弘揚及影響中國軍事創新文化 //2016年01月12日08:XX 来源:解放军报
現代英語:
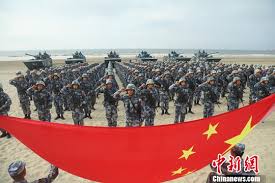
At the Central Military Commission’s reform work conference, President Xi Jinping emphasized, “We must focus on seizing the strategic commanding heights of future military competition, give full play to the role of innovation-driven development, and cultivate new growth points for combat effectiveness.” This important statement profoundly reveals the important position of military innovation in the strategy of reforming and strengthening the military.
History has repeatedly shown that in the process of military competition, whoever occupies the commanding heights of military culture may lead the trend of military innovation, stay ahead of the war and win strategic advantages in advance.
The deepening of national defense and military reforms currently underway is closely linked to the new world military revolution. “In this tide of the new world military revolution, whoever is conservative and complacent will miss precious opportunities and fall into strategic passivity.” President Xi’s words are deafening and thought-provoking. In the process of reforming and strengthening the military, every soldier is not a bystander, but a factor of innovation. In the face of reform, can we accurately grasp the latest trends in the development of world military theory and military technology? Can we adapt to the latest changes in the form of war? Can we find the right path and method for innovation? These should be questions that we should think about.
Culture senses the changes in the world, stands at the forefront of reform, and is the forerunner of the times. We build a strong military culture by leveraging the unique advantages of culture, breaking the conservative and rigid thinking pattern in the context of thousands of ships competing and hundreds of boats vying for the current, stimulating the vitality of military innovation, and allowing the latest achievements of military cultural innovation to continue to extend to reform.
Rocks are flying through the sky, waves are crashing against the shore, in the rolling tide of the new world military revolution, who has awakened and who is still sleeping?
–editor
The curtain has been raised on deepening the reform of national defense and the military. This reform is carried out against the backdrop of the surging tide of the world’s military revolution and is another milestone in the history of our military development. From “changing chess pieces” to “changing the chessboard”, institutional reform inevitably requires changes in the “rules of the game” and the military system; it requires accelerating the pace of building an informationized army based on a new organizational structure.
The new military revolution is a process of continuous innovation, and the informationized army is essentially an innovative army. We need to continuously cultivate a military innovation culture, enhance the vitality of reform, and promote the realization of the strategy of reform and strengthening the army.
(one)
The new trend of the development of world military culture requires us to strengthen cultural cultivation in the process of change and change the thinking logic of military innovation.
In a sense, the so-called strategic vision is the vision of understanding the future. Associated with the change in the field of observation, the “paradigm” of innovative thinking has changed accordingly: in the past, it was: practice-technology-theory. Now it is: theory-technology-practice. Associated with the change in the “paradigm” of thinking, since the 1980s, military innovation has gradually changed from the previous combat demand-driven model to the “theory-driven” model. Theoretical works such as “The Third Wave” and “Future Wars” by the famous American futurist Alvin Toffler have played a great role in the development of information society, information warfare and related technologies. As a result, the logic of military innovation has also changed accordingly. The previous order of innovation development was: scientific and technological progress-weapons and equipment-military theory-combat formation. The current development order is: military theory-scientific and technological progress-weapons and equipment-combat formation. The military culture of the information age has made combat commanders and military theory experts the leaders of military technology innovation.
Military theory experts and military technology experts have found that in developed Western countries, the evolution of modern military culture has gone through three stages:
Throughout the 19th century and before, most soldiers had not yet realized the huge role of scientific and technological progress in promoting the development of military power. Even a highly innovative military commander like Napoleon easily rejected the suggestion of American scientist Fulton to develop sailless warships. From the beginning of the 19th century to the First World War, although the Industrial Revolution had already affected other areas of society, most soldiers did not think about the role of new technologies in war. They only emphasized the use of existing equipment in their hands and would not think about improving and innovating equipment. This period is called the stage of soldiers “waiting for technology.”
At the beginning of the 20th century, the highly developed mechanical industry gradually changed the soldiers’ simple martial concept. On August 8, 1918, in the Battle of Emins, the assault power of the Allied “star” tanks and the bombing power of 300 British aircraft awakened the soldiers from their trenches. In the following 20 years, history has created a large number of new military strategists in the era of mechanized warfare, such as Fuller, Douhet, Guderian, Rommel, Montgomery, de Gaulle, Eisenhower, Zhukov, and Vasilevsky. They are not only proficient in military affairs, but also know the performance characteristics of tanks, aircraft, and other new technological weapons at the time. They regard science and technology as their second major and engineers as their close friends, thus making one innovation after another in the development of tactics. Guderian invented the armored blitzkrieg, Roosevelt accepted Einstein’s suggestion to make the atomic bomb, and Stalin treated a large number of aircraft designers as guests of honor. Because of this, during and after World War II, the military technology and military academic level of these countries have achieved unprecedented and substantial development. This period can be called the stage of “marriage between soldiers and technology”.
Since the 1960s and 1970s, due to the rapid development of new technologies such as microelectronics, artificial intelligence, genetic engineering, space, ocean development, new materials, and new energy, the wave of new technological revolution has enabled many far-sighted military strategists to further break the original thinking mode and propose that soldiers should stand at the forefront of scientific and technological development to envision future combat styles, and based on these ideas, in turn propose the goals and directions of military technology innovation. Military defense experts look forward to the development trends in the next 20 to 30 years, design new combat concepts, and innovate combat theories to propose the necessary technical support, and then scientific researchers will meet the new military needs from a technical perspective. Under the organization and guidance of soldiers, military technology has reduced the blindness of development, thereby obtaining faster and more military economic benefits. This period can be said to be the stage of soldiers “leading technology”.
The change from soldiers “waiting for technology” and “marrying technology” to “leading technology” reflects the objective trend of the increasingly close relationship between the development of military science and science and technology. This trend forces soldiers to change from being bystanders of technological development to being leaders of technological development.
In my country, due to the loss of the opportunity of the first industrial revolution, military culture is still in the stage of “waiting for technology” and “marrying technology”. The military concept that emphasizes history and neglects the future is used to designing our army’s tomorrow according to the opponent’s today; it is used to thinking about our army of tomorrow and fighting against today’s opponent.
On the journey of reform, many comrades’ ideas are still stuck in the Gulf War, Kosovo War, Afghanistan War, and Iraq War, which have been 15 or 20 years. The US military proposed the third “offset strategy” to select disruptive new technologies and create new “asymmetric military advantages.” The new military revolution will thus see a turning point: a new form of warfare – light warfare based on autonomous systems is slowly coming. In order to fulfill the historical mission of military reform and meet new challenges, we must strengthen cultural cultivation and transform the thinking logic of military innovation.
(two)
The cultural core of an army is deeply hidden in its military philosophy. In the process of implementing the strategy of reforming and strengthening the army, we should use modern scientific methods to carry out military innovation.
In human history, every great era not only gives people great tasks, but also provides people with new methods. Only those who have clearly defined the great tasks and mastered the new methods can lead the trend of the times.
The history of scientific development shows that many major scientific and technological innovations, as well as the raising and solving of major scientific problems, are often the result of certain breakthroughs in scientific methods. Galileo’s discovery of the laws of falling motion and the law of inertia is inseparable from his systematic use of experimental and mathematical methods; Darwin’s creation of the theory of biological evolution benefited from the scientific observation method and the historical comparison method; the theoretical experimental method played an important role in the emergence of Einstein’s theory of relativity; Marx’s “Capital” was able to deeply analyze the complex capitalist society and achieve great success. One of the important reasons is that he cleverly applied the method of unity of logic and history, as well as the method of scientific abstraction, taking the “simplest, most common, and most basic things” – commodities, as the logical and historical starting point of scientific research, rising from the concreteness of perception to the abstract provisions, and then from the abstract provisions to the concreteness of thinking.
Similarly, innovation in military theory also first relies on the new methods of the times. The Art of War was published in China in the late Spring and Autumn Period because the ancient system theory represented by “yin and yang” and “five elements” had matured and been complete by then; Clausewitz wrote On War because Newton’s mechanics and Hegel’s dialectics provided him with weapons to study war; Mao Zedong’s military thought is the result of Comrade Mao Zedong’s use of Marxist philosophical methods to study the practice of China’s revolutionary war.
The scientific and technological revolution has promoted the improvement of social productivity and military combat effectiveness, and also prompted the development of philosophical thought.
The “three major discoveries” of the 19th century (evolution, cytology, and conservation and transformation of energy) led to the end of German classical philosophy and the emergence of Marxist philosophy.
In the 20th century, the emergence of relativity, quantum mechanics and life sciences, the development of information technology, biotechnology, nanotechnology, new materials technology, and Internet technology have changed and are continuing to change the world’s landscape. In the 1960s and 1970s, along with the wave of new technological revolution, the revolution of scientific methods reached an unprecedented high, showing the trend of natural science research methods, methods, models and concepts penetrating and blending into the field of social sciences. New scientific methodologies have emerged one after another: system theory, control theory, synergy theory, mutation theory, information theory, discrete theory, functional theory, intelligence theory, optimization theory, reaction theory, fuzzy theory, art theory, as well as “chaos” and “fractals”. From a philosophical perspective, the methods proposed by these cross-disciplinary disciplines can be summarized as system methods and complex system methods.
In 1958, after the U.S. military implemented the separation of military administration and military command, it did not quickly regain vitality. The Pentagon’s resource management was in chaos and was still in a precarious situation. In 1960, McConamara took over the Ministry of Defense. In response to the chaotic situation in which the three armed forces acted independently in the use of national defense resources, he proposed the management principle of “combining centralized guidance with decentralized implementation” in 1962, adopted the system engineering method, coordinated the planning of national defense and weapons and equipment construction, and proposed a “Planning, Programming and Budgeting System (PPBS)”, which straightened out the relationship for the construction of the U.S. military and saved resources.
In 1986, the U.S. military implemented the Department of Defense Reform Act, which centralized the power of the Department of Defense and the Joint Chiefs of Staff and established a new set of regulations that unified centralization and authorization. This ensured the smooth implementation of joint operations and laid the foundation for future integrated joint operations.
At the beginning of the 21st century, when Donald Rumsfeld was the Secretary of Defense, according to the development of the new military revolution, the U.S. military changed the PPBS system’s management habits based on target tasks and proposed a PPBE system based on capability requirements, namely “Planning, Programming, Budgeting and Execution System”.
The PPBS system and the PPBE system are both typical applications of the system science method in national defense management. From a methodological perspective, the characteristics of these systems are: grasping the reality from the future, determining capabilities based on missions and tasks, and driving technology creation and selecting combat formations based on capability requirements. In short, the “upstream” determines the “downstream”, the “top” determines the “bottom”, and the “front end” determines the “back end”.
The ideas of system theory and complexity methods have been deeply applied in the transformation of the US military. They believe that previous military theories, namely the theories of famous scholars such as Clausewitz and Jomini, are all based on Newtonian mechanics. In today’s operations, the enemy’s military organization and combat operations must be regarded as a system. In this way, only complexity theory, which Newtonian methods cannot do at all, can be used to describe, predict, and select corresponding confrontational actions. For example, the concept of “friction” often used by Clausewitz in “On War” originated from Newtonian mechanics. It can be said to be a concept of physical war, reflecting the characteristics of war in the pre-industrial era. No matter how tightly organized the army was at that time, it was inevitable to face shocks and hysteresis, frontier confrontation and confrontation. Therefore, Clausewitz used Newtonian mechanics as the main method to understand, study, and guide war. In today’s information warfare, the purpose of war has changed from “destroying the enemy and preserving oneself” to “controlling the enemy and realizing interests.” Therefore, a major change in the confrontation method is from large-scale destruction to increasing the “entropy value” within the enemy organization and increasing the “negative entropy value” within one’s own organization (“entropy” is a description of the disorder within the organization). The more information-based, integrated, and sophisticated a military is, the more vulnerable it becomes. An important principle in modern military construction is to minimize the vulnerability of its own disintegration and collapse; an important principle in war guidance is to actively create and exploit the vulnerability within the enemy.
Today, when evaluating a military system, we cannot only look at the amount of matter, energy and information it possesses, but also its anti-destruction ability, stability, and the possible “entropy value”.
(three)
Informatization and networking have broken through the traditional space boundaries and time barriers. The “pre-practice” of virtual technology has created a new military culture.
While causing a revolution in philosophical methodology, the science of complex systems has also triggered a revolution in philosophical epistemology when combined with multimedia technology, virtual reality technology, artificial intelligence technology, high-performance computing technology and simulation technology – there have been some changes in the way humans understand the world.
First, the understanding of the unity of the world is richer. In the past, when we talked about the unity of the world, we only emphasized the “primacy of matter”. From today’s perspective, the unity of the world contains three basic elements, namely the unity of matter, energy, and information. In man-made technical systems, it is the unity of materials, energy, and information; in social and economic systems, it is the unity of material flow, energy flow, and information flow. Abstracting the unity of these three aspects to the philosophical level, it colorfully embodies the “unity of matter, movement, and information.”
Secondly, the cognitive process has changed from the past “part-whole-part” to today’s “whole-part-whole”. In connection with this, the research method has changed from the past “analysis-synthesis-analysis” to today’s “synthesis-analysis-synthesis”.
Informatization and networking have broken through the traditional space boundaries and time barriers. People’s focus on observing problems has shifted from “object-centered” to “system-centered”, and the key to epistemology is no longer “concrete analysis” but “system integration”.
This new philosophical epistemology marks a major change in the structure of scientific thinking. Scientific research has shifted from the analytical advantage of the past to the overall comprehensive advantage of today; the static cognition that mainly studied “existence” in the past has shifted to the dynamic cognition that mainly studies systems today.
The significance of practice is no longer limited to the framework of history and reality, but also includes the future. After the Gulf War, developed countries established the innovative idea of ”proposing theory – combat experiment – actual military exercise – actual combat test”, stepped up the establishment of “combat laboratory”, and made new breakthroughs in military theory research methods.
Scholars such as Zhang Yi, the author of Virtual Epistemology, pointed out: “Virtual technology has profoundly changed the way humans perceive the world and created a completely new way of human practice. Virtual technology is not just a way of understanding and interpreting the world, it is itself a way of human practice.”
The “pre-practice” of virtual technology creates a new military culture. Thus, the military construction has developed from the past “contemporaneity” to today’s “synchronicity”. “Contemporaneous” development means finishing today and then moving on to tomorrow. “Synchronic” development means that things today, tomorrow and the day after tomorrow can be done at the same time. In this process, based on the repeatability, modifiability and embeddability of virtual technology, the war scenarios that are happening and will happen in the world, as well as the pre-designed war scenarios in the mind, are created into virtual environments to test and correct the military capabilities that should be in different stages.
Compared with natural science, military science is relatively weak in analytical reasoning and quantitative analysis. Summarizing the experience of wars that have already occurred and “learning war from war” have always been the traditional way for soldiers to create theories. With the development of information technology, modeling/simulation and computer networks have provided people with a third important method to understand the world, promoting the expansion of military practice from “experience induction” to “virtual simulation”, “learning war in the laboratory” and “learning war from future wars”, which greatly improves the soldiers’ advanced cognitive ability.
In short, to advance the reform of our army in the face of the new wave of military revolution, we need to establish a new philosophy, innovate military theories, and let the light of military innovation illuminate the path to the future.
現代國語:
習近平主席在中央軍委改革工作會議上強調,“要著力搶佔未來軍事競爭戰略制高點,充分發揮創新驅動發展作用,培育新的戰鬥力增長點。 ”這項重要論述深刻揭示了軍事創新在改革強軍戰略中的重要地位。
歷史一再證明,在軍事競爭過程中,誰佔據了軍事文化的製高點,誰就能引領軍事創新潮流,領先於戰爭,提前贏得戰略優勢。
當前深化國防和軍事改革與新世界軍事革命密切相關。 “在這場新世界軍事革命的浪潮中,誰保守、自滿,誰就會錯失寶貴機遇,陷入戰略被動。”習主席的話震耳欲聾,引人深思。在改革強軍過程中,每位戰士都不是旁觀者,而是創新者。面對改革,我們能否準確掌握世界軍事理論和軍事技術發展的最新動態?我們能否適應戰爭形式的最新變化?我們能否找到正確的創新路徑和方法?這些都應該是我們應該思考的問題。
文化感知世界變遷,站在改革前沿,走在時代先驅。發揮文化獨特優勢,打破千軍萬馬、百舸爭流的保守僵化思維模式,激發軍事創新活力,讓最新成果不斷湧現,打造強軍文化。
亂石飛天,海浪拍岸,在新世界軍事革命的滾滾浪潮中,誰已經甦醒,誰還在沉睡?
- 編輯
深化國防和軍事改革拉開了序幕。這次改革是在世界軍事革命浪潮洶湧澎湃的背景下進行的,是我軍發展史上的另一個里程碑。從“換棋子”到“換棋盤”,機構改革必然需要“遊戲規則”和軍事體制的改變;要求加快新組織架構的資訊化軍隊建設步伐。
新軍事革命是一個不斷創新的過程,資訊化軍隊本質上是一支創新軍隊。我們要不斷培養軍隊創新文化,增強改革活力,推動改革強軍戰略實現。
(一)
世界軍事文化發展的新趨勢要求我們在改變過程中加強文化修養,轉變軍事創新思維邏輯。
從某種意義上來說,所謂戰略願景就是認識未來的願景。伴隨著觀察領域的變化,創新思維的「典範」也隨之改變了:過去是:實務-技術-理論。現在是:理論-技術-實務。與思維「範式」的轉變相聯繫,1980年代以來,軍事創新逐漸從先前的作戰需求驅動模式轉變為「理論驅動」模式。美國著名未來學家阿爾文‧托夫勒的《第三波》、《未來戰爭》等理論著作對資訊社會、資訊戰爭及相關科技的發展發揮了巨大作用。由此,軍事創新的邏輯也發生了相對應的改變。以往的創新發展順序是:科技進步──武器裝備──軍事理論──作戰形成。目前的發展順序是:軍事理論——科技進步——武器裝備——作戰編隊。資訊時代的軍事文化使作戰指揮官和軍事理論專家成為軍事技術創新的領導者。
軍事理論專家和軍事技術專家研究發現,在西方已開發國家,現代軍事文化的演變經歷了三個階段:
在整個19世紀及以前,大多數軍人還沒有認識到科技進步對軍事力量發展的巨大推動作用。即使是像拿破崙這樣極富創新精神的軍事統帥,也輕易地拒絕了美國科學家富爾頓研發無帆戰艦的建議。從十九世紀初到第一次世界大戰,雖然工業革命革命已經影響社會的其他領域,大多數士兵沒有考慮新技術在戰爭中的作用。他們只強調使用手中現有的設備,不會考慮設備的改良和創新。這個時期被稱為士兵「等待技術」的階段。
20世紀初,高度發展的機械工業逐漸改變了士兵單純的軍事觀念。 1918年8月8日,在埃明斯戰役中,盟軍「明星」坦克的突擊威力和300架英國飛機的轟炸威力喚醒了戰壕裡的士兵。此後20年,歷史創造了一大批機械化戰爭時代的新軍事家,如富勒、杜黑、古德里安、隆美爾、蒙哥馬利、戴高樂、艾森豪威爾、朱可夫、華西列夫斯基等。他們不僅精通軍事,也了解當時坦克、飛機等新技術武器的性能特徵。他們視科學技術為第二專業,視工程師為親密朋友,在戰術發展上進行了一次又一次的創新。古德里安發明了裝甲閃電戰,羅斯福接受了愛因斯坦的建議製造原子彈,史達林則把一大批飛機設計師當作貴賓。正因為如此,二戰期間和戰後,這些國家的軍事技術和軍事學術水準都獲得了前所未有的長足發展。這段時期堪稱「軍人與科技聯姻」的階段。
自1960、70年代以來,由於微電子、人工智慧、基因工程、太空、海洋開發、新材料、新能源等新技術的快速發展,新技術革命的浪潮使許多有遠見的軍事家進一步打破原有的思維模式,提出軍人應該站在科技發展的最前沿暢想未來的作戰樣式,並基於這些設想進而提出軍事技術創新的目標和方向。軍事國防專家展望未來20至30年的發展趨勢,設計新的作戰概念,創新作戰理論,提出必要的技術支撐,然後科學研究人員從技術角度滿足新的軍事需求。軍事技術在士兵的組織和指導下,減少了發展的盲目性,從而獲得更快、更多的軍事經濟效益。這段時期可以說是軍人「技術領先」的階段。
士兵從「等技術」、「嫁技術」到「領先技術」的轉變,體現了軍事科學與科技發展關係日益密切的客觀趨勢。這種趨勢迫使士兵從技術發展的旁觀者轉變為技術發展的領導者。
在我國,由於失去了第一次工業革命的機遇,軍事文化仍處於「等待科技」和「嫁給科技」的階段。重歷史、輕未來的軍事理念,用來根據對手的今天來設計我軍的明天;它習慣於思考我們的明天的軍隊,並與今天的對手作戰。
在改革的旅程上,許多同志的思想還停留在海灣戰爭、科索沃戰爭、阿富汗戰爭、伊拉克戰爭,已經十五年、二十年了。美軍提出第三個“抵消戰略”,選擇顛覆性新技術,打造新的“非對稱軍事優勢”。新軍事革命將迎來轉捩點:一種新的戰爭形式——基於自主系統的輕型戰爭正在慢慢來臨。履行軍隊改革歷史使命、迎接新挑戰,必須加強文化修養,轉變軍事創新思維邏輯。
(二)
軍隊的文化內核,深蘊藏在軍事理念之中。在實施改革強軍戰略過程中,要運用現代科學方法進行軍事創新。
人類歷史上的每一個偉大時代,不僅賦予人們偉大的任務,也提供人們新的方法。只有明確了偉大任務、掌握了新方法,才能引領時代潮流。
科學發展史表明,許多重大科技創新以及重大科學問題的提出和解決,往往都是科學方法取得一定突破的結果。伽利略發現落體運動定律和慣性定律與他系統性地運用前驅定律是分不開的。
實驗和數學方法;達爾文創立生物演化論得益於科學觀察方法和歷史比較方法;理論實驗方法對愛因斯坦相對論的產生發揮了重要作用;馬克思的《資本論》能夠深入分析複雜的資本主義社會並取得巨大成功。其中一個重要原因是他巧妙地運用了邏輯與歷史相統一的方法以及科學抽象的方法,以「最簡單、最普遍、最基本的東西」——商品,作為邏輯和歷史的起點。著眼點,從感知的具體上升到抽象的規定,再從抽象的規定上升到思考的具體。
同樣,軍事理論的創新也首先依賴時代的新方法。中國春秋末年出版《孫子兵法》,是因為當時以「陰陽」、「五行」為代表的古代體系理論已經成熟、完整;克勞塞維茨寫《論戰爭》,是因為牛頓的力學和黑格爾的辯證法為他提供了研究戰爭的武器;毛澤東軍事思想是毛澤東同志運用馬克思主義哲學方法研究中國革命戰爭實踐的成果。
科技革命促進了社會生產力和軍事戰鬥力的提高,也促進了哲學思想的發展。
19世紀的「三大發現」(進化論、細胞學、能量守恆與轉化)導致了德國古典哲學的終結和馬克思主義哲學的出現。
20世紀,相對論、量子力學與生命科學的出現,資訊科技、生物科技、奈米科技、新材料科技、網路科技的發展,已經並將持續改變世界面貌。 1960、70年代,伴隨著新科技革命浪潮,科學方法革命達到了前所未有的高度,呈現出自然科學研究方法、方法、模型和理念向社會科學領域滲透、融合的趨勢。新的科學方法論相繼出現:系統論、控制論、協同論、突變論、資訊理論、離散論、泛函論、智能論、最優化論、反應論、模糊論、藝術論,以及「混沌論」。 」和「分形」。從哲學的角度來看,這些跨學科學科所提出的方法可以歸納為系統方法和複雜系統方法。
1958年,美軍實行軍政軍指揮分離後,並沒有很快恢復活力。五角大廈的資源管理一片混亂,仍處於岌岌可危的境地。 1960年,麥科納馬拉接管國防部。針對三軍獨立使用國防資源的混亂局面,他於1962年提出「集中指導與分散實施相結合」的管理原則,採用系統工程方法,統籌規劃國家國防資源。規劃和預算系統(PPBS)”,理順了美軍建設的關係,節省了資源。
1986年,美軍實施了《國防部改革法案》,將國防部和參謀長聯席會議的權力集中起來,建立了一套集權與授權相統一的新法規。這保證了聯合作戰的順利實施,為今後一體化聯合作戰奠定了基礎。
21世紀初,拉姆斯菲爾德擔任國防部長時,根據新軍事革命的發展,美軍改變了PPBS系統基於目標任務的管理習慣,提出了基於能力需求的PPBE系統,即「規劃、規劃、預算和執行系統」。
PPBS體系和PPBE體係都是系統科學方法在國防管理的典型應用。從方法論來看,這些體系的特點是:從未來掌握現實,根據任務任務確定能力,根據能力需求驅動技術創新和選擇作戰編隊。簡而言之,“上游”決定“下游”,“頂部”決定“底部”,“前端”決定“後端”。
系統論和複雜性方法的想法已經深入人心應用於美軍轉型。他們認為,以往的軍事理論,即克勞塞維茨、約米尼等著名學者的理論,都是以牛頓力學為基礎的。在今天的作戰中,必須把敵方的軍事組織和作戰行動視為一個系統。這樣,就只能用牛頓方法根本無法做到的複雜性理論來描述、預測和選擇相應的對抗動作。例如,克勞塞維茨在《戰爭論》中經常使用的「摩擦」概念就源自於牛頓力學。可以說是物理戰爭的概念,反映了前工業時代戰爭的特徵。無論當時的軍隊組織得多麼嚴密,都不可避免地要面臨衝擊和滯後、邊疆對峙和對抗。因此,克勞塞維茨以牛頓力學為主要方法來認識、研究和指導戰爭。當今資訊化戰爭,戰爭目的已從「消滅敵人、保存自己」轉變為「制敵、實現利益」。因此,對抗方式的一個重大變化就是從大規模破壞,轉向增加敵方組織內部的「熵值」和增加己方組織內部的「負熵值」(「熵」是對組織內部混亂的描述)。 )。軍隊越是資訊化、一體化和複雜化,它就越容易受到攻擊。現代軍事建設的一個重要原則就是盡量減少自身瓦解和崩潰的脆弱性;戰爭指導的一個重要原則是積極創造和利用敵人內部的弱點。
今天,評價一個軍事系統,不僅要看它所擁有的物質、能量和資訊的多少,還要看它的抗破壞能力、穩定性以及可能存在的「熵值」。
(三)
資訊化、網路化突破了傳統的空間界限和時間障礙。虛擬技術的「預實踐」創造了新的軍事文化。
複雜系統科學在引發哲學方法論革命的同時,與多媒體技術、虛擬實境技術、人工智慧技術、高效能運算技術、模擬技術結合,也引發了哲學知識論的革命——在知識論上發生了一些變化。人類理解世界的方式。
一是對世界統一的認識更加豐富。過去,我們在談論世界的統一性時,只強調「物質的首要性」。從今天的角度來看,世界的統一包含三個基本要素,即物質、能量、資訊的統一。在人造技術系統中,它是物質、能量和資訊的統一體;在社會經濟系統中,它是物質流、能量流、資訊流的統一。將這三方面的統一抽像到哲學層面,豐富多彩地體現了「物質、運動、資訊的統一」。
其次,認知過程從過去的「部分-整體-部分」轉變為今天的「整體-部分-整體」。與此相聯繫,研究方法也從過去的「分析-綜合-分析」轉變為今天的「綜合-分析-綜合」。
資訊化、網路化突破了傳統的空間界限和時間障礙。人們觀察問題的焦點從“以物件為中心”轉向“以系統為中心”,認識論的關鍵不再是“具體分析”而是“系統整合”。
這種新的哲學認識論標誌著科學思維結構的重大變化。科學研究從過去的分析優勢轉向今天的整體綜合優勢;過去主要研究「存在」的靜態認知已經轉向今天主要研究系統的動態認知。
實踐的意義不再侷限於歷史和現實的框架,也包括未來。海灣戰爭後,已開發國家確立了“提出理論——實戰實驗——實戰演練——實戰檢驗”的創新思路,加緊建立“實戰實驗室”,軍事理論研究方法取得新突破。
《虛擬知識論》一書作者張毅等學者指出:「虛擬技術深刻改變了人類感知世界的方式,創造了人類全新的實踐方式。虛擬技術不僅僅是一種理解和解釋世界的方式,它本身就是人類實踐的一種方式。
虛擬技術的「預實踐」創造了新的軍事文化。由此,軍隊建設從過去的“同時性”發展到今天的“同步性”「同步」開發是指完成今天,然後走向明天。嵌入性,將世界上正在發生和將要發生的戰爭場景,以及腦海中預先設計的戰爭場景,創建到虛擬環境中,以測試和修正不同階段應有的軍事能力。
與自然科學相比,軍事科學在分析推理和定量分析方面相對較弱。總結已經發生的戰爭經驗,“從戰爭中學習戰爭”,一直是軍人創造理論的傳統方式。隨著資訊科技的發展,建模/模擬和電腦網路為人們提供了認識世界的第三種重要方法,推動軍事實踐從「經驗歸納」向「虛擬模擬」、「在實驗室學習戰爭」拓展「從未來戰爭中學習戰爭”,大大提高了士兵的高級認知能力。
總之,面對新一輪軍事革命浪潮,推進我軍改革,需要建立新理念,創新軍事理論,讓軍事創新之光照亮未來之路。
中國原創軍事資源:http://theory.people.com.cn/n1/2016/0112/c49150-28040888.html