信息安全技術-個人信息安全規範 –
China’s “Information Security Technology Personal Information Security Specification” in Four Aspects
On December 11th, 2017, there were two kinds of mobile phone APPs, Baidu and Baidu, which were owned by Baidu. They included “listening phone”, “reading short MMS”, “reading contacts”, etc. involving consumer personal information. In the case of security related rights and refusal to rectify the situation, the Jiangsu Provincial Consumer Protection Committee initiated a consumer civil public interest litigation concerning suspected illegal access to consumer personal information and related issues by Beijing Baidu.com, which was held on January 2 of this year in Nanjing. The Intermediate People’s Court has formally opened the case. On January 6th, with the fermentation of Alipay’s annual billing event, the State Administration of Cybernetics Network Security Coordination Bureau interviewed relevant persons in charge of Alipay (China) Network Technology Co., Ltd. and Sesame Credit Management Co., Ltd. and pointed out that Alipay, The way in which sesame credits collect personal information does not conform to the spirit of the National Standard for Information Security Technology and Personal Information Security. It violates the promise of the Personal Information Protection Initiative that it signed shortly and should strictly follow the Cyber Security Law. The following is called the “net security law” requirements, strengthen the comprehensive investigation of the platform, carry out special rectification, and take effective measures to prevent similar incidents from happening again. Since the official implementation of the “Network Security Law”, the National People’s Congress, Industry and Information Technology, Internet Information, Internet Security, and Consumers’ Association systems have launched a series of special inspections and rectifications of personal information throughout the country. At the same time, they have also strengthened punishments for violations of laws and regulations. The public’s emphasis on the protection of personal information.
However, because of the principle, fuzziness and fragmentation of legal norms and local regulatory policies, many articles lack detailed rules for landing, which brings great confusion to many network operators’ personal information compliance work. On December 29 last year, the China National Standardization Administration officially issued the “Information Security Technology Personal Information Security Specification” (hereinafter referred to as the “Safety Code”). On January 24, the national standard full-text publication system officially announced the full text of the specification, and It will be implemented on May 1, 2018. The “Safety Code” clarifies the compliance requirements for the collection, preservation, use, and sharing of personal information in the form of national standards, and provides guidelines for network operators to formulate privacy policies and improve internal controls.
”Safety Regulations”
Related legal concepts
Based on the existing principles and provisions of the “Net Security Law”, the “Safety Regulations” specifies the specific definitions of relevant legal concepts in light of the specific issues that network operators are concerned about in practice.
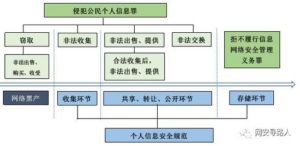
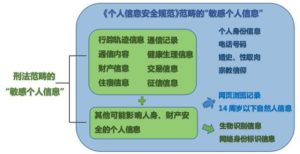
First, regarding personal sensitive information, the “Guide to the Protection of Personal Information in Information and Security Technology Public and Commercial Service Information Systems” implemented in 2013 defined personal sensitive information as personal information that would adversely affect the personal information subject after being exposed or modified. At the same time, it is recommended that the specific content of personal sensitive information in various industries be determined based on the willingness of the personal information subject to the service and their respective business characteristics. The “Safety Regulations” further emphasizes in the definition that the disclosure of personal sensitive information, illegal provision or misuse may endanger the safety of people and property, cause personal reputation, physical and mental health damage or discriminatory treatment and other serious consequences, and in Appendix B A specific example of personal sensitive information was drawn up, linking up with the data classification obligations stipulated in Article 21 of the “Network Security Law”.
Secondly, regarding the collection of personal information, the “Safety Regulations” defines three types of “collection” as the provision of personal information subjects, automatic collection by network operators, and indirect acquisition from third parties. At the same time, exceptions are stipulated and individuals are acquired at terminals. Information not returned to the operator’s server does not belong to “collection.”
Finally, with respect to the anonymization and de-identification of personal information, the “Safety Code” distinguishes the two. The anonymized information cannot be restored and is no longer part of personal information; de-identification processing guarantees Personal information can’t identify the main body of information without relying on additional information, but it still retains the granularity of the individual and uses pseudonyms, encryption, hash functions, etc. instead of the original personal information. In addition, on August 15 last year, the “Information Security Technology Personal Information De-identification Guide” was released for solicitation of public opinions. The contents involved the process of de-identification and technical applications. Currently, the network operators are implementing the personal information during the review stage. Marking work is worth learning from.
Collection of personal information
The “Safety Regulations” stipulates that the collection of personal information should comply with the requirements of legality and minimization. Among them, the requirements for authorization to obtain personal information indirectly and the explicit consent requirements for collecting personal sensitive information are worthy of attention.
When obtaining personal information indirectly, the company as the recipient is obliged to require the provider to explain the source of the relevant personal information and confirm its legitimacy. At the same time, it should also understand the scope of the personal information subject’s authorization to the provider, including the purpose of use and the individual. Whether the information subject is authorized to consent to the transfer, sharing, public disclosure, etc. If the recipient handles personal information beyond the above-mentioned range, it shall also obtain the explicit consent of the personal information subject within a reasonable time limit. Establishing an authorization consent model for indirect collection of personal information is one of the highlights of the Personal Information Collection section of the “Safety Code”. This model reinforces the review obligation of information receivers and increases the corresponding compliance costs.
In the collection of personal sensitive information, first of all, the “Safety Code” further requires the express consent of the personal information subject on the basis of the “Net Security Law” to be a voluntary, concrete, clear and clear wish given by the individual on the basis of full knowledge. Representation; Second, if the personal information controller collects personal sensitive information for the core business functions of its products or services, it shall explicitly inform the information subject of the core business functions it provides, the personal sensitive information it needs to collect, and the personal information subject. Three choices of rights; Finally, if personal information controllers collect personal sensitive information for other additional functions, they should clearly inform specific additional functions and the right to choose personal information, but refuse personal sensitive information required for additional functions. It does not mean that the core business functions have stopped providing.
Sharing of personal information
When entrusting a third party to process personal information, apart from the fact that the commissioning itself must not exceed the scope of the authorized consent of the personal information subject, the “Safety Code” also stipulates that the personal information controller should carry out personal information security impact assessment and take the responsibility of the contract. Obligation, auditing, etc. supervise the trustee and ensure accurate recording and preservation of the trustee’s handling of personal information.
With respect to the sharing and transfer of personal information, the “Safety Code” also stipulates the obligations of the personal information controller on the security impact assessment. At the same time, the personal information controller shall notify the personal information subject of the purpose of sharing, transferring the personal information, and the type of the data receiver. In the case of personal sensitive information, the type of sensitive information, the identity of the recipient of the data, and the security capabilities should also be notified, and sharing or transfer may be made only after obtaining the explicit consent of the personal information subject. In addition, personal information controllers need to accurately record and preserve the sharing and transfer of personal information, and bear the legal responsibility for the harm caused by sharing and transferring personal information to the legitimate rights and interests of the information subject. Where changes in the controlling body occur due to mergers and acquisitions, restructuring, etc., they shall individually notify the subject of personal information.
With regard to the cross-border transmission of personal information, the “Safety Code” requires that personal information controllers should conduct security assessments in accordance with the standards set by the Network Information Office and relevant departments. According to the “Personal Information and Important Data Outbound Security Assessment Methodology (Exposure Draft)” published in April last year, network operators should organize their own data outbound security assessment before leaving the country and be responsible for the results if they contain or accumulate 500,000. If the personal information above the person or the personal information provided by the key information infrastructure is provided to the outside, it shall also be reported to the industry supervisor or the supervisory authority for organizing the safety assessment. The Guidelines for Outbound Security Assessment of Information Security Technology Data (Draft for Solicitation of Comments) (hereinafter referred to as the “Evaluation Guide”) issued by the National Information Security Standardization Technical Committee on August 30 last year are also worthy of attention. The Assessment Guide clearly indicates the data. The use scope and exceptions of outbound security assessments are to refine the types of personal information and important data, increase the disclosure obligation of network operators for personal information, distinguish security self-assessment and assessment processes of competent authorities, and implement personal information for personal information controllers. Cross-border transmission provides a reference.
Safety management requirements
Since its implementation, NetEase has given network operators many security protection obligations. One of them is the development of internal security management systems and operational procedures to implement the network security protection responsibilities. Specifically, the “security regulations” include three. Aspects. First, the responsible departments and personnel should be clarified. According to the “Safety Regulations”, personal information controllers that meet certain conditions in terms of business, personnel scale, and personal information processing volume should establish full-time personal information protection managers and work agencies so that The specific implementation of personal information security work prevents personal information from being leaked, damaged or lost. Second, a personnel management and training system should be established. According to the “Safety Regulations”, personal information controllers should sign confidentiality agreements with employees engaged in personal information processing positions and conduct background checks to clarify the safety responsibilities of related positions and the occurrence of security incidents. Penalty mechanism, while conducting regular professional training and assessment, to ensure that relevant employees have the privacy policy and regulatory processes. Third, a personal information security impact assessment and audit system should be developed to assess potential risks and adverse impacts in the processing of personal information, form an assessment report for inspection by relevant parties, and establish an automated auditing system to monitor and record personal information processing activities. Handle the illegal use and abuse of personal information in the audit process in a timely manner.
Conclusion
The formal issuance of the “Safety Code” ended the situation in which there were many personal information protection principles and the lack of specific measures since the implementation of the “Net Security Law.” This answer the confusion of the Internet companies, and in the appendix, it is the subject of personal information. The agreed-upon functional interface and privacy policy templates have provided a complete compliance and risk control policy for the provision of network products and services. Although the “Safety Code” number is displayed as a national recommendation, in practice, the review of the privacy policy conducted by the four departments of the Network Information Office, the Ministry of Industry and Information Technology, and the Ministry of Public Security last year was mainly based on the “Safety Regulations” solicitation opinion draft. When the Information Office interviewed Alipay about the annual billing event, it also emphasized the validity of the “Safety Regulations.” These events all reflected the importance of the “Safety Rules” for improving the personal information protection system. The majority of network operators should make efforts to collect, save, use, and share personal information, improve internal management and privacy policy formulation to cope with the rigorous regulatory situation.
Original Mandarin Chinese:
2017年12月11日,就百度旗下“手機百度”、“百度瀏覽器”等兩款手機APP存在“監聽電話”、“讀取短彩信”、“讀取聯繫人”等涉及消費者個人信息安全的相關權限且拒不整改的情形,江蘇省消費者權益保護委員會就北京百度網訊科技有限公司涉嫌違法獲取消費者個人信息及相關問題提起消費民事公益訴訟,今年1月2日,南京市中級人民法院已正式立案。 1月6日,隨著“支付寶年度賬單事件”的發酵,國家網信辦網絡安全協調局約談了支付寶(中國)網絡技術有限公司、芝麻信用管理有限公司的有關負責人並指出,支付寶、芝麻信用收集使用個人信息的方式,不符合《信息安全技術個人信息安全規範》國家標準的精神,違背了其前不久簽署的《個人信息保護倡議》的承諾,應嚴格按照《網絡安全法》(以下稱“《網安法》”)的要求,加強對平台的全面排查,進行專項整頓,切實採取有效措施,防止類似事件再次發生。自《網安法》正式實施以來,人大、工信、網信、網安以及消協系統,在全國各地掀起了一系列個人信息專項檢查、整治行動,處罰違法違規行為的同時,也加強了社會公眾對個人信息保護的重視程度。
然而,由於法律規範及各地監管政策的原則性、模糊化及碎片化,很多條文缺乏落地的細則,這就給很多網絡運營者個人信息合規工作帶來極大的困惑。去年12月29日,中國國家標準化管理委員會正式發布《信息安全技術個人信息安全規範》(以下稱“《安全規範》”),1月24日,國家標準全文公開系統正式對外公佈規範全文,並將於2018年5月1日起實施。 《安全規範》以國家標準的形式,明確了個人信息的收集、保存、使用、共享的合規要求,為網絡運營者制定隱私政策及完善內控提供了指引。
《安全規範》的具體規定
相關法律概念
《安全規範》在《網安法》已有的原則性規定的基礎上針對網絡運營者在實踐中關注的具體問題,明確了相關法律概念的具體定義。
首先,關於個人敏感信息,2013年實施的《信息安全技術公共及商用服務信息系統個人信息保護指南》將個人敏感信息定義為在遭受洩露或修改後會對個人信息主體造成不良影響的個人信息,同時建議各行業個人敏感信息的具體內容根據接受服務的個人信息主體意願和各自業務特點確定。 《安全規範》則在定義中進一步強調了個人敏感信息被洩露、非法提供或濫用可能危害人身、財產安全,致使個人名譽、身心健康受到損害或歧視性待遇等嚴重後果,並在附錄B中給出了個人敏感信息的具體示例,銜接了《網安法》第二十一條規定的數據分類義務。
其次,關於個人信息的收集,《安全規範》將個人信息主體主動提供、網絡運營者自動採集以及從第三方間接獲取等三種方式定義為“收集”,同時規定了例外情形,在終端獲取個人信息但不回傳至運營者服務器的,不屬於“收集”。
最後,關於個人信息的匿名化與去標識化,《安全規範》將兩者區別開來,經匿名化處理後的信息無法復原,也不再屬於個人信息之列;而去標識化處理則保證了個人信息在不借助額外信息的情況下,無法識別信息主體,但依舊保留了個人顆粒度,採用假名、加密、哈希函數等手段替代了原有個人信息的標識。此外,去年8月15日,《信息安全技術個人信息去標識化指南》徵求意見稿發布,內容涉及去標識化的過程及技術應用等,目前已在送審階段,網絡運營者在落實個人信息去標識化工作時值得借鑒。
個人信息的收集
《安全規範》規定個人信息收集應遵循合法性要求和最小化要求,其中,間接獲取個人信息的授權同意要求和收集個人敏感信息的明示同意要求值得關注。
在間接獲取個人信息時,作為接收方的企業有義務要求提供方對相關個人信息的來源進行說明並確認其合法性,同時還應當了解個人信息主體對於提供方的授權範圍,包括使用目的、個人信息主體是否授權同意轉讓、共享、公開披露等內容,若接收方處理個人信息超出上述範圍的,還應在合理期限內另行徵得個人信息主體的明示同意。確立間接收集個人信息的授權同意模式是《安全規範》有關個人信息收集部分的亮點之一,這一模式強化了信息接收方的審查義務,增加了相應的合規成本。
在收集個人敏感信息方面,首先,《安全規範》在《網安法》的基礎上進一步要求個人信息主體的明示同意是其在完全知情的基礎上自願給出的、具體的、清晰明確的願望表示;其次,若個人信息控制者收集個人敏感信息用於其產品或服務的核心業務功能,則應當明確告知信息主體其所提供的核心業務功能、所需收集的個人敏感信息和個人信息主體的選擇權三項內容;最後,若個人信息控制者收集個人敏感信息用於其他附加功能的,則應當明確告知具體的附加功能和個人信息主體的選擇權,但拒絕附加功能所需的個人敏感信息並不意味著核心業務功能的停止提供。
個人信息的分享
在委託第三方處理個人信息時,除委託行為本身不得超出個人信息主體授權同意的範圍之外,《安全規範》還明確規定,個人信息控制者應當開展個人信息安全影響評估,並採取合同約定責任義務、審計等方式對受託者進行監督,保證準確記錄和保存受託者處理個人信息的情況。
關於個人信息的共享與轉讓,《安全規範》同樣規定了個人信息控制者的安全影響評估義務,同時個人信息控制者應當向個人信息主體告知共享、轉讓個人信息的目的、數據接收方類型,涉及個人敏感信息的,還應當告知敏感信息的類型、數據接收方的身份和安全能力等,在事先徵得個人信息主體明示同意後方可共享或轉讓。此外,個人信息控制者需準確記錄和保存個人信息共享和轉讓情況,承擔因共享、轉讓個人信息對信息主體合法權益造成損害的法律責任。因併購、重組等發生控制主體變更的,應當單獨向個人信息主體告知有關情況。
關於個人信息的跨境傳輸,《安全規範》要求個人信息控制者應按照網信辦會同相關部門製定的標准進行安全評估。根據去年4月發布的《個人信息和重要數據出境安全評估辦法(徵求意見稿)》,網絡運營者在數據出境前應自行組織數據出境安全評估,並對結果負責,若含有或累計含有50萬人以上個人信息以及由關鍵信息基礎設施對外提供個人信息的,還應報請行業主管或監管部門組織安全評估。去年8月30日由全國信息安全標準化技術委員會公佈的《信息安全技術數據出境安全評估指南(徵求意見稿)》(以下稱“《評估指南》”)同樣值得關注,《評估指南》明示了數據出境安全評估的使用範圍及例外,細化個人信息及重要數據的類型,增加了網絡運營者個人信息出境的告知義務,區分安全自評估與主管部門評估流程,為個人信息控制者俱體落實個人信息跨境傳輸提供了參考依據。
安全管理要求
《網安法》自實施以來,賦予了網絡運營者諸多安全保護義務,其中之一便是製定內部安全管理制度和操作規程,落實網絡安全保護責任,具體到《安全規範》中,主要包括三個方面。第一,應當明確責任部門與人員,根據《安全規範》,在業務、人員規模、個人信息處理量等方面滿足特定條件的個人信息控制者,應設立專職的個人信息保護負責人和工作機構以便個人信息安全工作的具體實施,防止個人信息的洩露、損毀、丟失。第二,應當構建人員管理與培訓制度,根據《安全規範》,個人信息控制者應當與從事個人信息處理崗位的員工簽署保密協議並進行背景審查,明確相關崗位的安全職責和發生安全事件後的處罰機制,同時定期開展專業化培訓和考核,確保相關員工掌握隱私政策和規章流程。第三,應當開展個人信息安全影響評估與審計製度,評估個人信息處理過程中可能產生的風險與不利影響,形成評估報告以供相關方查閱,同時建立自動化審計系統,監測記錄個人信息處理活動,及時處理審計過程中個人信息違規使用、濫用等情況。
結語
《安全規範》的正式發布結束了《網安法》實施以來個人信息保護原則性規定較多而具體措施欠缺的局面,解答了廣大互聯網企業的困惑,其在附錄部分更是製作了個人信息主體授權同意的功能界面和隱私政策的模板,使得網絡產品和服務的提供有了完備的合規和風控政策。雖然《安全規範》編號顯示為國家推薦標準,但在實踐中,去年網信辦、工信部、公安部等四部門開展的隱私政策評審工作主要以《安全規範》徵求意見稿為依據,今年年初網信辦就年度賬單事件約談支付寶時,也再次強調了《安全規範》的準據效力,上述事件均從側面反映了《安全規範》對於完善個人信息保護製度的重要性。廣大網絡運營者應發力個人信息的收集、保存、使用、分享等多個方面,完善內部管理與隱私政策制定,以應對趨於嚴格的監管形勢。
Source: http://new.qq.com/omn/20180201/20180201B07GLP.htm