits and inspire people with excellent works. We regularly arrange literary and artistic cavalry teams, battlefield propaganda teams, battlefield photography teams, etc. to go into cold areas, deserts, plateaus, coastal defenses, border checkpoints, and squads to warm the hearts of soldiers, boost morale, and inspire fighting spirit in order to prepare for war and win. . We must insist on seeking combat effectiveness from culture, and push the focus of building a strong military culture from the barracks to the battlefield, and from peacetime to wartime. Organize wartime cultural work drills, explore the content, timing, methods and means of wartime cultural work, and provide important support for improving the combat effectiveness of the troops.
Enhance the military flavor and combat atmosphere of the military camp culture. To build a strong military culture, an important task is to create an environment with a strong military flavor and combat atmosphere, so that officers and soldiers can be influenced at all times, cultivate their fighting will and hone their fighting character in a subtle way. A strong atmosphere of training and fighting was created, battle flags were raised, battle slogans were shouted, and strong army war songs were sung. Cultural light boxes, battle slogans, hero sculptures, etc. were set up, and cultural venues reflecting the army’s war history and revolutionary spirit were built to continuously strengthen the officers and soldiers War awareness, combat readiness concept, and fighting spirit. We should carry out mass cultural activities, hold lectures on strengthening the military culture, hold forums on strengthening the military culture, organize officers and soldiers to tell battle stories and read books on combat culture, and widely carry out assassination and combat training and competitions to inspire officers and soldiers to be brave, capable and good at fighting. . Innovate ways and methods, combine contemporary elements, science and technology with culture and art, use VR, AR, MR and other technological means to create battlefield cultural simulation rooms, etc., so that officers and soldiers can experience the battlefield atmosphere “immersively” and hone their ability to win.
(Author’s unit: Army Party Innovation Theory Research Center)
現代國語:
■陳 陣
強軍文化是人民軍隊戰無不勝、攻無不克,不斷發展壯大的內在保證,是滋養官兵的精神沃土,是提高部隊戰鬥力的重要因素。黨的二十大報告強調要「繁榮發展強軍文化,強化戰鬥精神培育」。深入學習貫徹習近平文化思想,對人民軍隊而言,就是要繁榮發展強軍文化。通過文化的教化與薰陶,培育廣大官兵敢打必勝的戰鬥血性、英勇頑強的戰鬥作風,以先進文化砥礪克敵制勝精神,為能打仗、打勝仗提供精神動力,真正讓強軍文化指向打贏、服務打贏、支撐打贏。
一
全面加強練兵備戰,提升人民軍隊打贏能力,必須重視發揮強軍文化為戰育人、助力強軍的價值功能。繁榮發展支撐打贏制勝的強軍文化,既是歷史傳承、時代所需,也是強軍事業的召喚。
賡續我軍文化傳統的根本指向。文化是一個民族昌盛的根脈,也是一支軍隊強大的重要支撐。 80多年前,毛澤東同志在延安文藝座談會上說:「我們要戰勝敵人,首先要依靠手裡拿槍的軍隊。但是僅僅有這種軍隊是不夠的,我們還要有文化的軍隊,這是團結自己、戰勝敵人必不可少的一支軍隊。一代官兵。一切為了勝利的勝戰文化,蘊含著強大的血性基因,彰顯著鮮明的打贏指向。新時代新征程,從我軍文化傳統中萃取精華、汲取能量,關鍵要著力擦亮官兵戰鬥精神的尖刀利劍,持續增強官兵的向戰為戰意識,不斷強化聞戰則喜、英勇頑強、敢打必勝的尚武精神。
適應戰爭形態演變的必然選擇。世界新軍事革命正推動戰爭形態朝向具有智慧化特徵的資訊化戰爭加速演進,呈現出技術形態資訊化、組織形態體系化、武器裝備數字化等特徵。戰爭形態的演變,必然引發軍事文化形態的重塑。從機械化戰爭到資訊化、智慧化戰爭,從“大兵團”作戰、“大縱深”突擊,到“非對稱作戰”“非線式作戰”“一體化聯合作戰”,再到“多域精確戰”“認知域作戰”,戰爭制勝機理的演變,推動軍事文化形態相應隨之改變。新征程上,我軍推進機械化資訊化智慧融合發展,既要加速武器裝備的迭代更新,更要積極推進軍事文化轉型發展,從軍事理論、戰略戰術、戰鬥精神等方面塑造和體現時代特質,打造與時代發展相適應、與技術進步相符的新時代支撐打贏制勝的強軍文化。
繁榮發展強軍文化的本質要求。強軍文化姓軍為戰的根本職能,決定了打造強軍文化的根本目的就是為能打仗、打勝仗提供精神動力。強軍文化具有極強的滲透性、持久性,其所蘊含的忠誠品質和鬥爭意志,鍛造著人民軍隊的精氣神,培育著人民軍隊無堅不摧的戰鬥力。黨的十八大以來,人民軍隊浴火重生、轉型重塑,全軍部隊以能打仗、打勝仗為根本著眼點,把繁榮發展強軍文化作為催生戰鬥力的有力舉措,與戰鬥力生成緊密結合在一起,與軍隊主責主業緊密結合在一起,不斷提升強軍文化對戰鬥力的貢獻率,充分彰顯了強軍文化在練兵備戰中的戰鬥功能。
二
繁榮發展支撐打贏制勝的強軍文化,必須以習近平強軍思想為指導,把準主脈、突出重點,著力培塑以戰鬥文化、聯合文化、部隊特色文化等為主體內容的強軍文化體系。
培育能打勝仗的戰鬥文化。戰鬥文化反映強軍文化的內在本質,決定強軍文化的價值定位和價值取向。戰鬥文化是歷經軍事鬥爭實踐錘煉、淘洗、積蓄形成的血性文化,具有深厚的文化底蘊、強烈的戰鬥特性和鮮明的時代特徵,其價值功能主要表現為強化打仗意識、提升作戰本領、砥礪戰鬥精神,是戰鬥力的重要構成要素,是強軍文化體系的主體,是人民軍隊打贏制勝的重要法寶。培育戰鬥文化,要著力強化官兵當兵打仗、帶兵打仗、練兵打仗的責任擔當,「一不怕苦、二不怕死」的戰鬥精神和英勇頑強、敢打必勝的戰鬥品質,切實把戰鬥力標準作為繁榮發展強軍文化的基本著力點和根本落腳點,作為檢驗強軍文化建設質效的根本尺度。
培育聯合製勝的聯合文化。現代戰爭無戰不聯、無聯不勝,基本作戰樣式是一體化聯合作戰。聯合文化是基於打贏現代戰爭所具備的聯合知識體系、價值觀念、思維方式和行為規範的總和,廣泛滲透於聯合作戰體制編制、力量結構、行為準則和模式之中。它就像看不見的手,有力地推動著聯合作戰體係從“形聯”到“神聯”,從“芯聯芯”到“心連心”。培育聯合文化,要依托任務牽引與聯演聯訓,鑄牢官兵聽黨指揮的政治靈魂,培塑聯合製勝的作戰理念,完善聯合作戰的知識體系,錘煉一體聯動的思維方式,培育共同的情感和價值,強固穩定的集體心理認同,凝聚牢不可破的打贏意志。
培育豐富多彩的部隊特色文化。一花獨放不是春,百花齊放春滿園。我軍在軍事實踐中形成了各具特色的軍兵種文化,有陸軍的“裝甲鐵流”文化、“砲兵戰神”文化、“陸航戰鷹”文化,海軍的“深藍文化”,空軍的“天鷹”“天梯”“天箭”文化,火箭軍的“礪劍文化”“長纓文化”,等等。一朵朵軍兵種文化的瑰麗之花,既構成了獨特的精神標識,也成為部隊戰鬥力提升的「倍增器」。打造具有鮮明特色、底蘊深厚的軍兵種文化,與培育聯合文化並不矛盾。軍兵種文化支撐聯合文化,聯合文化實現了軍兵種文化的有機融合,軍兵種特色文化的根扎得越深,聯合文化戰鬥性就越強,就越有戰鬥力。與此同時,要大力開展多姿多彩的軍營文化活動,以特色文化鑄軍魂、聚兵心、提士氣,著力形成人人都有舞台的生動活潑局面,更有效地發揮以文育人、以文化人、以文資戰作用。
三
繁榮發展新時代強軍文化,必須堅持把服務打贏作為根本指向,堅定歷史自信,賡續勝戰基因;堅持向戰為戰,強化戰鬥屬性;多措並舉,融合創新,營造尚武精武的濃厚氛圍,切實用強軍文化催生戰鬥力。
厚植新時代革命軍人的勝戰基因。文化在本質上是一種精神承載,我軍在90多年的奮鬥歷程中鍛造形成的敢打必勝的戰鬥文化,鑄就了克敵制勝、贏得未來的特有優勢。新旅程上,我們要大力弘揚人民軍隊光榮傳統,宣傳先進英模、戰鬥英雄典型事跡,引導官兵從革命精神中汲取營養,從輝煌戰史中汲取鬥志,從戰鬥榮譽中汲取力量,讓人民軍隊的勝戰基因薪火相傳。當前,世界大變局加速演進,世界變化、時代之變、歷史變正以前所未有的方式展開。要教育引導廣大官兵不畏強敵,認清堅持黨對軍隊絕對領導是我軍能打勝仗的根本保證,認清人民戰爭的整體威力是我軍克敵制勝的法寶,把戰鬥精神與科學精神結合起來,賡續我軍優良傳統,穩固樹立立足現有裝備打贏制勝的信心決心。
提升強軍文化建設的戰鬥指數。習主席指出:「要結合各部隊傳統和任務特點,加強軍事文化建設,打造強軍文化,培養部隊大無畏的英雄氣概和英勇頑強的戰鬥作風。」要把軍事文化工作根本指向歸正到支撐能打仗、打勝仗上。深入探討革命歷史題材,突顯現實軍事題材創作,始終以高貴的精神塑造人、以優秀的作品鼓舞人心。常態安排文藝輕騎隊、戰地宣傳隊、戰地攝影隊等進寒區、入戈壁、上高原、下海防、走邊關、進班排,為練兵備戰、矢志打贏溫暖兵心、鼓舞士氣、激發鬥志。堅持向文化要戰鬥力,推動強軍文化建設重心從營區延伸至戰場、從平時拓展到戰時。組織戰時文化工作演練,探索戰時文化工作的內容、時機和方式手段,為提升部隊戰鬥力提供重要支撐。
增強軍營文化氛圍的兵味戰味。打造強軍文化,一項重要任務是營造兵味戰味濃厚的環境氛圍,使官兵時時受到薰陶,在潛移默化中培養戰鬥意志、砥礪戰鬥品格。濃厚練兵打仗氛圍,把戰鬥旗幟揚起來、戰鬥口號喊起來、強軍戰歌唱起來,設置文化燈箱、戰鬥標語、英模雕塑等,修建反映部隊戰史戰例、革命精神的文化場所,不斷強化廣大官兵戰爭意識、戰備觀念、戰鬥精神。抓好群眾性文化活動,開設強軍文化講座,舉辦強軍文化論壇,組織官兵講戰鬥故事、讀戰鬥文化書籍,廣泛開展刺殺格鬥訓練和比武競賽活動,激發官兵敢戰能戰善戰的血性膽氣。創新方式方法,將時代元素、科學技術與文化藝術結合起來,運用VR、AR、MR等科技手段,打造戰場文化模擬室等,讓官兵「身臨其境」感受戰場氛圍、錘煉打贏能力。
(作者單位:陸軍黨的創新理論研究中心)